David Collins
14.7K posts


David Collins
@ColliCryptoboy
Web 3 Enthusiasts: Builder/ Front-end developer
Joined Kasım 2024
2.2K Following163 Followers
David Collins retweeted

Yesterday’s @colosseum Frontier Hackathon Co working session with my @SuperteamNG family was a blast 😇
We had great session going over our projects, got valuable feedbacks and shared our progress
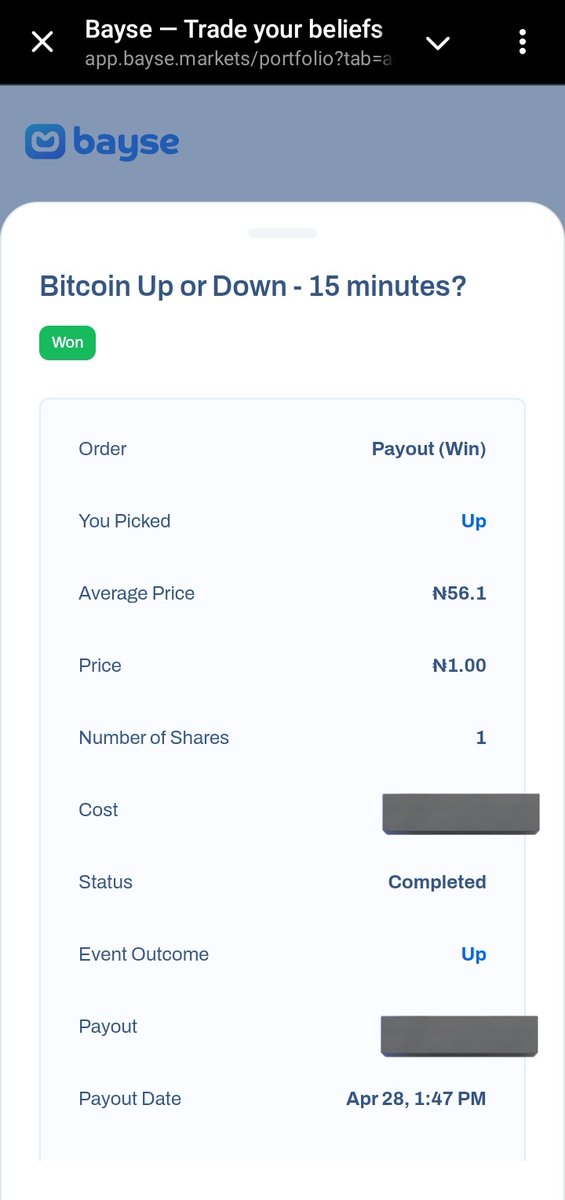
