Hackademy
77 posts

Hackademy
@hack_ademy
We teach Real Hacking here. If you want Hands-On then you are in the right place. Founded by @officialwhyte22



Here's how you can capture login credentials in plain text in under 2 minutes. No exploitation. No brute force. Just passive sniffing. Here's exactly what happened 👇 > Opened http://testfire[.]net — an intentionally vulnerable lab site running on HTTP (no encryption) > Started capturing traffic in Wireshark on my WiFi interface > Logged in with credentials on the site > Successfully authenticated — from the site's perspective, everything looked normal > Stopped capture → filtered with: http.request.method == "POST" > One packet. I clicked it. Expanded the HTML form data. > Username and password — sitting there in plain text. This is not a hack. This is just reading what your device is already broadcasting. On HTTP, anyone on the same network can do exactly this. This is why HTTPS exists. This is why that padlock matters. This is why you should never log into anything sensitive on public WiFi. Demonstrated in a controlled lab environment on an intentionally vulnerable site built for security testing. Video credits: @arceuzvx #EthicalHacking #MITM #Wireshark #NetworkSecurity #CyberSecurity #OffSec #Kali

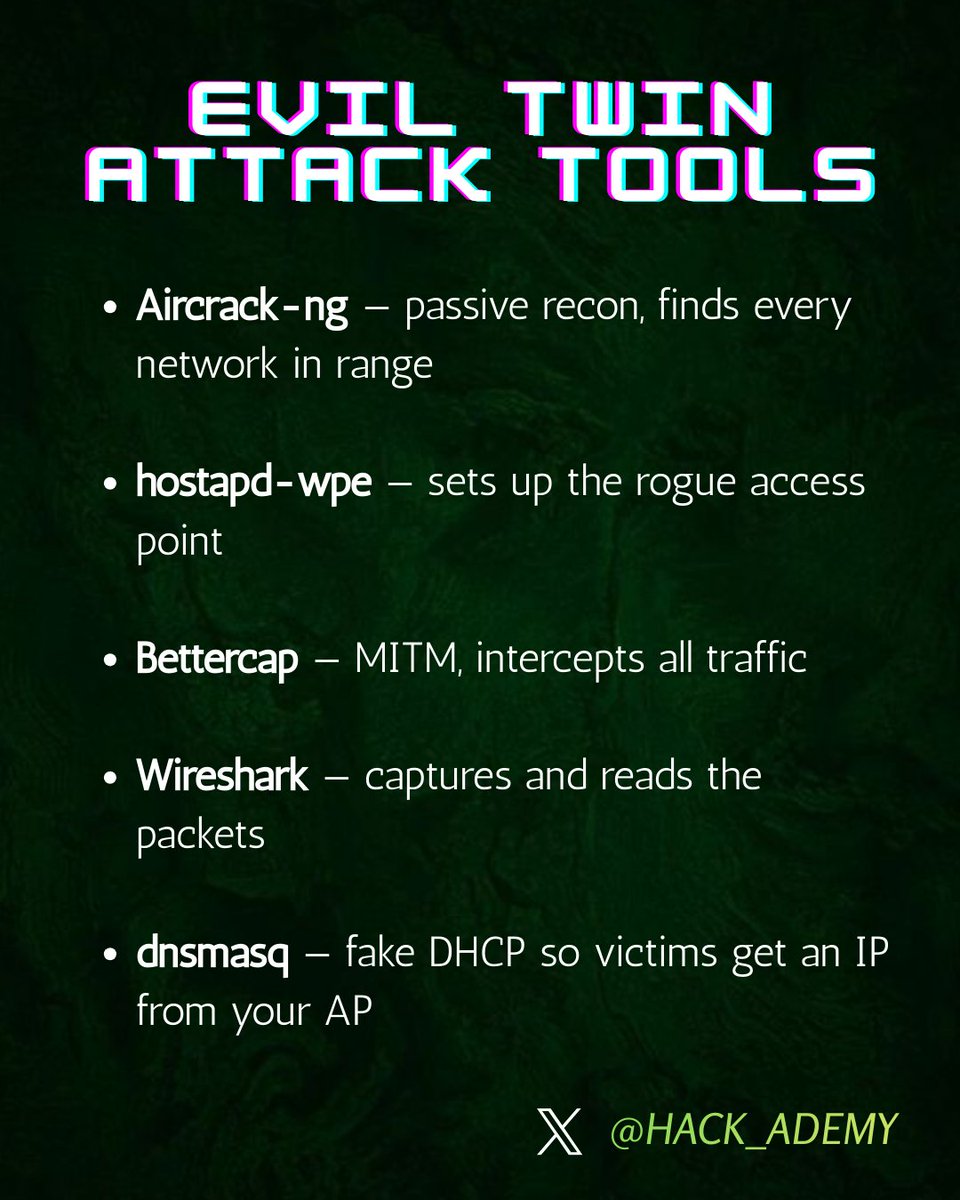
Man-in-the-Middle attacks don't get enough attention. Not because they're rare — because they're quiet. Most people picture hacking as breaking into systems. MITM is different. It's about sitting silently between two parties and watching everything flow through you. Here's what that actually looks like: Instead of this: User → Server The attacker makes it this: User → Attacker → Server Both sides think they're talking to each other. They're not. And neither side notices anything wrong — the page loads, the UI looks fine, everything feels normal. That's the whole game. Getting into the communication path is step one. Attackers do this through: —> Joining the same public WiFi and exploiting weak configs —> Setting up an Evil Twin —> a fake hotspot identical to the real one —> ARP spoofing —> tricking devices into routing traffic through their machine — DNS spoofing —> silently redirecting users to malicious destinations Once they're in the middle, the real work begins. If the connection isn't properly secured, the attacker can: —> Read credentials and session cookies in plain text —> Inject malicious scripts into responses —> Modify transactions in real time —> Strip HTTPS down to HTTP so everything becomes visible. The scary part isn't the technique. It's that the victim never notices. The website loads. The interaction feels completely normal. Meanwhile everything is being harvested in the background. This is why MITM still works in 2026 —> not because defenses don't exist, but because implementation is inconsistent and users ignore warnings. Prevention is layered: For engineers: → Enforce HTTPS everywhere + HSTS headers → Certificate pinning in applications → Mutual TLS where appropriate → Monitor for ARP/DNS anomalies → Zero Trust —> never assume a network is safe. For everyone else: → Treat public WiFi as hostile by default → Use a VPN on untrusted networks → Never ignore browser certificate warnings → Don't log into sensitive accounts on unknown networks MITM isn't an advanced exploit. It's a positioning attack combined with basic protocol abuse. That's exactly why it keeps working. If you're serious about security — don't just read about it. Spin up a lab, simulate it, and watch how easily trust breaks down. (Demo video coming soon 👀) #CyberSecurity #MITM #EthicalHacking #NetworkSecurity #OffSec #hack_ademy