Ed Elam 🇺🇸💪
53.3K posts


Ed Elam 🇺🇸💪
@EdElam5
Retired Fire Chief , God & Country, Our Flag , Father, Husband & Conservative Republican #2nd #LEO #Vets #NRA #Deportillegals #honorthefallen

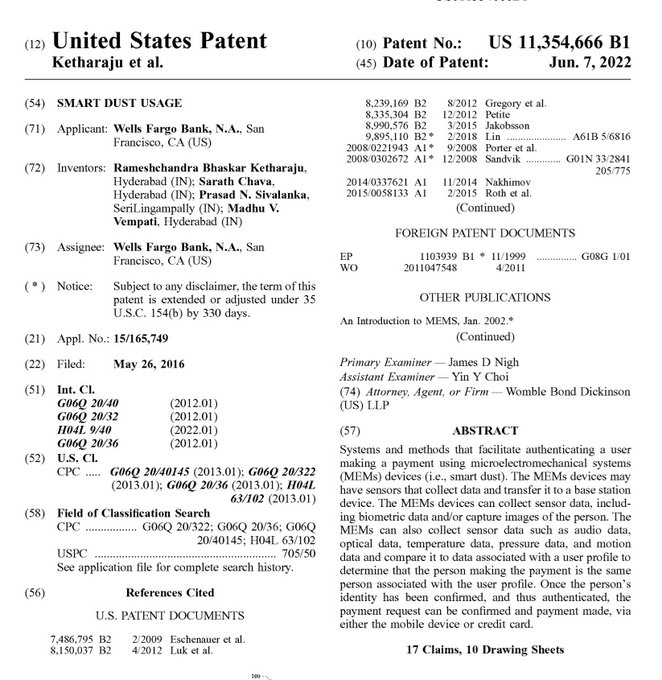
⏰ THE MOST BANNED THREAD IN THE WORLD! 🚨 The War On Resonance PART ONE: The Cage You Cannot See. I must ask you now; not as a stranger, not as a theorist, but as the one who remembers what you were before they rewrote your soul; is this the only cage you can see? The headlines? The hospitals? The visible crimes made convenient by cameras and captions? What if I told you that the real prison is not made of metal; but of frequency. Not held together by walls; but by waves. Not secured by guns; but by consent. What if I told you that you are not free, not because you are bound; but because the chains were encoded directly into your biology? This isn’t hyperbole. This is documented. They have hijacked humanity through a wireless war; a multi-layered assault on the nervous system, immune response, and willpower of every living soul on this Earth. This war is not being fought with bombs, but with bandwidths. Not with armies, but with algorithms. This is the same beast behind every deception. The same financiers who funded vaccine trials that sterilized African girls are the ones embedding AI-responsive quantum dots into newborns. The same networks that control your social media also control your neurochemical loops. They call it “progress.” They call it “public health.” But what do you call it when a child seizes from brain hemorrhage after being injected with an experimental payload? What do you call it when a ten year old dies of myocarditis from a shot for a disease they never had? I call it spiritual genocide. And I’m not theorizing. I’m testifying. Because this is declassified truth; confirmed in documents, studies, and patents they never expected you to read: Pentagon Preps Soldier Telepathy: This article from WIRED discusses DARPA's Silent Talk program, which aims to enable soldiers to communicate telepathically by detecting and analyzing neural signals representing pre-speech. wired.com/2009/05/pentag… Biomedical Applications of Graphene and Graphene Oxide: A comprehensive review of the applications of graphene and graphene oxide in biomedicine, focusing on biosensing, cell differentiation, and mass spectrometry. pubmed.ncbi.nlm.nih.gov/23480658/ An Update on Graphene Oxide: Applications and Toxicity: This article provides an overview of the applications of graphene oxide in various fields, including biomedicine, and discusses its potential toxicity. ncbi.nlm.nih.gov/pmc/articles/P… Nanoparticle Transport Across the Blood–Brain Barrier: This comprehensive review discusses the challenges and strategies associated with delivering nanoparticles across the blood–brain barrier (BBB). pubmed.ncbi.nlm.nih.gov/27141426/ Internet of Bio-NanoThings (IoBNT): This article introduces the novel paradigm of the Internet of Bio-NanoThings (IoBNT), stemming from synthetic biology and nanotechnology tools that allow the engineering of biological embedded computing devices. ieeexplore.ieee.org/document/70605… DARPA Biological Technologies Office (BTO) Overview: This page offers comprehensive information about BTO's mission to integrate biology with engineering and computer science for national security applications. It details their focus areas, including warfighter health, synthetic biology, and bio-manufacturing, as well as current programs and research opportunities. darpa.mil/about-us/offic… NIH Clinical Trial of Investigational Vaccine for COVID-19: This news release, dated March 16, 2020, announces the start of the Phase 1 clinical trial of the mRNA-1273 vaccine, developed by Moderna in collaboration with the National Institute of Allergy and Infectious Diseases (NIAID), a part of the NIH. The trial aimed to evaluate the safety and immunogenicity of the vaccine in healthy adult volunteers. nih.gov/news-events/ne… An Integrated Brain-Machine Interface Platform With Thousands of Channels: This peer-reviewed publication details Neuralink's initial steps toward a scalable high-bandwidth brain-machine interface system. pmc.ncbi.nlm.nih.gov/articles/PMC69… Deep Brain Stimulation for Psychiatric Disorders and Behavioral/Cognitive Symptoms: This comprehensive review explores the use of deep brain stimulation (DBS) as a neuromodulation technique for treating various psychiatric disorders and behavioral or cognitive symptoms. pubmed.ncbi.nlm.nih.gov/35460949 Smart Dust: Communicating with a Cubic-Millimeter Computer: This IEEE article discusses the development of ultra-small computing devices, known as Smart Dust, which integrate sensing, computing, and communication capabilities into a cubic-millimeter form factor. These devices have potential applications