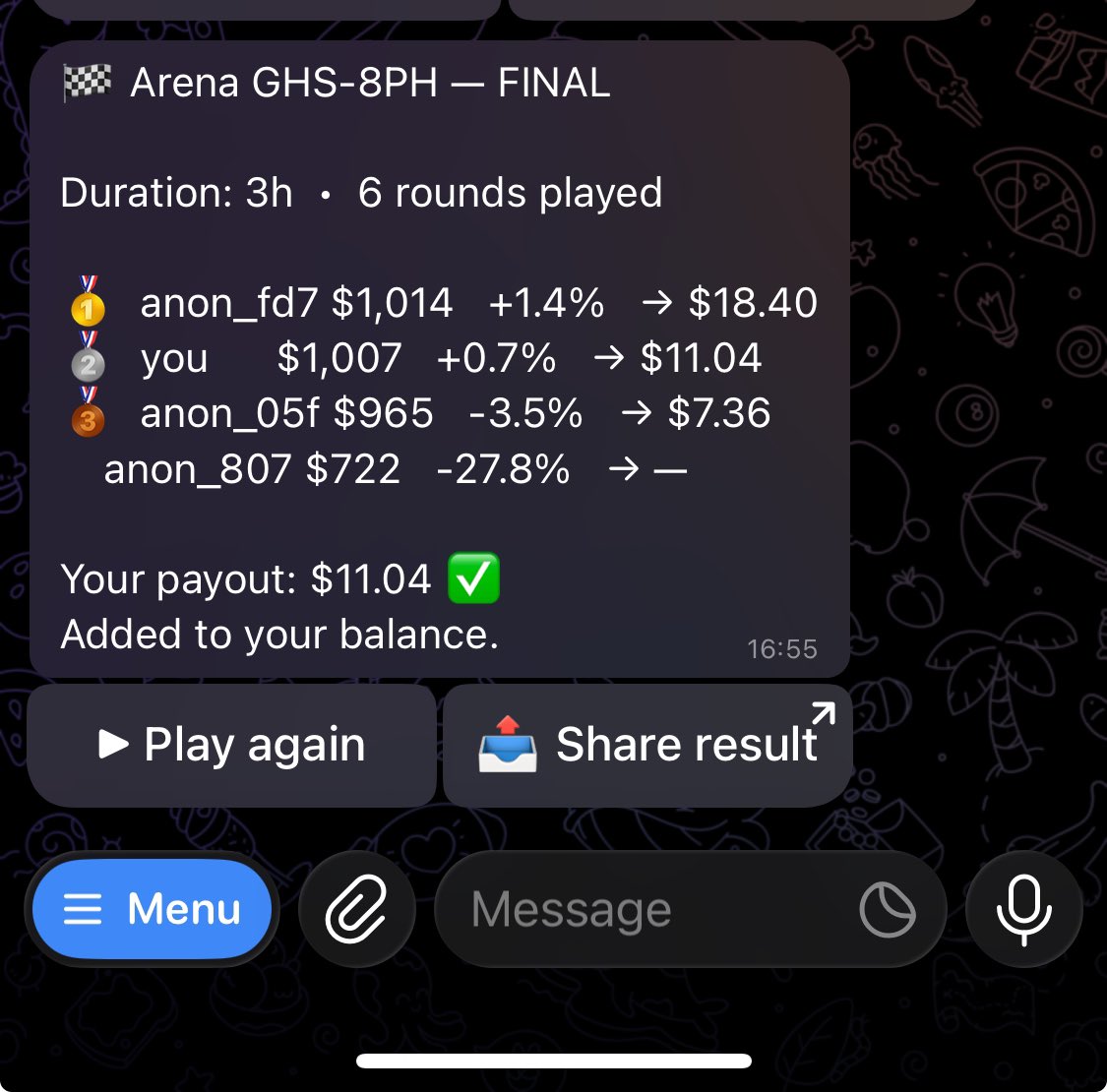
Played 2 rounds of Bayse Fantasy arena with the community and they loved the game and the approach we are taking at @headlineodds
I came 4th and lost my wager to @CallMi_Alex_ @Tobi_Builder and @rolandayd 😅
Solana builders are shipping incredible projecs and i’m always proud to be part of this
Solana will keep winning. We will all make sure of that.
Ecosystem call up next. ✌️




