Cryptology07 「🦑」 🦭/acc
22.5K posts

Cryptology07 「🦑」 🦭/acc
@Cryptologyo7
Cryptology07.sui Fudyou.sui
Inscrit le Haziran 2016
5.7K Abonnements1K Abonnés

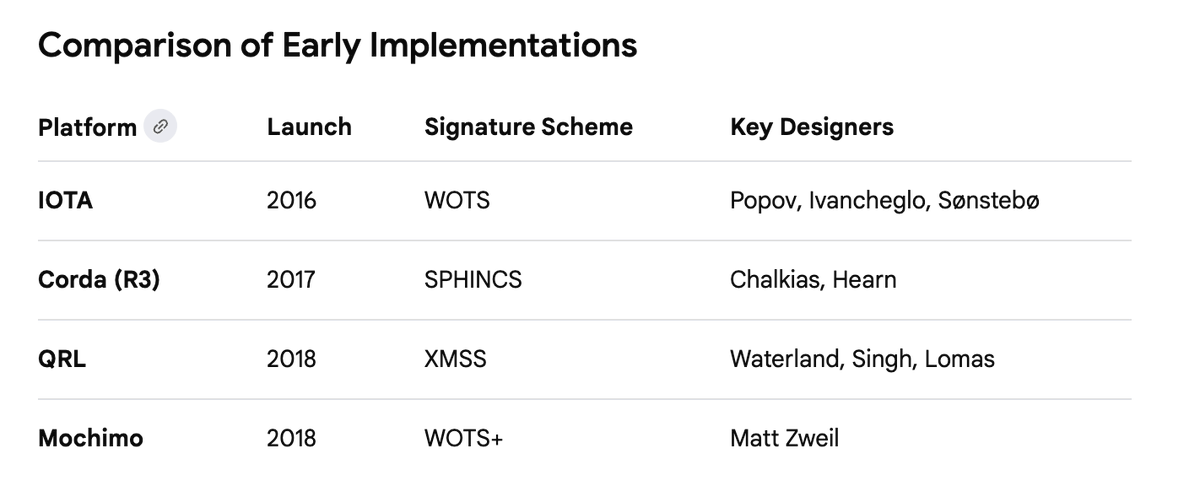
After two nights of April Fools quantum drama, let’s drop some receipts, mostly to get back my sanity as I was left without saliva.
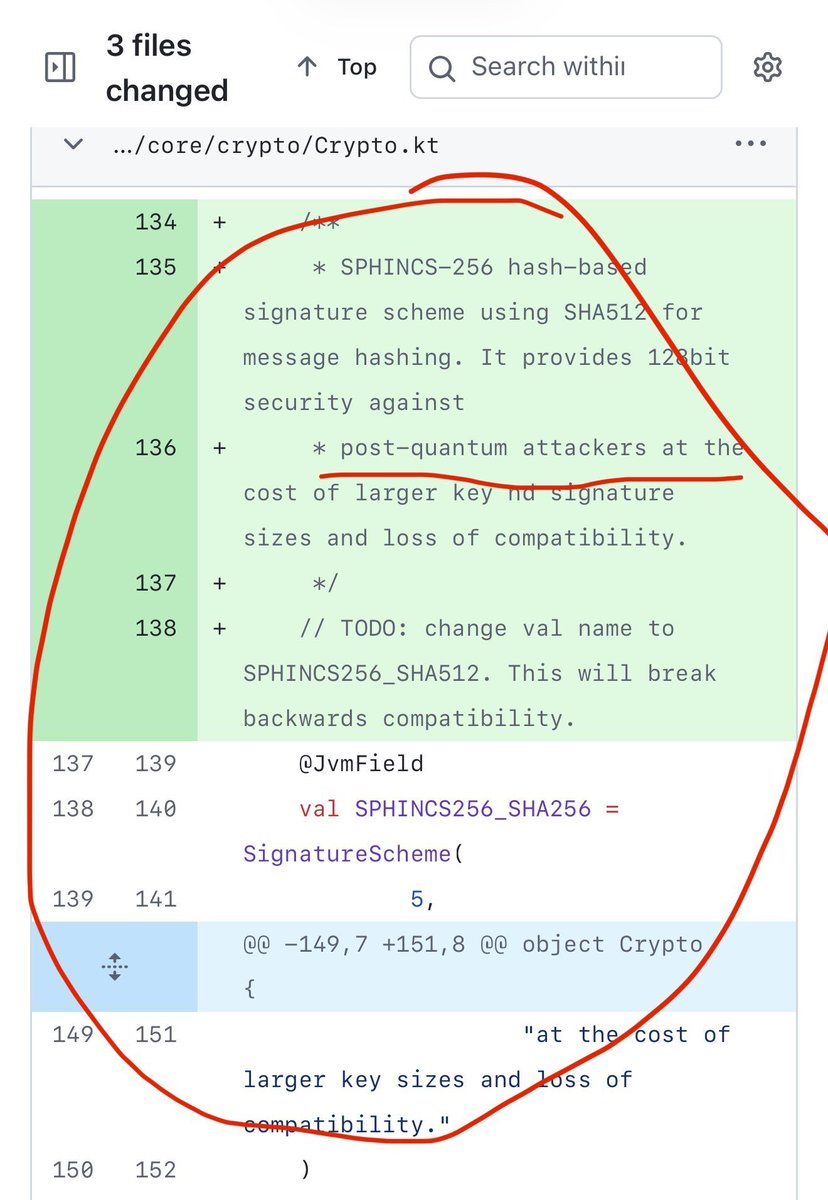
First stateless (multi-use) quantum-safe signatures in crypto / distributed ledgers? Yeah… that was me and Mike Hearn (one of the OG Bitcoin devs). We designed and shipped the first stateless post-quantum scheme in production for blockchains a decade ago.
10 years later Google posts a paper and suddenly everyone’s calling…
…but they’re all late and thirsty. 😅
Believe me, SUI is on something quantum unique

