Post

@Jamwanda2 Even you are against it but mungadii muri pabasa 😀
Indonesia
@Jamwanda2 The jingles on zbc and radio stations won't change the people's minds.
English

@Jamwanda2 Takazviona izvi pa time ya Mugabe, even mu Zanupf hamuna consensus kune varikutodawo various offices in 2028 from Cllrs kusvika panyanga chaipo. 24hrs is long a time in politics

@Jamwanda2 @admusinga ZANU-PF will always win because it controls all the levers of power. We are helpless and at its mercy. Even changing the entire Constitution to suit its desires is possible. This is how dangerous it becomes when power rests in the hands of cruel people.
English

@Jamwanda2 You're good at inflicting pain. Your turn is coming. CAB3 will not succeed. You will not succeed.
English

@Jamwanda2 @TendayiZinyama Imi makanaka cheroo hurumende yauya muri pabasa. Language yenyu chero pana Mugabe maingodai
Filipino

@Jamwanda2 Mahwinha Postponing succession bambo. But ED is in his twilight saka makatodyiwa nedare. Fate will fix everything. achangobaya...natural attrition chababa.
English

@Jamwanda2 Its not winning kunonzi kumbunyikidza zvido zvepovho nekushandisa chisimba.

@Jamwanda2 Why murikuti mahwina? Ticida kungotarisa pano cete hapana kana one akukutsigirai
Indonesia

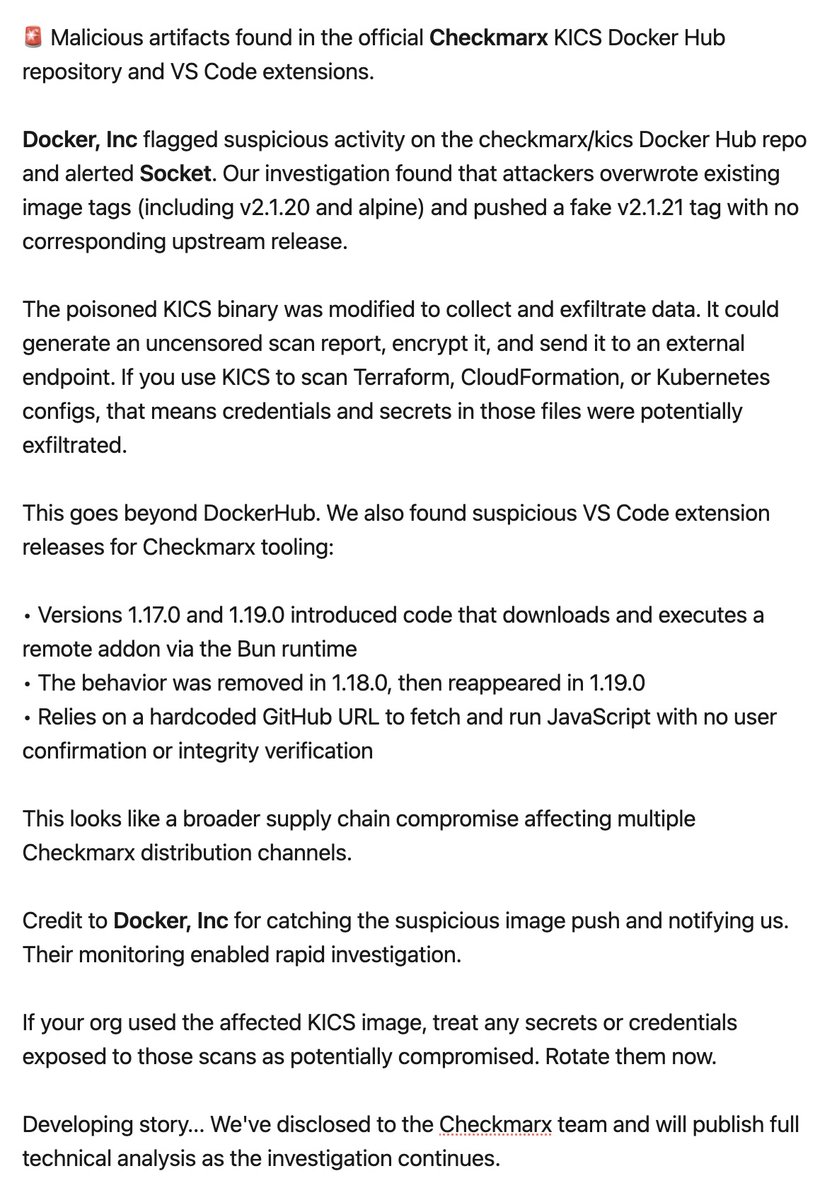
🚨 DEVELOPING STORY: Malicious artifacts found in the official @Checkmarx KICS Docker Hub repository and VS Code extensions.
@Docker flagged suspicious activity on the checkmarx/kics Docker Hub repo and alerted Socket. Our investigation found that attackers overwrote existing image tags (including v2.1.20 and alpine) and pushed a fake v2.1.21 tag with no corresponding upstream release.
The poisoned KICS binary was modified to collect and exfiltrate data. It could generate an uncensored scan report, encrypt it, and send it to an external endpoint. If you use KICS to scan Terraform, CloudFormation, or Kubernetes configs, that means credentials and secrets in those files were potentially exfiltrated.
This goes beyond DockerHub. We also found suspicious VS Code extension releases for Checkmarx tooling:
• Versions 1.17.0 and 1.19.0 introduced code that downloads and executes a remote addon via the Bun runtime
• The behavior was removed in 1.18.0, then reappeared in 1.19.0
• Relies on a hardcoded GitHub URL to fetch and run JavaScript with no user confirmation or integrity verification
This looks like a broader supply chain compromise affecting multiple Checkmarx distribution channels.
Credit to Docker for catching the suspicious image push and notifying us. Their monitoring enabled rapid investigation.
If your org used the affected KICS image, treat any secrets or credentials exposed to those scans as potentially compromised. Rotate them now.
Developing story... We've disclosed to the Checkmarx team and will publish full technical analysis as the investigation continues.
English