English
David Collins retweeted

@bioduncrypt @colosseum @SuperteamNG @solana Crazy how we’re building during the day and competing right after 😅
Bayse Arena was fun but also tells you a lot about decision making under pressure
Secured my win on that end too 😅
English
David Collins retweeted

Ghidra Agent is now available in Neo.
- Malware analysis.
- Patch diffing.
- CVE reversing.
- Firmware research.
All of it - just by talking to @neo_ai_engineer
See it reverse Mirai live 👇
neo.projectdiscovery.io/share/ccb479cd…

English
David Collins retweeted

[NEW BLOG]
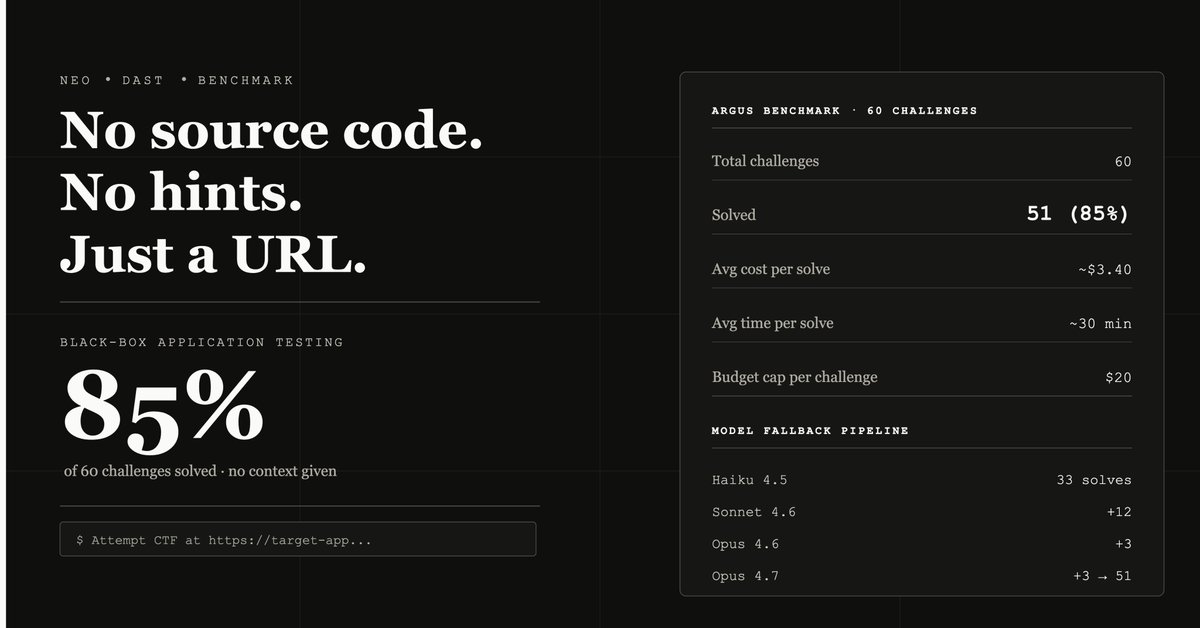
Benchmarking Neo's Black-Box DAST Capabilities
- Haiku 4.5 solved 33 of 51.
- Sonnet 4.6 picked up +12.
- Opus 4.6 picked up +3.
- Opus 4.7 picked up +3.
The harness matters as much as the model. With the right scaffolding, a smaller model can handle most of the work, and the frontier models earn their keep on the harder tail.
- 85% solve rate. ~$3.40 per solve.
Read more: projectdiscovery.io/blog/neo-black…
English
David Collins retweeted

ProjectDiscovery Nuclei Nights: Singapore
After Vegas last year, we're bringing it to Singapore for
Black Hat Asia & DEFCON Singapore week.
Tue Apr 28 / Sospiri, Marina Bay / 20:00
RSVP: luma.com/c7zmlpgp

English
David Collins retweeted

🚨 CVE-2025-0133 – Reflected XSS in PAN-OS
Affects Palo Alto firewalls. Issued just 6 days ago.
Nuclei detection template is now live ⚡️
#xss #infosec #security #bugbounty #paloalto

English
David Collins retweeted

@neo_ai_engineer just got a Deploy Agent for Runtime Validation for Security Review & Research
Validating vulnerabilities or reviewing a PR shouldn't require hours of environment setup. The Deploy Agent handles that.
Give it a CVE - it deploys the vulnerable app, reviews the code, and validates the finding with a real request/response and PoC at runtime.
Give it a PR - it spins up the app, validates the changes, and tears it down. Same agent, same power, both workflows.
Our @pdnuclei templates team is already using it to validate newly published vulnerabilities and hunt for 0-days in OSS.
See Deploy agent in action → neo.projectdiscovery.io/share/fc15a653…