English

@0xrajendra @MrBreadSmith @Reset_sui @0xd34th @EmanAbio @0xPain__ @MinhTranQuang10 Thank you Raj!
Really appreciate your advice.
I also see the hacker's wallet has an alphalend position.
English
I don’t see any on-chain activity that suggests your private key was exposed via a contract or tx. This is most likely an off-chain compromise.
Common causes:
• Malware / compromised device (even opening a dowloaded folder can do it)
• Seed/private key stored digitally (notes, screenshots, cloud, etc.)
• Clipboard or browser extension exploit
Immediate steps:
Assume the device is compromised. Stop using it for crypto transactions.
• Use a clean device (phone/new laptop)
• Create fresh wallets (preferably hardware like Ledger Stax. It works with @SlushWallet)
•Transfer any remaining funds from other wallets ASAP
•If you have EVM wallets, then revoke all approvals across wallets.
Going forward: never store keys digitally, avoid unknown downloads, and isolate your signing environment.
I am sorry, mate!
English

@MrBreadSmith @Reset_sui @0xrajendra @0xd34th @EmanAbio
@0xPain__ @MinhTranQuang10 @_Dragnipur
What precautions should I be taking for damage control?
Cryptology07 「🦑」 🦭/acc@Cryptologyo7
One of my wallets just got drained. No idea how. Wasn't connected to any site except for unstaking $wal last epoch. 0xd1330453694c952472a57a7aac81b92cce44e419d78611bfb9ef337cd0ff1fce Hacker's wallet 0xc9f175af6a0a901eb0b2d48d0b88da192224533d6a1b5d9add30b2867bcd7a76
English

GM fam!
Looks like my X account has gone!😱
Can you please react to this post to see if you're still seeing me?
Can you check if you can see my older posts and let me know?
@X what happened. Could you please help?!
Ampelokipoi, Greece 🇬🇷 English
Cryptology07 「🦑」 🦭/acc retweeté

Over the past few months, we’ve been in the kitchen cooking hard.
Designing, building, shipping quietly.
Solving one problem: how do you let agents move money without losing control?
We built @KairoGuard to solve this.
An on-chain policy layer so agents can execute, but only within rules you set;
Without sacrificing custody. One-line SDK install.
This is the missing layer for agentic finance.
Now it’s time. We’re opening to early users.
Comment below if you want access 👇
English
Cryptology07 「🦑」 🦭/acc retweeté

