CYBER HUB
1.2K posts


CYBER HUB
@SOCDefender
Cybersecurity Content | SOC | Ethical Hacking | Pentesting + Blue Team🛡️


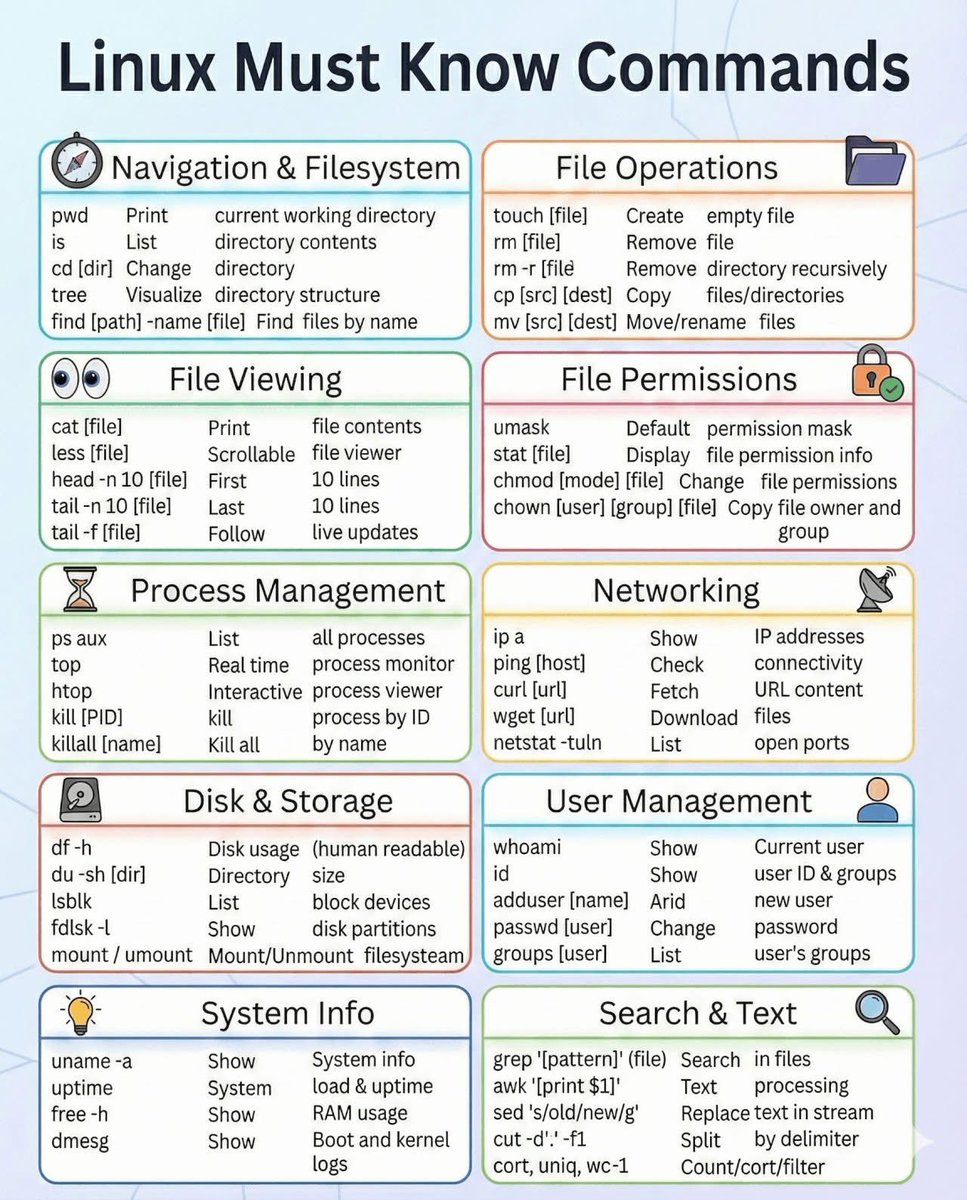
LINUX KNOWLEDGE CHECKPOINT Which command is used to display currently logged-in users on a Linux system? A. whoami B. who C. id D. userset