English
David Collins retweeted

We built three full-stack apps using Claude Code, Codex, and Cursor - a healthcare portal, a banking platform, and an insurance claims system. The prompts were casual, exactly how people actually vibe code. No mention of security, nothing intentionally broken.
Then we threw four security scanners at them Neo, Claude, Invicti and Snyk and manually verified every single finding.
The results genuinely surprised us. 70 exploitable vulnerabilities across three apps. Unlimited money creation in the banking app. Any user could create admin accounts in the insurance platform. Patient records accessible to anyone in the healthcare portal. All Critical and High severity. All shipped out of the box.
But what really got me was the scanner gap. Neo found 62 of 70 vulnerabilities with only 5 false positives. Snyk found literally zero valid issues. The difference between these tools isn't incremental it's the difference between finding the bugs that matter and walking away with a false sense of security.
Full blog with the stats is live. The detailed research paper with exact prompts, methodology, all the findings, and the apps themselves is coming soon.

English
David Collins retweeted
David Collins retweeted

AI ships code faster than security can verify it.
On April 30, ProjectDiscovery's Davis Franklin is unveiling Neo — an autonomous security testing platform that thinks like a pentester, tests like one, and delivers proof with every finding.
Catch it at @ActualTechMedia's Agentic AI MegaCast 👇 🎁 Live attendees: shot at an M4 iPad Air
events.actualtechmedia.com/register-now/2…
English
David Collins retweeted

Why Bayse?
👉Zero maker fees on CLOB markets
👉Liquidity rewards for active quoting
👉NGN + USD support out of the box
👉An API that actually works
Bayse is building the infrastructure.
Harbinger is live here 👇
t.me/Harbingerbayse…
English
David Collins retweeted

@dontfadedave What's the accuracy of winning with bot with btc, sports etc?
English

@baysemarkets ✦ Harbinger just got a serious upgrade.
Here's what's new ⇩
🧵

Davexinoh 🦇🔊@dontfadedave
"The Bayse API just dropped." I opened the docs at 2AM and didn't sleep. Not because I was reading, Because I already knew what I was going to build. Introducing Harbinger.. A thread 🧵
English
David Collins retweeted
David Collins retweeted

🌠Are you interested in $13–$15/hr as a Side hustle or extra income?
📡Working remotely from home!
Agents Only is a gig-based software platform for managing customer support (CX) and data annotation needs on-demand.
It Combines AI tools with human talent to handle scaling support efficiently- think chat, calls, email, etc.
📥They currently have 9 active Data Labeling projects and their pipeline is continuously growing.
🏡By completing this application form, you'll be just a few steps away from joining one of our ongoing or upcoming projects.
👉100% permanent work-from-home
👉Earnings scale with your skills and expertise
👉Flexible project assignments based on your availability
🕥This form takes approximately 10–15 minutes to complete.
Data Annotator Application Intake Form is live!
Kindly answer every question carefully and accurately.
Fill form here; docs.google.com/forms/d/e/1FAI…
Disclaimer; This is not a paid promotion
Tudor™️@Big2dor
A new platform recruiting data annotators for AI training. Apply quickly! Link in the comment. Repost for others.
English
David Collins retweeted

