Name cannot be blank
371 posts



🧵 How does an off-the-shelf car GPS jammer work?
A short thread.
There are many ways to perform radio signal jamming (and also detect or protect against it), however the most basic concept is this: a jammer saturates the input of the target's receiver system by noise, in a way that it can't receive/detect/decode the desired radio signal anymore. It reduces the signal to noise ratio.
It's like if you want to listen to someone, but I shout at you in close proximity, so you can't hear that person. (I hope experts don't shout at me for this simplistic example)
There are many legal and illegal use cases for a jammer: military, law enforcement, car theft, protection against tracking etc.
1/4

English
In the past year I've seen SO many weird permissions granted to the "Domain Computers" group in environments. Always check outbound control from this group!
See below for how to gain "Domain Computers" permissions, for later exploitation (with many links from @_nwodtuhs):
English

I've been playing around with Module Stomping for EDR Evasion
This is a cool technique for bypassing detection by overwriting "legitimate" memory regions.
Let's see what it looks like from a #Malware and RE Perspective
@SEKTOR7net
[1/25]




English

Hey, @SteveAngello. Big fan. Is there any chance "Sentido" is still alive?
English
Name cannot be blank retweetet
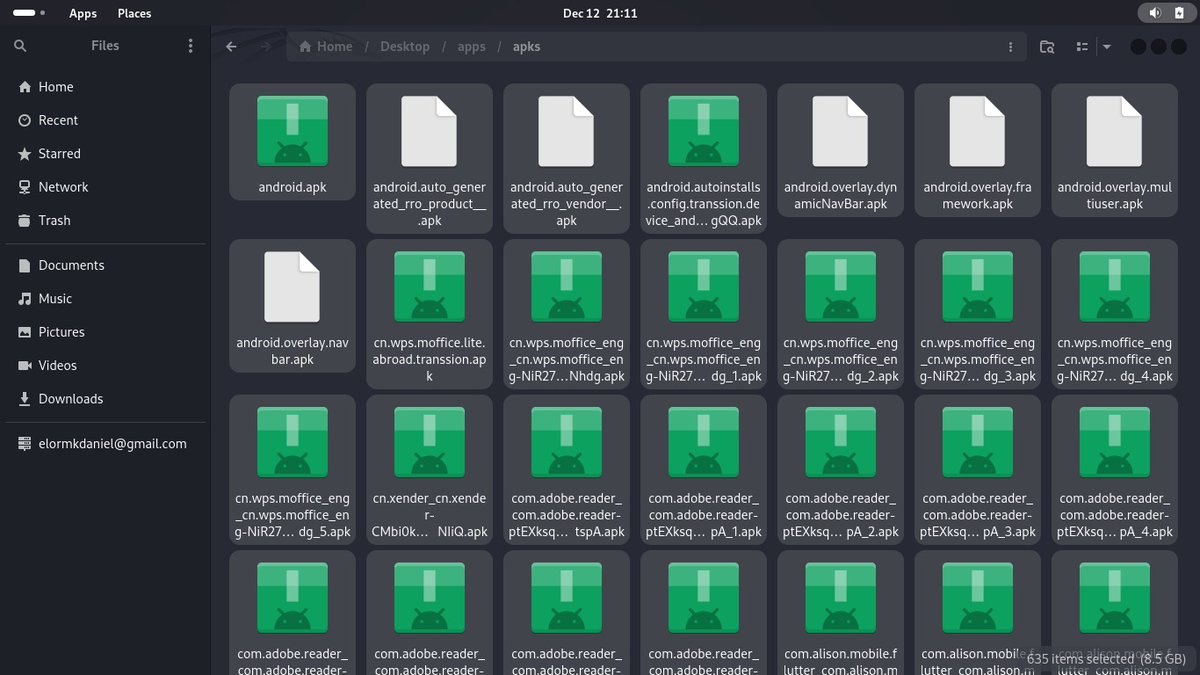
