🚨 Microsoft paid $1.6M to ethical hackers in ONE event.
Bug bounty is real.
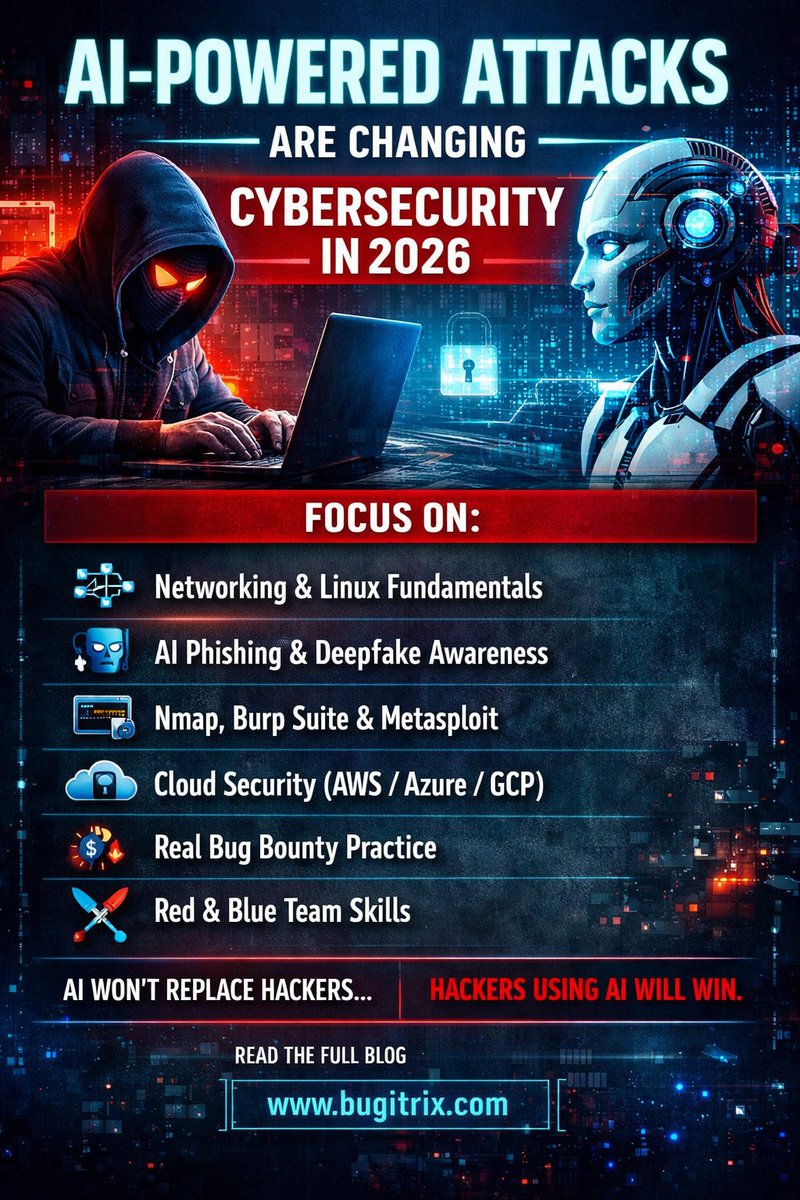
Top hackers earned big by finding flaws in AI, Cloud & security systems.
💡 Want in?
Read 👉 bugitrix.com/blog/news-tren…
Learn. Hack. Report. Repeat. 🔁
#CyberSecurity #BugBounty #EthicalHacking #InfoSec

English