ret2basic.eth
2.6K posts


ret2basic.eth
@ret2basic
@taichiaudit Founder | Web3 Security Researcher @yAuditDAO @zenith256 @plainshift | Core Member @DeFiHackLabs



Translation: you passed verification but we won't allow you to do your regular job, what you gonna do about it kid?








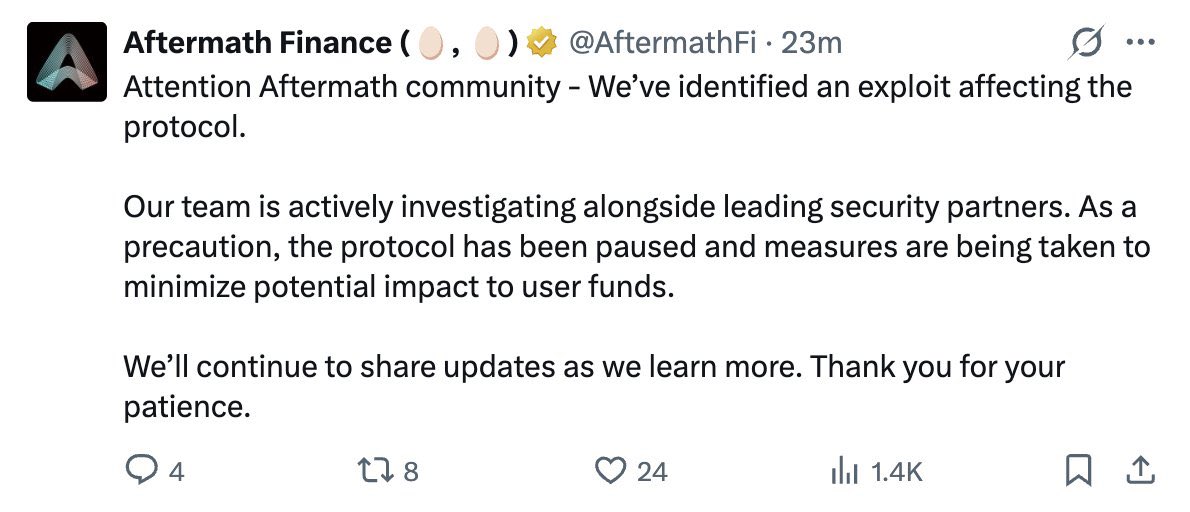

It seems a @tradingprotocol vault, i.e., YieldCore-3rd-deal, was exploited with $398k loss. There is a missing check on the caller authorization, which is exploited to drain all funds from the vault. Here is the related tx: etherscan.io/tx/0x6b04344d5…



🚨🚨🚨Exploit Alert Chain: Ethereum Loss: $408,318.18 Target: 0xc851e5a046819b022091b50f05ae3bd052e034a4 Attack Attack Tx: etherscan.io/tx/0x81f9aeaa6… Summary: An attacker deployed 0x2196b3f31a43de49a2951c514488a8dd7c96ad67 and abused execute(uint256,address,uint256,bytes) on 0xc851e5a046819b022091b50f05ae3bd052e034a4 to pull 224,865 USDC and 183,453.18 USDT through 0x34be478993b60561c7c9f3b8a3851e9a3a15cd53 and 0x2a69893ec6d332101750eed731d52891717af671. Funds flow: 0x2196b3f31a43de49a2951c514488a8dd7c96ad67 forwarded both token balances to 0xdb2096ffceef50106c4457b12fc139d89d179cce. #DeFiSecurity #ETH #ExploitAlert


Root Cause
The root cause is that spool::user::update_points does not enforce pool-account binding or stake type consistency before calling spool_account::accrue_points.
In this incident, the attacker used a SpoolAccount created in spool 0x4f0ba970d3c11db05c8f40c64a15b6a33322db3702d634ced6536960ab6f3ee4(index = 1191219615), but updated its points using a different spool 0xeec40beccb07c575bebd842eeaabb835f77cd3dab73add433477e57f583a6787 (index = 891301263052871).
public fun update_points