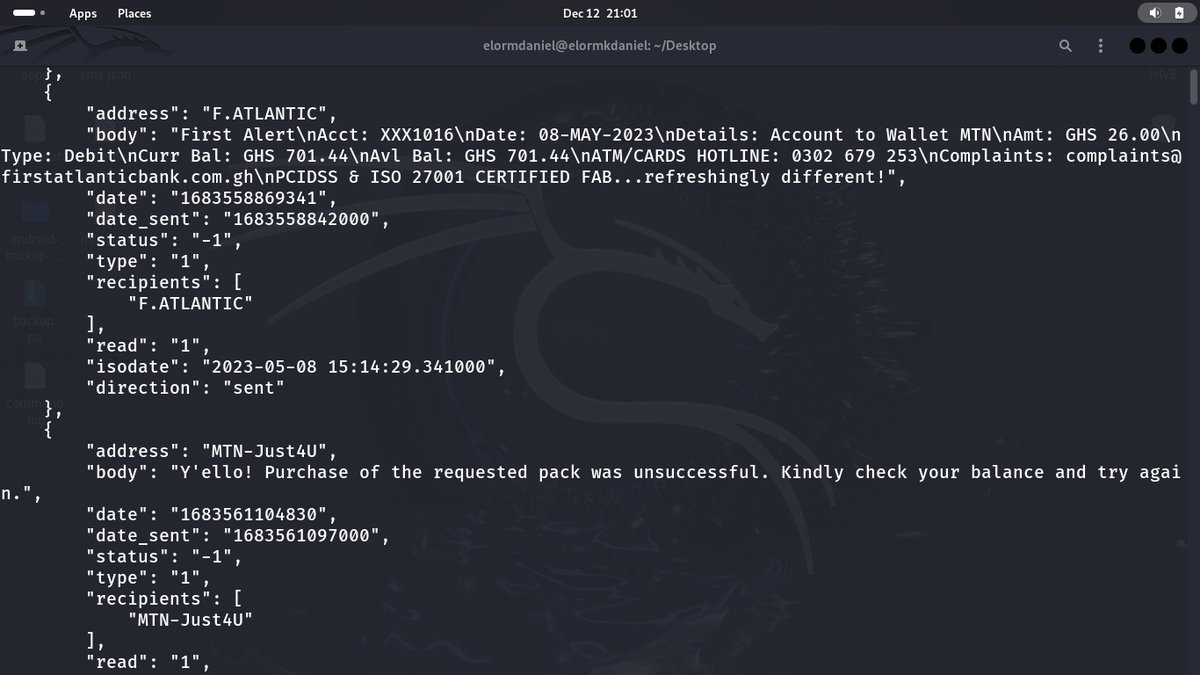
That DIT is going to take forever to exfiltrate. Better to strip the hashes out and exfiltrate those instead.
github.com/Dionach/NtdsAu…
ntdsAudit.exe '.\Active Directory\ntds.dit' -s registry\SYSTEM -p pwddump.txt -u users.csv
Its c#, so you can reflectively load it in PS, too.
Grzegorz Tworek@0gtweet
Did you spot something like: ntdsutil "activate instance ntds" "ifm" "create full c:\somerandompath" q q on your DC? You are in huge trouble... BTW it creates the folder you specify as path.
English
Name cannot be blank retweetet

I really enjoyed testing @C5pider's Havoc C2 framework. Wrote a little blogpost, on how to set it up & exploit a fully patched Win11 machine:
payload.cafe/2022/10/02/hav…
Video: youtu.be/pso2LAONCJ8

YouTube
English

@joetidy not to brag, but we could've stopped that from happening @RoyalMail
English
Name cannot be blank retweetet
Name cannot be blank retweetet
Name cannot be blank retweetet

@nas_bench I must have missed an episode, which c2 framework was leaked?
English

@Alh4zr3d Or, you could go Internal-Monologue or Masky (ADCS required) way.
English
Name cannot be blank retweetet

"Tools such as PC Hunter (which grants access to system processes, kernel modes, and hooks), GMER (which detects and removes rootkits) and Revo Uninstaller (which can uninstall apps and programs) also terminate programs and antimalware solutions."
3/4
trendmicro.com/vinfo/us/secur…
English