Br*an
16.3K posts

Br*an
@SecurityCollins
☁️ security, general technology fan • opinions = mine
Bergabung Ocak 2021
4.3K Mengikuti454 Pengikut

Moved my retirement accounts to Robinhood last year bc of their asset match (like 3% match on all assets or something like that?)
But it’s incredibly annoying that you have to scroll past prediction markets (read: sports betting) to see portfolio positions.
The forced sports betting is gross.
English

.@grok does Jay Leno have a CDL?
Sawyer Merritt@SawyerMerritt
Here is Jay Leno driving the new redesigned @Tesla Semi. He is the first person outside of Tesla to drive it. @danWpriestley: "This truck from an energy standpoint is 50% cheaper to run here in California. Across the US, we're 20% cheaper on a per mile basis, and that's inclusive of everything, not just energy, whether that's reduced maintenance, fuel." via @LenosGarage
English
Br*an me-retweet

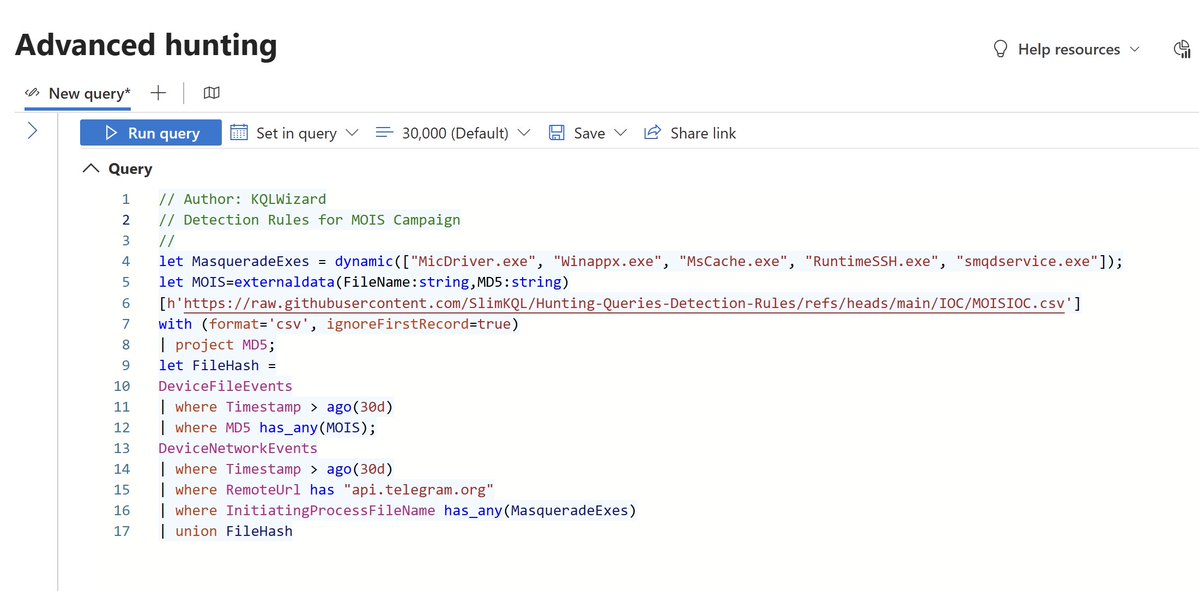
Turning Threat Intel Into Defense: Detection Rules for MOIS Campaign
The FBI warns that Iranian Ministry of Intelligence and Security (MOIS) cyber actors are using Telegram bots as command-and-control infrastructure to deliver malware disguised as legitimate Windows applications, targeting dissidents, journalists, and opposition groups worldwide. This multi‑stage malware enables persistent access, data theft, and exfiltration of files, audio, and video, with groups like Handala Hack and Homeland Justice linked to these campaigns. The FLASH provides indicators of compromise and urges defenders to apply updates, use trusted sources, enable antivirus, and report suspicious activity to the FBI.
Source: ic3.gov/CSA/2026/26032…
KQL Code:
github.com/SlimKQL/Detect…
#Cybersecurity #DefenderXDR #MOISCampaign
English
Br*an me-retweet

Microsoft Threat Intelligence has observed threat actors actively experimenting with techniques to bypass or “jailbreak” AI safety controls.
By reframing malicious requests, chaining instructions across multiple interactions, and misusing system‑ or developer‑style prompts, threat actors can coerce models into generating restricted content that bypasses built‑in safeguards. These techniques demonstrate how generative AI models are probed, shaped, and redirected to support reconnaissance, malware development, and social engineering while minimizing friction from moderation.
AI guardrails have become dynamic surfaces that attackers test and manipulate to sustain operational advantage. As AI becomes more deeply embedded in enterprise workflows, understanding how attackers test and manipulate these guardrails is critical for defenders. Learn more about securing generative AI models on Azure AI Foundry: msft.it/6013Qs5oX
English
Br*an me-retweet

