10.3K posts




🆔Government to public: Do you want digital ID checks to be used to enforce a social media ban for under-16s ☐ Yes ☐ Definitely yes ☐ Strongly yes ☐ Yes 100% The “consultation” doesn’t appear to have a box for disagreeing.







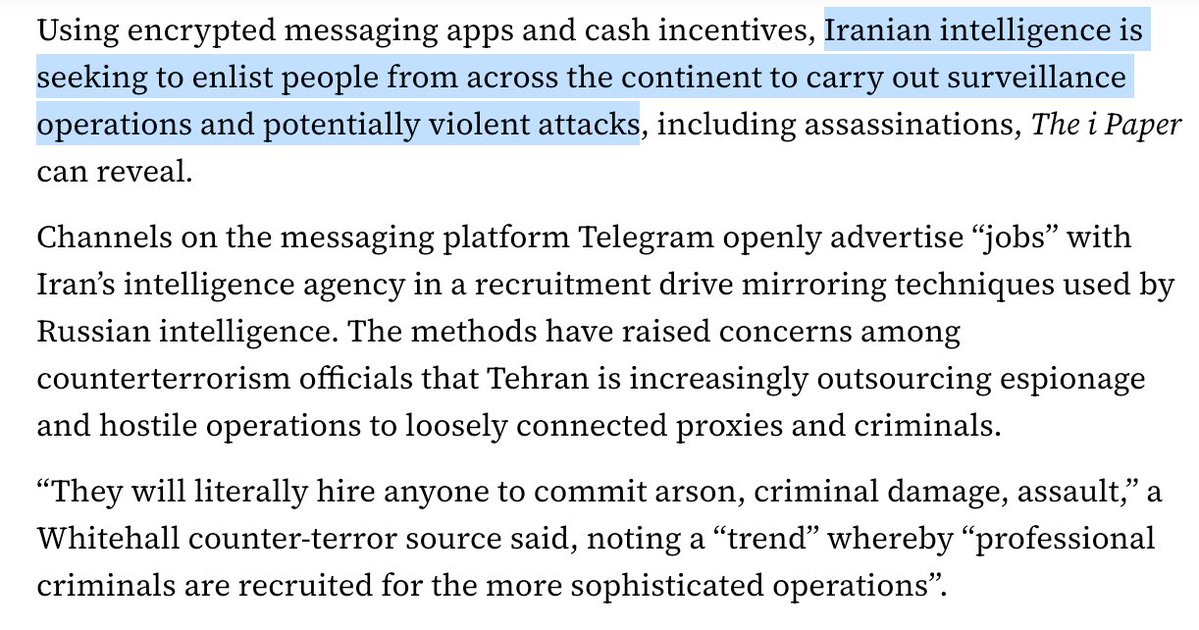
Russia has embraced a novel technique: Sabotage-as-a-Service.💣 It’s outsourcing disruption like gig work. Immigrants and petty criminals are recruited via Telegram with offers of quick jobs: hang a poster, set fire to a telecom box, cut a cable, snap a photo. Cheap. Simple. Anonymous. No training needed. No loyalty required. Just finish the task. There’s no need to risk real agents when freelancers will do. Complete the job — get paid. Welcome to Kremlin Rewards, a loyalty scheme for sabotage? One incident? It’s nothing. But 💥dozens spread fear, chaos, and a creeping sense of insecurity. That’s the whole point. They’re about corrosion, psychological and cognitive operations. See the map of Russian hybrid operations in Western Europe. As you can see: there's a lot happening. Worth noting: European railways have become a key target. They’re critical to NATO’s military logistics. One failure can block thousands of kilometres of transport routes.


Defense Secretary Pete Hegseth gives Anthropic a Friday deadline to open its AI technology for unrestricted military use or risk losing contract, source tells AP. apnews.com/article/anthro…

BREAKING: Hegseth gives Anthropic until Friday to back down on AI safeguards, per Axios





The Telegraph has uncovered yet more about the UK government's 'AI skills hub' that suggests the entire thing was a rushed, vibe-coded hack job (which cost £4.1 million of taxpayers' money). Their investigation reveals it includes: - courses that seem to be AI-generated scams - courses that are more than 20 years old - 'degrees' that cost thousands of pounds yet offer no meaningful qualifications - courses that don't exist at all And so much more. This bit killed me: "One course on 'digital agriculture fundamentals' is provided by a Canadian education company and requires applicants to live in the rural provinces of Alberta, Manitoba or Saskatchewan." Yet the government is digging in, saying the hub is meant to provide "deep and specialist expertise in AI", and that it intentionally includes "some hybrid international options". To be clear, if one of the AI companies the government so admires had released this product, the person responsible would have been fired within a day. telegraph.co.uk/business/2026/…