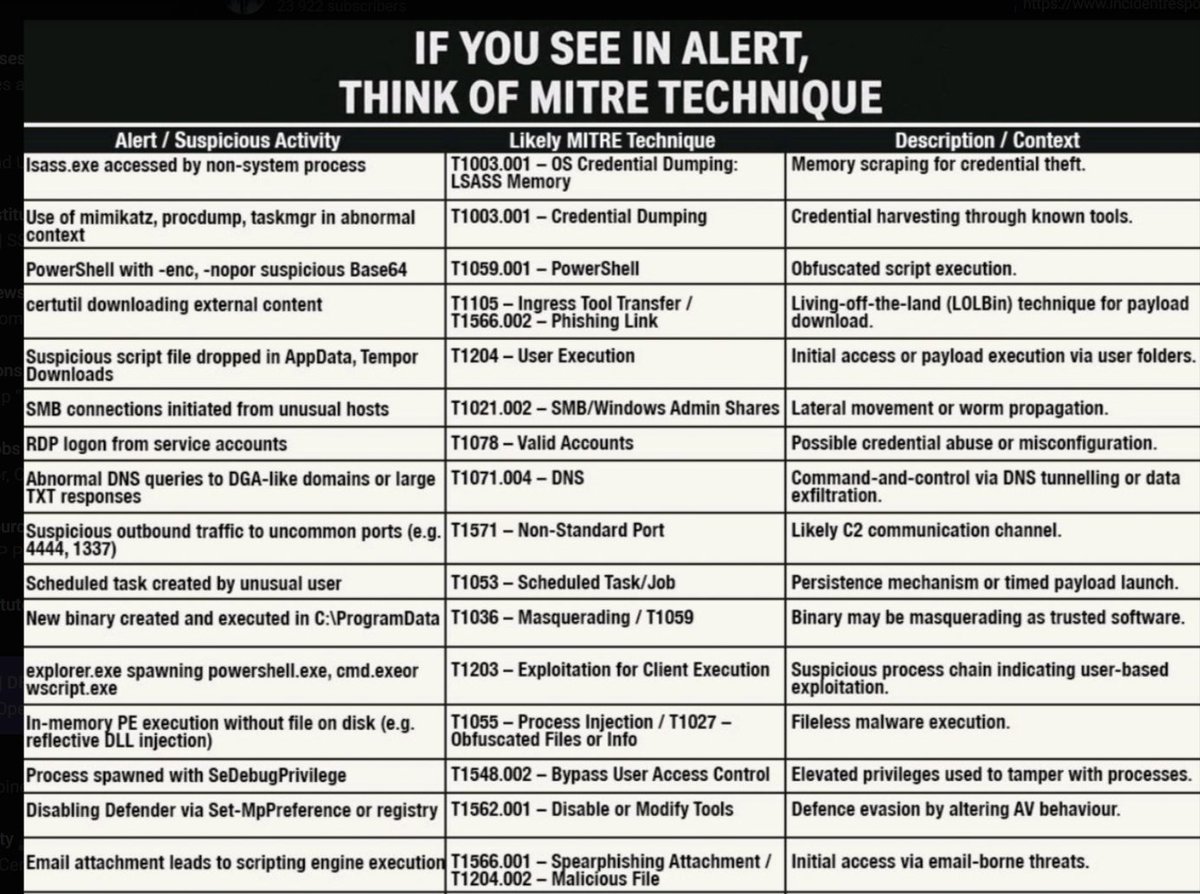
EDR

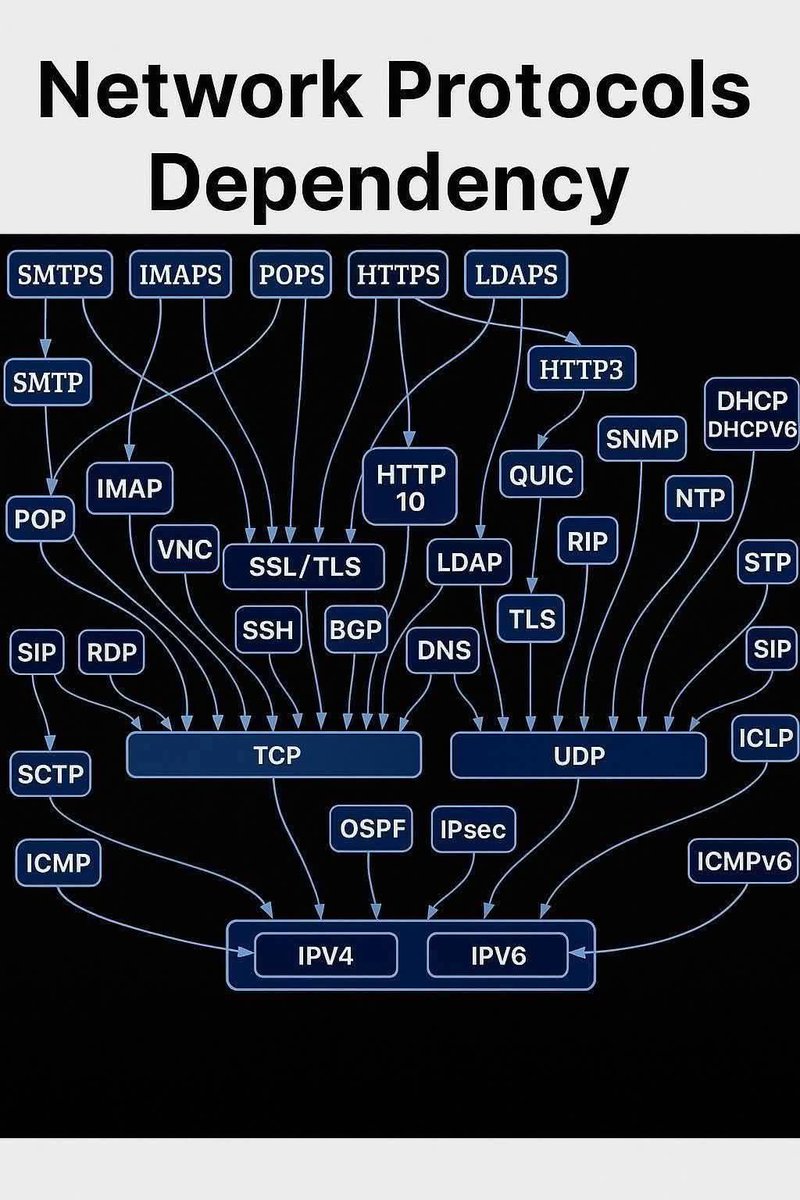
NETWORKING KNOWLEDGE CHECKPOINT Which of the following IP addresses is a private IP address? A. 8.8.8.8 B. 172.20.15.10 C. 192.0.2.1 D. 150.10.5.5

Interviewer: When you're using a VPN, your ISP can still see how much data you’re using, but they can't see what you’re doing. However, if you're watching a 4K movie on Netflix over a VPN, a sophisticated ISP can still guess exactly what you're watching just by looking at the "shape" of your traffic. How is that possible if the data is fully encrypted?


Linux Server is slow due to high CPU utilization. How will you fix it?