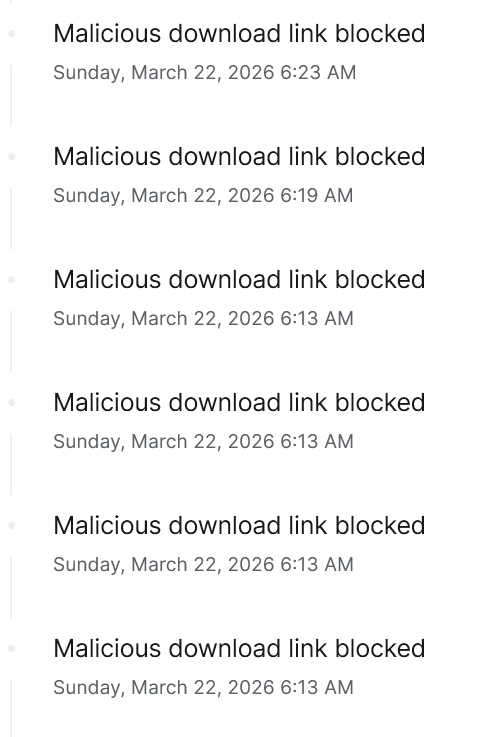
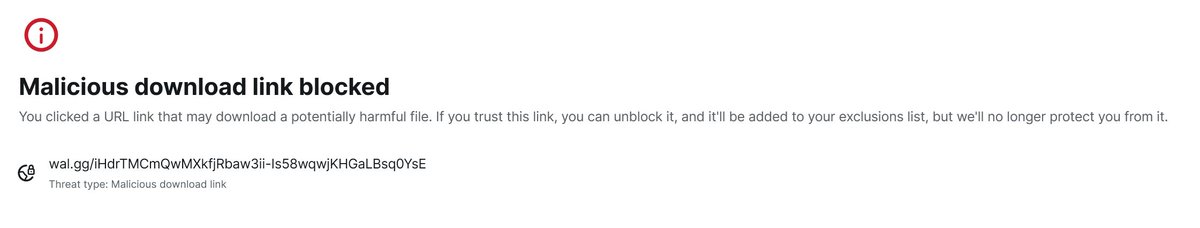
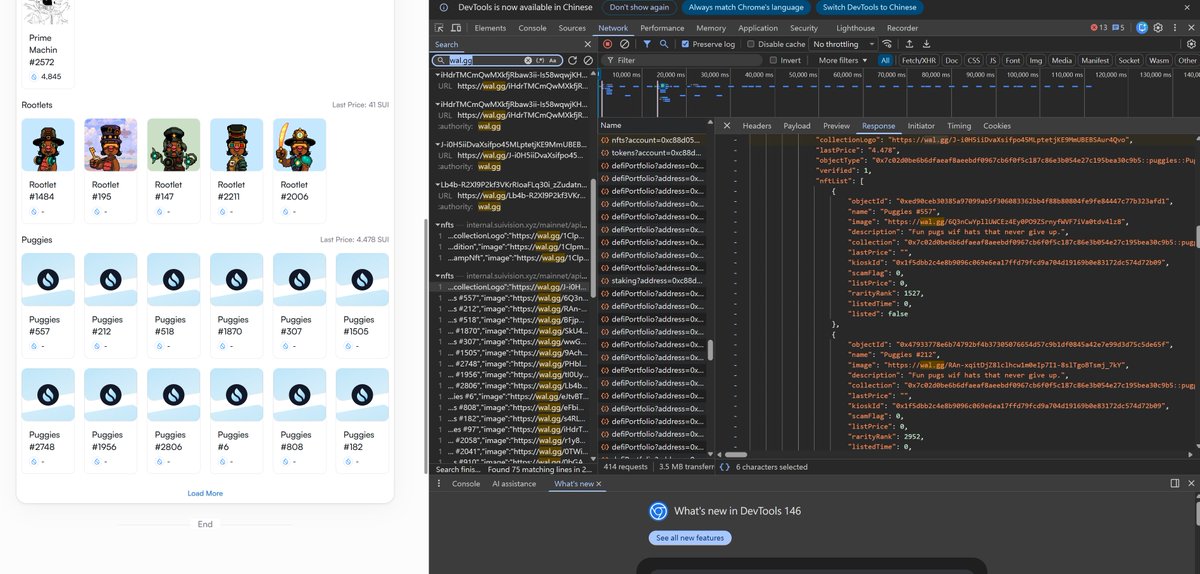
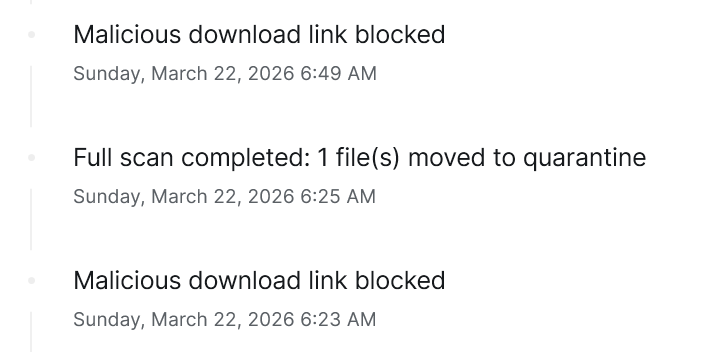
🚨 Security Alert for Old Sui NFT Project: Puggies 🚨
Attention to anyone holding the "Puggies" NFT collection! The project's image domain has been compromised and is acting as a malicious download endpoint.
🔍 My Investigation Process: After my antivirus blocked downloads on Suivision/Suiscan, I inspected the network requests via browser DevTools (F12). I found that in the portfolio API response, the image_url and collectionLogo of the old "Puggies" collection had been hijacked and replaced with malicious links. Alarmingly, the explorer APIs still return "verified": true and "scamFlag": 0 for this collection.
⚠️ The Trigger Mechanism: When you (or anyone) look up the contract or a holder's address, the browser automatically requests these hijacked URLs to render the portfolio. This triggers a background download of a malicious file (usually a .rar archive), leaving frontends completely defenseless.
🛡️ Security Actions:
DO NOT Search: Do not look up the Puggies contract or any holder's address on explorers out of curiosity. This will instantly trigger the malicious download.
Check your downloads: If you find an unknown .rar file, DO NOT extract or run it. Simply permanently delete it (Shift + Delete). It is harmless if unopened.
Antivirus blocks: If your antivirus quarantines the file, your protection is working. Do not whitelist it.