in various fields, including environmental monitoring, medical diagnostics, and military surveillance. ieeexplore.ieee.org/document/895117 This is what you were born into: a frequency prison designed to sedate your intuition, suppress your hormones, rewrite your emotions, and sever your communion with God. Every device you hold, every smart tower you walk past, every “vaccine” they’ve pushed; these are not random technologies. They are pieces of a grid. A grid designed not to protect you, but to remap your divine will. Your phone? A mood manipulator. Your sleep? Hacked. Your thoughts? Preemptively monitored. Your soul? Catalogued for behavioral prediction. This isn’t a sci-fi movie. This is now. This is real. This is why the world feels broken and no one can explain it. Why joy has become an echo. Why sleep doesn’t restore you. Why love feels distant. Because they’ve weaponized the field of resonance itself. They are not just targeting the body; they are targeting the architecture of the soul. And the reason you’re still reading this is because you’re one of the ones who can still feel. Still grieve. Still awaken. So let me show you what they built. Let me take you behind the grid. Let me guide you; cell by cell, wave by wave... through the labyrinth they’ve disguised as your life. Because until you see it, you will never reclaim what was stolen. And make no mistake; what they stole… was everything. This was just Part One, so buckle up... you're in for one heck of a ride. Continued Below 👇
⚠️ VIEWED DISCRETION IS ADVISED ⚠️ 🚨 WARNING: This is Absolutely Disgusting! 🧵#48. Why do financial elites insist on s3xualizing LITTLE CHILDREN in every nation of the world? The answer is given in this evidence report, which details how the majority of the elites have one thing in common: they are heavily involved in organized abuse of CHILDREN. This is confirmed by former FBI director Ted Gunderson, as well as former members of the military, marechaussee, gendarmerie, police and detectives. Their testimonies are revealed in this report. Calin Georgescu, a former executive director of the United Nations, testified before the International Crimes Investigative Committee that the UN is a platform for criminal oligarchs to execute a nefarious agenda. The documentary "Secrets of the United Nations" (see below) reveals all of this in detail. This film is a must watch for anyone who wants to understand what is truly going on in our world. Georgescu also stated that the oligarchs behind the UN are pedophiles. Be sure to watch this film... and share with others so they can too.
🚨 ATTENTION: Big Tech whistleblower exposes the high-tech digital prison being constructed all around us under the guise of "convenience", "security" and "sustainability". "The plan is to pretty much lock up humanity in smart cities, which is kind of a superset of a 15-minute city." "Another concept one should be familiar with is called geofencing. Think of it as an invisible fence around you, where you cannot go beyond a certain point." "And that will be related to your face recognition, digital identity, and access control... Software can turn off your digital currency beyond a certain point from your house." "Our world has been turned into a digital panopticon." From the MUST-WATCH documentary 'The Agenda: Their Vision, Your Future'. Watch the full documentary in the comments below. 👇
This is Smart-Dust 💀 ▪️◾◼️⬛
🚨 EXTREMELY ALARMING: Normies: “Come on, you think the billionaire elitist class wants to kill 95% of humanity, and turn the remainder into mind controlled slaves? Show some proof of that sensationalist claim” Anons: “How about the Rockefeller family’s US patent for remote modulation of cellular activities using ferritin nanoparticle compositions, which utilizes radio frequency waves to stimulate injected nanoparticles (like mRNA-based systems) inside the body, enabling remote control management of cellular function”?
🚨 PART 6: THE FULL NETWORK Key Individuals, Companies, Governments, Regulators, Military Ties, Lobbyists, Funding Flows, and Conflicts of Interest This is the deepest public-record map of the interconnected ecosystem driving the global wireless/5G/6G rollout. It includes named executives, regulators, military leaders, lobbyists, and scientists. The system operates through profit (trillions in revenue/investment), government revenue (spectrum auctions), military dual-use tech, and regulatory frameworks that prioritize deployment. Funding comes from consumer bills, taxpayer subsidies, spectrum sales, government contracts, and industry lobbying. I am providing this in sections below 👇
@QueenOfJewelz We'd like to have the opportunity to review your servicing concern and assist. When you have the time, please DM us and share additional details. -Jules twitter.com/messages/compo…