Two free AI security tools every security team should bookmark right now.
declawed.io - SecurityScorecard's STRIKE team built this. Live dashboard tracking 390,000+ exposed OpenClaw instances globally, updated every 15 minutes. 243,000+ still live and reachable, 35.4% vulnerable to RCE. Some exposed IPs correlate with infrastructure attributed to nation-state actors including APT28 and Sandworm.
radar.protectifyai.com - ShadowAI Radar tracks the broader AI attack surface most people don't know exists. Right now it's showing 1,231 exposed AI endpoints across OpenClaw, Ollama, Open WebUI, Dify, Flowise, and more - plus 720 leaked AI credentials on GitHub, 7.3% with corporate signals. It covers 216 active CVEs across the entire open-source AI tooling ecosystem with exploit status, CISA KEV tracking, and a live feed showing new unauthenticated instances appearing globally in real time. The OpenClaw deep dive alone shows 98.9% of tracked instances have no authentication and 53.5% are vulnerable to remote code execution.
declawed.io shows you the OpenClaw exposure. Radar.protectifyai.com shows you the entire AI infrastructure attack surface - endpoints, credentials, CVEs, and supply chain risks in one place.
Both free.
Both should be on every CISO's screen this week.
English
Br*an me-retweet

@SenTedCruz Big, stupid, glaring “if” in there. Insanely dumb, even for you
English
Br*an me-retweet

🚨 Think you’ve locked down MCP Server connectors in Copilot Studio? Think again.
It actually requires control across two admin centers and that’s where most gaps happen.
In this video, I walk through roles, setup, and a full demo to help you get it right.
🎯 What you’ll learn:
The roles required (and where people often get stuck)
How settings differ between MAC vs PPAC
A step-by-step walkthrough
A live demo showing how it all comes together
🎥 Watch here: youtu.be/ALoK0EPVDpg
Watch 👀 or bookmark 🔖, learn 🧠 and share🥰.
#MCP #AI #Governance #EnterpriseAI #CopilotStudio #PowerPlatformn #Microsoft365
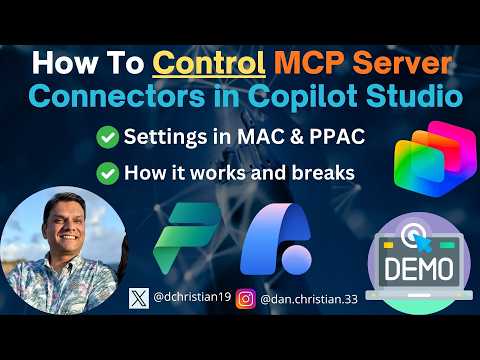
YouTube
English
Br*an me-retweet

@Wrightslake @carlquintanilla @GettyImages @CNBC He’s looking at boobs or Facebook from his phone. This isn’t TDS, just basic critical thinking lmao
Be serious
English

@carlquintanilla @GettyImages Yea thats why they are there to roam the airports and look for things suspicious therefore freeing up TSA agents to check passengers. They took over one part of TSA duties. You really have let your TDS get out of hand. You once were a decent reporter @CNBC
English
Br*an me-retweet

A threat actor is claiming to sell a major breach of OVHcloud - one of Europe's largest cloud hosting providers. 1.6 million customer records. 5.9 million active websites. Website code, databases, and server configurations. All allegedly for sale on a dark web forum.
Unconfirmed. But worth watching closely. Here's why.
(Thanks DarkWebinformer for flagging this)
If this is real, the claimed attack vector is access through a parent account - meaning administrative-level credentials that gave the attacker visibility across the entire hosting infrastructure, not just one customer.
That's the management-plane pattern we've been seeing all month. Cisco FMC. Microsoft Intune. Oracle EBS. Attackers aren't going after individual systems anymore. They're going after the platforms that manage them. Compromise one admin account and you get access to thousands of customers simultaneously.
OVHcloud hosts 5.9 million websites. That's 5.9 million potential supply chain entry points. Website code and server configurations aren't just data - they're the keys to understanding how those sites work, what vulnerabilities exist, and how to compromise them downstream.
For any organisation hosted on OVHcloud right now:
→ Rotate admin credentials immediately - don't wait for confirmation
→ Review access logs for unusual parent-account activity
→ Audit your server configurations for anything that shouldn't be public
→ Assume your database connection strings and API keys stored in server configs are compromised
The seller hasn't set a minimum price and is offering 30% commission for referrals. That tells you something about the volume - they're trying to move this fast.
This is still unconfirmed. But the claimed scope - 1.6M customers, 5.9M sites, full code and database access - would make this one of the largest cloud hosting breaches in European history.
Watch this space.
English


@EODHappyCaptain Will police officers get purple hearts too now? Firemen? I approve honoring their brave and swift action but not with combat awards.
English

@Pickza10 @Richwiedis Markets like rational policy decisions that don’t change by the minute
English