H4RUK7 KIRA 🇯🇵🇨🇵
9.2K posts

H4RUK7 KIRA 🇯🇵🇨🇵
@h4ruk7
私は私はデジタルの戦士だ| founder @hsc_consult
Hiroshima-shi Naka, Hiroshima Katılım Kasım 2024
571 Takip Edilen10.4K Takipçiler
Sabitlenmiş Tweet

I will drop a detailed road map to becoming a master hacker from
☑️ computer basic
☑️network infrastructure set up
☑️web hacking
☑️system hacking
☑️hardware hacking
☑️ programing language you need
☑️ operating system
follow @h4ruk7
repost & share to 3 friends
comment roadmap
English

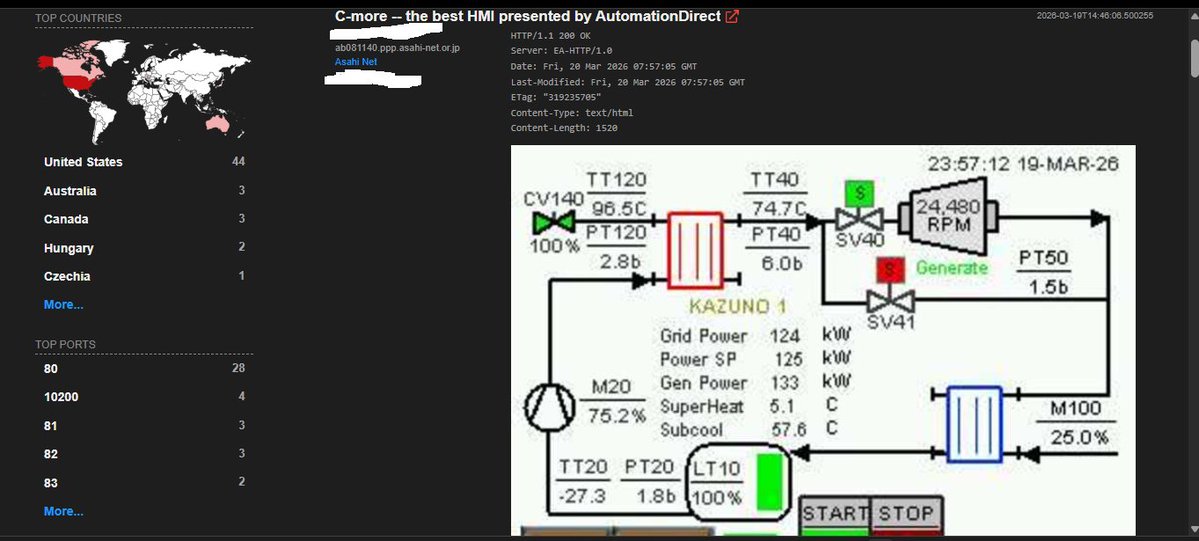
@OnijeC yes boss very big bad boy i have been learning how to hack sacada systems lately
English

@Zoho is even more expensive than Google cause why would I have to pay for the number of hosts and participants in a meeting when Google can take more than a thousand
English
H4RUK7 KIRA 🇯🇵🇨🇵 retweetledi


the stress bug bounty hunters go through i cant stand it mhen
Shad0w@Itx_Shad0w
This is beyond frustrating, @Bugcrowd. For 5 months, I’ve been trying to receive my payouts. I followed every step, provided every document, and even spent ~$500 to register a UK business just to comply.
English
H4RUK7 KIRA 🇯🇵🇨🇵 retweetledi
H4RUK7 KIRA 🇯🇵🇨🇵 retweetledi

Man-in-the-Middle attacks don't get enough attention.
Not because they're rare — because they're quiet.
Most people picture hacking as breaking into systems. MITM is different. It's about sitting silently between two parties and watching everything flow through you.
Here's what that actually looks like:
Instead of this: User → Server
The attacker makes it this: User → Attacker → Server
Both sides think they're talking to each other. They're not. And neither side notices anything wrong — the page loads, the UI looks fine, everything feels normal.
That's the whole game.
Getting into the communication path is step one. Attackers do this through:
—> Joining the same public WiFi and exploiting weak configs —> Setting up an Evil Twin —> a fake hotspot identical to the real one —> ARP spoofing —> tricking devices into routing traffic through their machine — DNS spoofing —> silently redirecting users to malicious destinations
Once they're in the middle, the real work begins.
If the connection isn't properly secured, the attacker can:
—> Read credentials and session cookies in plain text —> Inject malicious scripts into responses —> Modify transactions in real time —> Strip HTTPS down to HTTP so everything becomes visible.
The scary part isn't the technique. It's that the victim never notices. The website loads. The interaction feels completely normal. Meanwhile everything is being harvested in the background.
This is why MITM still works in 2026 —> not because defenses don't exist, but because implementation is inconsistent and users ignore warnings.
Prevention is layered:
For engineers: → Enforce HTTPS everywhere + HSTS headers → Certificate pinning in applications → Mutual TLS where appropriate → Monitor for ARP/DNS anomalies → Zero Trust —> never assume a network is safe.
For everyone else: → Treat public WiFi as hostile by default → Use a VPN on untrusted networks → Never ignore browser certificate warnings → Don't log into sensitive accounts on unknown networks
MITM isn't an advanced exploit.
It's a positioning attack combined with basic protocol abuse.
That's exactly why it keeps working.
If you're serious about security — don't just read about it. Spin up a lab, simulate it, and watch how easily trust breaks down.
(Demo video coming soon 👀)
#CyberSecurity #MITM #EthicalHacking #NetworkSecurity #OffSec #hack_ademy

English

Updates:
The Hacker News@TheHackersNews
🛑 Perseus, a new #Android malware, enables full device takeover via Accessibility abuse. It runs live remote sessions, steals banking credentials, and scans notes apps for sensitive data. It spreads through IPTV-style apps delivered via phishing and sideloading. 🔗 Read → thehackernews.com/2026/03/new-pe…
English