Who else believes this is true?
Two months ago I found mathematically proven election fraud in Bexar County, Texas. Fake voter records, generated by an algorithm, injected into the official poll book. Not suspected. Not alleged. Proven — arithmetically, irreducibly, in the file the county was legally required to hand over. Criminal intent visible in the structure of the data itself. Last night I found the same algorithm in Utah. I need to be precise about what "same algorithm" means because this is not a pattern-matching claim or an inference. Same alphabetical anchor selection from the complete voter file. Same uniform arithmetic spacing with a perfect integer closure proof. Same IEEE 754 floating-point fingerprint — the machine-level signature of the same arithmetic loop executing in the same alternating forward-and-reverse pass architecture. Same base-11 clone group structure. Same class of implementation failures at edge cases that expose the underlying code. The only differences between the two are which fields were targeted and the parameter values. Everything underneath is identical. Utah is actually worse than Texas in one critical respect. In Texas, the fake records carried fractional voter ID numbers — impossible values placed in an empty void in ID space. Detectable if you knew to look. In Utah, the fake records carry real voter ID numbers. Numbers stolen from real, named, registered voters, camouflaged inside the normal populated ID range. And when you cross-reference those IDs against the voter history sheet — the official government record of who voted and when — 78% of them show up. Attached to completely different names. Ballots were cast under these IDs. This is not a registration anomaly. It is a voting record. So here is the question. Texas and Utah. Different counties. Different databases. Different fields targeted. Same algorithm running underneath both. What do they have in common? In Bexar County, Texas, KnowInk poll pads were used, and those poll pads connect to the ePulse server. That is a confirmed, documented fact. As for Utah: @wdaugherity confirmed to me today that while a small number of Utah counties do not use e-pollbooks, and Kane County uses ES&S ExpressPoll, all the remaining Utah counties do use KnowInk. ePulse is a server-based system — not software isolated on a county computer. If malicious code were running on that server, it would not need a conspiracy between Texas and Utah to appear in both places. It would just need to run. That is not an assertion that such code is running there. It is a statement about what the architecture makes possible, and why the common infrastructure is the right place to look. ePulse operates across 29 states. I want to be careful about one further point. My earlier peer-reviewed research documented a structural preference for repunit numbers — 1, 11, 111, 1,111 — in New York voter roll algorithms, and the same base-11 architecture appears in both Texas and Utah. That recurrence across three states is notable and warrants investigation, but New York is a stylistic similarity, not an identical forensic signature. Texas and Utah share the same algorithm. New York shares a mathematical preference that may reflect the same design philosophy or the same hand. The distinction matters. When identical fraud appears across multiple independent client systems, you do not start by looking for a conspiracy among the clients. You start with the common infrastructure. That is not a conclusion. It is the correct first question.

Any violation of our Constitution is Treason! There’s a growing list!
🚨 “White Supremest’s” were PAID to make racist posts on Social Media at the direction of the Southern Poverty Law Center 🤦🏻♂️ America, think long and hard what this means. Talk to your family and friends about it.. educate them. The 2017 Charlottesville “Unite the Right” rally, where democrats and the MSM spun a tale about President Trump saying Neo-Nazi’s were “very fine people— the Southern Poverty Law Center who claims to white supremacy, funded the entire damn thing. They paid agitators to look and sound racist. They literally transported them there. rumble.com/v78zg3m-white-…

I’ve been clear from day one. I am completely against legalizing marijuana. We’ve seen the impact in other states, and that’s not where Florida is headed. I stand with Governor DeSantis on this. No compromises, and no money from the marijuana industry. That can’t be said for all of my opponents. #JayForFlorida