ret2basic.eth
2.6K posts


ret2basic.eth
@ret2basic
@taichiaudit Founder | Web3 Security Researcher @yAuditDAO @zenith256 @plainshift @getfailsafe | Core Member @DeFiHackLabs
GMT+8 शामिल हुए Ocak 2018
3.9K फ़ॉलोइंग2.2K फ़ॉलोवर्स
पिन किया गया ट्वीट

Holiday season is here, and we @taichiaudit are starting a DeFi source code walkthrough campaign: one article every 1–2 days, from now until the end of January 2026. If you're a dev or security researcher leveling up in the bear market, this is for you.
English

@Fav_Truffle Convert all the code to the most compact form (single line) to avoid the nsloc quoting cost and convert back to normal in fixes
English

ret2basic.eth रीट्वीट किया

"FailSafe's agentic security system helped us catch an important issue and provided us with a great threat model which we can utilize for further development."
@megabyte0x, Co-Founder @bitmor_btc
Thank you to the Bitmor team and @base for the incredible commitment to security.
getfailsafe.com/bitmor-agentic…

English

Because of that, localResults.maxCloseableBorrowAmount_TargetUnderwaterAsset can be positive even when the account is healthy.
So the attacker does not need to wait for genuine insolvency. They can supply an asset, borrow that same market, then call liquidateBorrow() on themselves with the same asset as both debt and collateral and harvest bogus internal collateral credit.
English

There is a second bug that makes this path reachable much more easily: the insolvency gate is broken.
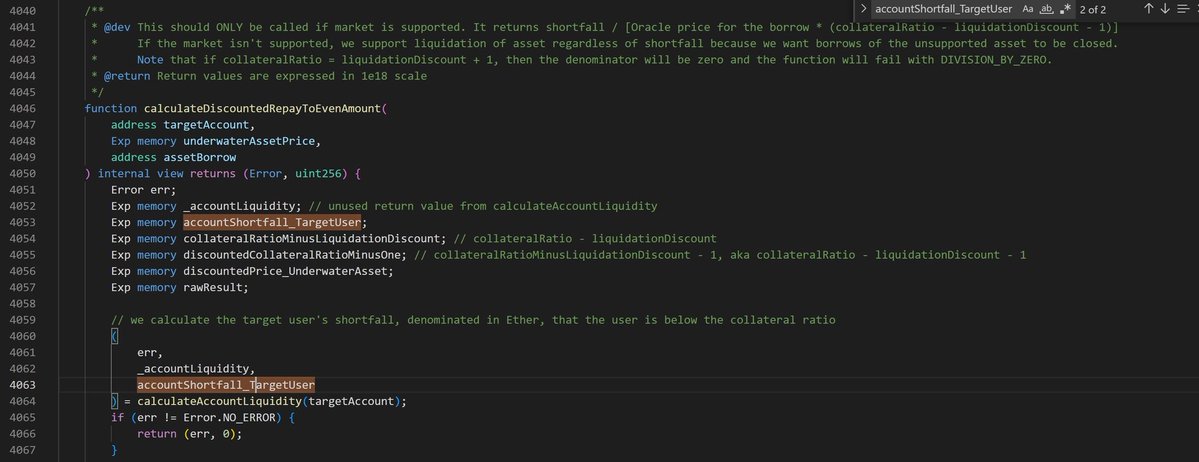
The comments say liquidation should depend on the borrower’s shortfall (the underwater amount), but calculateDiscountedRepayToEvenAmount() reads the target account’s shortfall and then never uses it. You can ctrl+f for accountShortfall_TargetUser and see it is not used anywhere in the contract.
Instead, the close cap (the maximum amount of the borrower’s debt that this liquidation is allowed to repay in one call) is effectively derived from close factor and borrow balance.
English

On March 10th, 2026, AlkemiNetwork was hacked because liquidateBorrow() allows a user to liquidate their own position specifying the same asset as both debt and collateral via user input.
In Alkemi's liquidation design, seized collateral is reassigned by internal accounting rather than transferred out as ERC-20 tokens directly. That means self-liquidation can alias the borrower's collateral accounting and the liquidator's collateral accounting to the same storage slot, so the protocol repays debt while crediting extra internal collateral instead of performing a neutral self-transfer in the book.
A second bug makes that path reachable even for healthy accounts: calculateDiscountedRepayToEvenAmount() reads the borrower's shortfall but never uses it, so liquidation can proceed without real insolvency.
Attack tx: app.blocksec.com/phalcon/explor…
Vulnerable code: vscode.blockscan.com/ethereum/0x85a…
English