escrow
1.5K posts

escrow
@escrow_
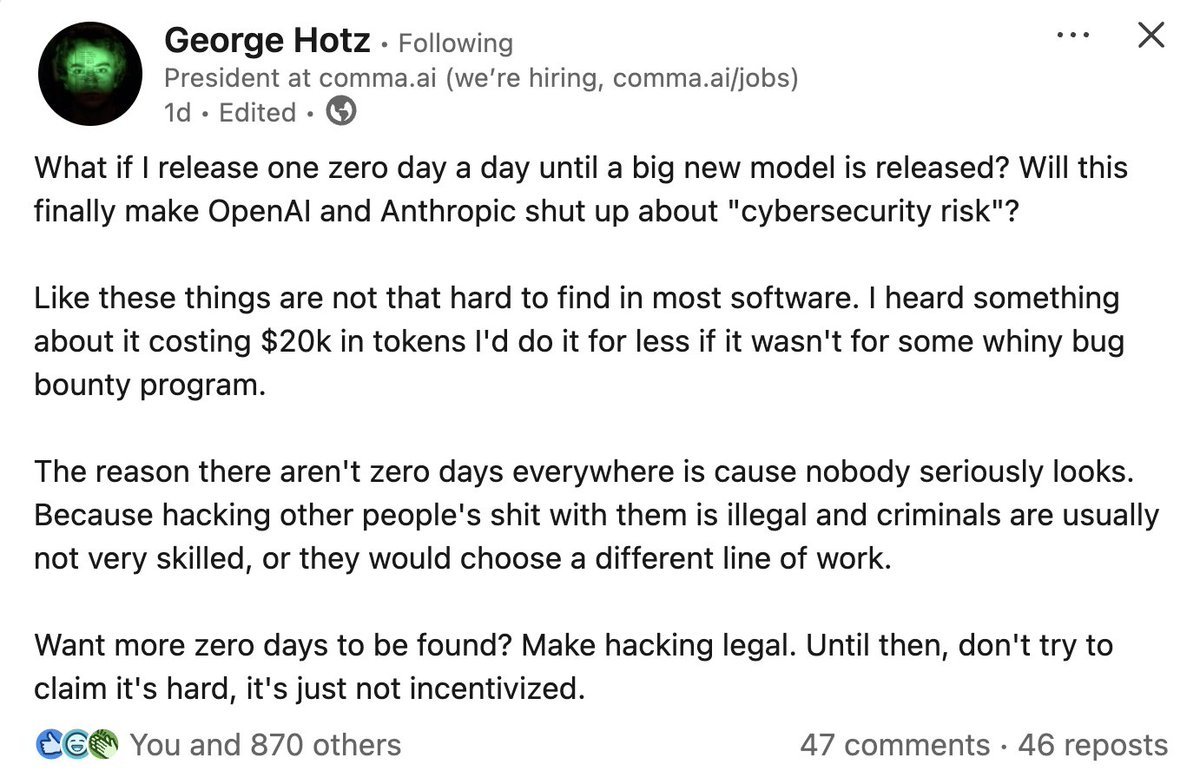
0days or bust














Can share atleast 3 perspectives on why you’re completely wrong but I see people have already commented that. Here’s a TL;DR for you: 1. In future hackers won’t return any funds 2. Hacker was offered the 10% of stolen amount as bounty by GMX which is standard. He didn’t negotiate. 3. Going by your logic it would have been best it he didn’t return any funds as law enforcement would still pursue him but now atleast you have a better example of minimising losses. You want to close this door as well?





There is a huge community that operates in parallel alongside the legitimate SR community of people who submit AI reports all day long in the hopes of getting $50 payout here, $500 there by tricking a project.





River hums softly, Capybara finds the breach A fortune flows in. Huge congratulations to @capybara_sr for earning a massive $500,000 bug bounty on Immunefi. Could be you.