BLAKE3-team retweeted

To support content-addressed data transfer in @iroh_n0, we have been relying on a @Blake3Team fork for quite some time.
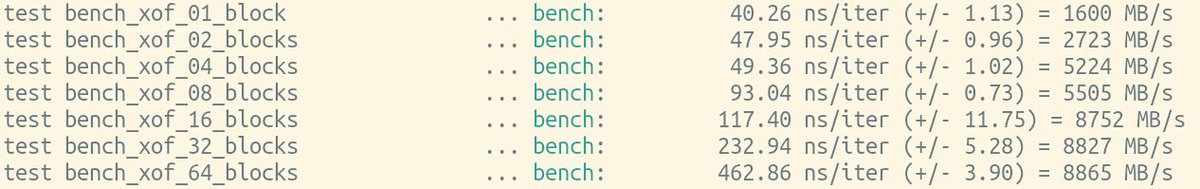
Not anymore. Thanks to @oconnor663, there is now a nice new hazmat API that has exactly what we need, and more.
For details: iroh.computer/blog/blake3-ha…
English