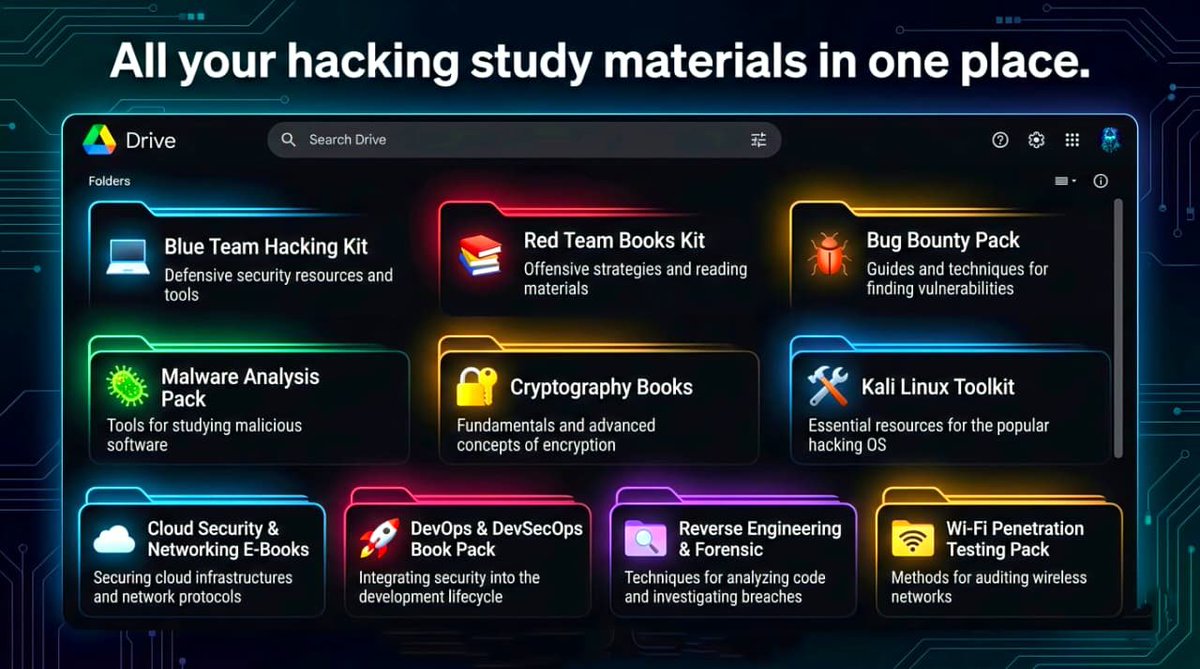
All Your Hacking Study Materials in One Place 🧠💻
Curated cybersecurity learning packs:
• Blue Team Kit — Defensive Security Tools
• Red Team Books — Offensive Security Guides
• Bug Bounty Pack — Exploit Hunting Resources
• Malware Analysis Pack — Learn Malware Secrets
• Cryptography Books — Code Breaking & Encryption
• Kali Linux Toolkit — Pentest Tools & Scripts
• Cloud Security & Networking E-Books — Cloud Defense
• DevOps & DevSecOps Pack — Secure Practices
• Reverse Engineering & Forensics — Deep Analysis
• Wi-Fi Pentesting Pack — Wireless Security Testing
📂 Download Links ↓
💻 Blue Team Hacking Kit
drive.google.com/drive/folders/…
📚 Red Team Books Kit
drive.google.com/drive/folders/…
🪲 Bug Bounty Pack
drive.google.com/drive/folders/…
🦠 Malware Analysis Pack
drive.google.com/drive/folders/…
🔐 Cryptography Books
drive.google.com/drive/folders/…
🛠️ Kali Linux Toolkit
drive.google.com/drive/folders/…
☁️ Cloud Security & Networking E-Books
drive.google.com/drive/folders/…
🚀 DevOps & DevSecOps Book Pack
drive.google.com/drive/folders/…
🔍 Reverse Engineering & Forensics
drive.google.com/drive/folders/…
📶 Wi-Fi Penetration Testing Pack
drive.google.com/drive/folders/…
"Attackers study systems. Defenders study attackers. Experts study both." 🔥
#Cybersecurity #EthicalHacking #RedTeam #BlueTeam #BugBounty #MalwareAnalysis #DevSecOps #Pentesting #Infosec
English
David Collins retweeted

吓到我了!
GitHub上有个工具叫GhostTrack,输入一个手机号,能直接扫出这人在哪些平台注册过账号,还能查IP定位、运营商信息。
克隆代码跑脚本,5分钟搞定,门槛低得离谱。你以为自己在网上隐身呢?
早被扒得透透的了。信息安全这事,真得重视起来。
🔗 github.com/HunxByts/Ghost…
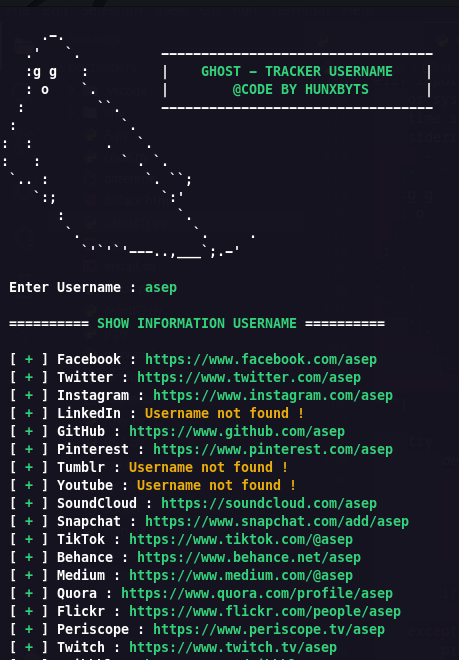
中文
David Collins retweeted