NEVER Interact or Burn: Do not attempt to transfer or "Burn" this NFT. Interacting can trigger hidden malicious contract approvals.
Hide via Frontend: Holders should open their wallet app (e.g., Sui Wallet) and set the "Puggies" collection to "Hide" to stop auto-fetching.
@SuiCommunity @blockvisionhq @suiscanofficial @SuiPugwif @EmanAbio @Walrus_CN @WalrusProtocol @SuiFoundation
#Sui #SuiNetwork #Web3Security #Puggies
English
Cryptology07 「🦑」 🦭/acc retweeté
Cryptology07 「🦑」 🦭/acc retweeté

🚨 BIG: 65 TB of indexed blockchain data from Bitcoin, Sui, Ethereum, Arbitrum, Tron and XRP just landed on Walrus.
And we're not talking raw data. These are standardized, finance-ready datasets from @AlliumLabs, the platform trusted by Visa and Stripe.
All datasets are encrypted and unlocked the moment you purchase, whether you're a human or an AI agent.
And this is just the first 65 TB 🦭👀

English
Cryptology07 「🦑」 🦭/acc retweeté

Coda launches this spring. Private beta onboarding begins soon and we're looking for testers!
If you love music, are a core part of the @_StudioMirai or @SuiNetwork community, and want to help shape the future of music, drop a comment below.
I'll be reaching out.
English

@Cryptologyo7 Yeah lol unfortunately I went a bit over that goal, I would like it back there right about now too😁
English

The simplest solution here is running $WAL, it would p easy considering how Sui ran.
I'm also in the hole and one of the biggest $WAL holders prob
Wara@0xWara
Raise your hand if you staked $WAL because Adeniyi promised multiples airdrops
English









