Victor
253 posts




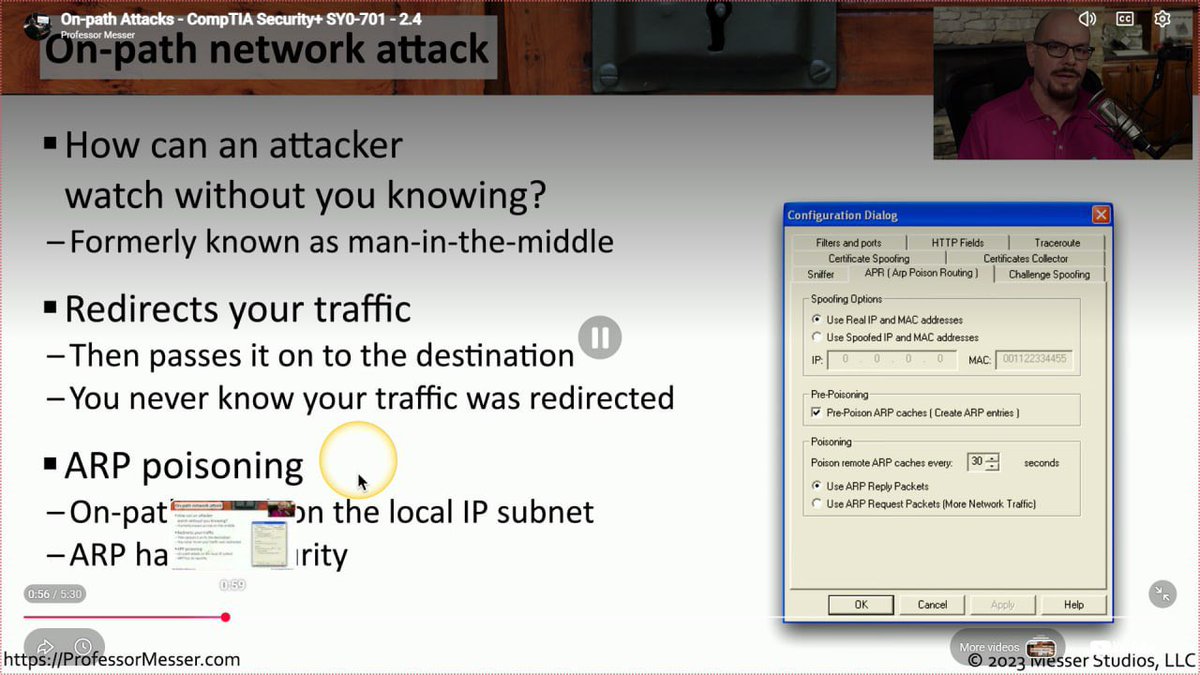
Day 92/100days challenge. Today I covered; Wireless Attacks, On-path Attacks (MiTM), Replay Attacks, and Malicious Code on my Security+ study. Also on TryHackMe, I completed a room on the Pyramid Of Pain. I learnt how it is used to improve the effectiveness of Cyber Threat Intelligence (CTI), Threat Hunting, and Incident Response exercises. Also, how different threat indicators affect attackers differently (From the simplest to the most complex). tryhackme.com/room/pyramidof… @ireteeh @OnijeC @jay_hunts @segoslavia @commando_skiipz @RedHatPentester @Officialwhyte22 @TemitopeSobulo @_DeejustDee @cyberjeremiah #BlueTeamer #100dayscybersecurity


Day 91/100days challenge. In my Security+ study today, I covered; Other Malware Types (Keylogging Malware, Logic Bomb, Rootkits), Physical Attacks, Denial of Service (DoS), and DNS Attacks. On TryHackMe, I completed a room on Introduction to SOAR (Security Orchestration, Automation and Response). I learnt how SOAR integrates multiple security tools to automate tasks and respond to incidents more efficiently using playbooks. tryhackme.com/room/soar?utm_… @ireteeh @OnijeC @jay_hunts @segoslavia @commando_skiipz @RedHatPentester @Officialwhyte22 @TemitopeSobulo @_DeejustDee @cyberjeremiah #BlueTeamer #100dayscybersecurity


Day 90/100days challenge. Today in my Security+ study, I covered; Zero-Day Vulnerabilities, An Overview of Malware, Viruses and Worms, Spyware and Bloatware. Also on TryHackMe, I completed a room on Elastic Stack: The Basics. I learnt how Elastic Search (ELK) can be used for log analysis and investigation. Also did a hands-on exercise exploring how ELK helps in searching and analyzing log data efficiently. tryhackme.com/room/investiga… @ireteeh @OnijeC @jay_hunts @segoslavia @commando_skiipz @RedHatPentester @Officialwhyte22 @TemitopeSobulo @_DeejustDee @cyberjeremiah #BlueTeamer #100dayscybersecurity




Day 88-89/100days challenge. Yesterday I rested. Today I continued with my Security+ study in which I covered Cloud Specific Vulnerabilities, Supply Chain Vulnerabilities, Misconfiguration Vulnerabilities and Mobile Device Vulnerabilities. Also on TryHackMe, I completed two rooms on Introduction to SIEM and Splunk: The Basics. I learnt how a SIEM is used to collect, normalize and correlate logs from various devices across a network. Also I did a hands-on practice of how Splunk works and how data can be uploaded and analyzed. tryhackme.com/room/introtosi… tryhackme.com/room/splunk101… @ireteeh @OnijeC @jay_hunts @segoslavia @commando_skiipz @RedHatPentester @Officialwhyte22 @TemitopeSobulo @_DeejustDee @cyberjeremiah #BlueTeamer #100dayscybersecurity




Day 87/100days challenge. Today in my Security+ study, I learnt about SQL Injection, Cross-Site Scripting (XSS), Hardware Vulnerabilities, and Virtualization Vulnerabilities. Also On TryHackMe today i completed a room on Introduction to EDR (Endpoint Detection and Response). I explored how EDR solutions monitor endpoints, collect telemetry, detect suspicious behavior, and help security analysts investigate and respond to threats effectively. tryhackme.com/room/introduct… @ireteeh @OnijeC @jay_hunts @segoslavia @commando_skiipz @RedHatPentester @Officialwhyte22 @TemitopeSobulo @_DeejustDee @cyberjeremiah #BlueTeamer #100dayscybersecurity