0xBB
714 posts

0xBB
@bb_hacks
Someone who breaks stuff, sometimes even on purpose!



Microsoft AI CEO, Mustafa Suleyman, says that "most, if not all, professional tasks" undertaken by white collar workers will be fully automated by AI within the next 12 to 18 months









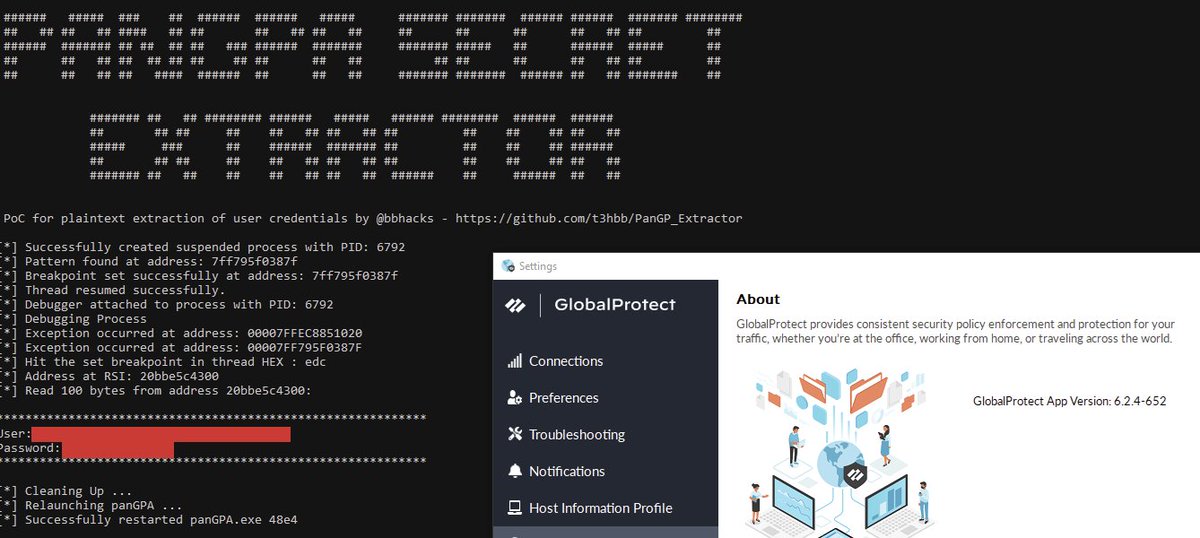
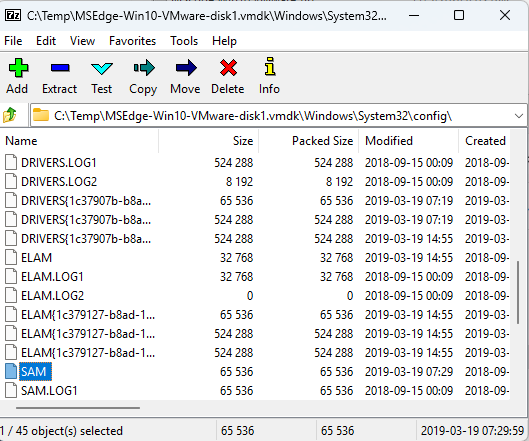
Fancy retrieving plaintext user credentials, deactivation passcodes and uninstall passwords for Palo Alto Global Protect VPN? Thank goodness Palo Alto make that easy for you ... Full write up here : shells.systems/extracting-pla… Tooling available here : github.com/t3hbb/PanGP_Ex…
Hi, it's tuts-for-nerds giveaway 6. (we movin' 'n' groovin') Our friend @mrgretzky hooked us up with 12 vouchers for the Evilginx Mastery course. Initially we were supposed to do this 12 does before Christmas, but we're swamped. Please forgive us, Kuba. I love you. If you'd like to master Evilginx, leave a comment below - Winners will be selected randomly in the next 24 hours. - We will DM winners. - If you do not confirm your win in 24 hours a new winner will be selected - If your DMs are closed, you automatically forfeit your prize Have a nice day