Tweet fijado

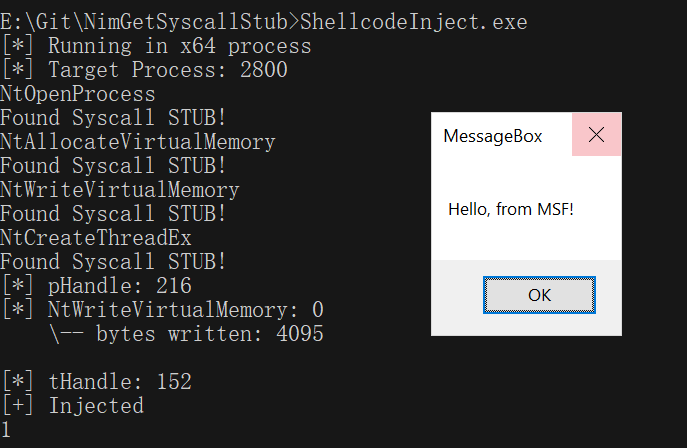
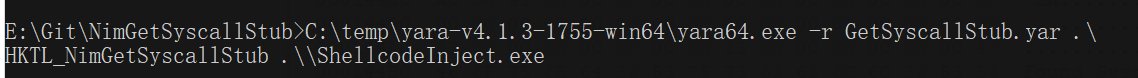
I have recently developed a tool which consists of 13 different shell code injections to evaluate endpoint detection capabilities. All credits go to @Ne0nd0g @_D00mfist @C__Sto @_batsec_ @spotheplanet for their amazing works that inspired me to do it.
github.com/sh4hin/GoPurple
English