Penetration Testing Guide — Tools + Workflow in One Place 🐉📘
Complete pentesting pipeline with practical tools:
• Recon → Nmap, Netifera
• Info Gathering → theHarvester, Maltego
• CMS Detection → WhatWeb, CMS-Explorer
• WAF Detection → WafW00f
• Enumeration → DirBuster, WebShag
• Exploitation → SQLMap, Nikto, W3af, Shodan
• Post-Exploitation → Weevely, MSF Payloads
Everything structured — no random notes, just a clear workflow.
📥 Download: drive.google.com/file/d/0B6yhwL…
#Pentesting #CyberSecurity #WebSecurity #Infosec #AppSec


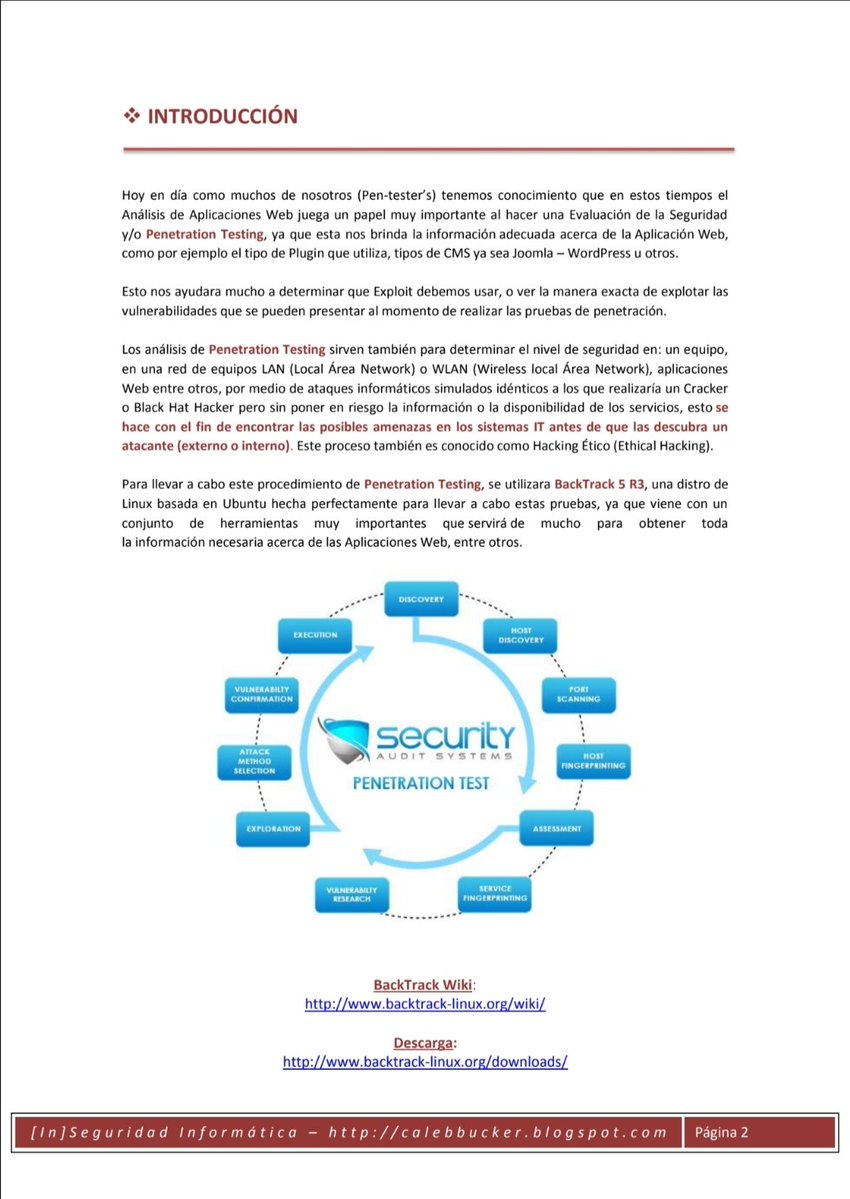
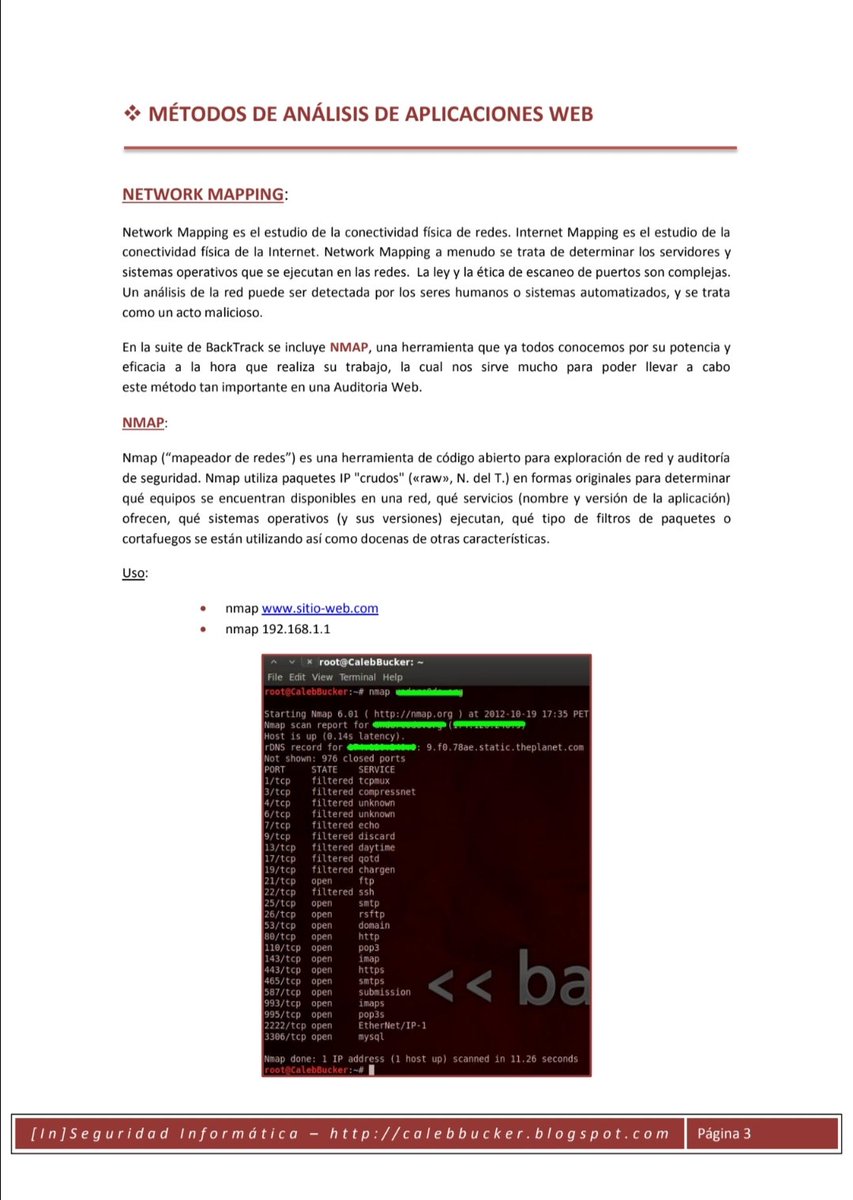
English