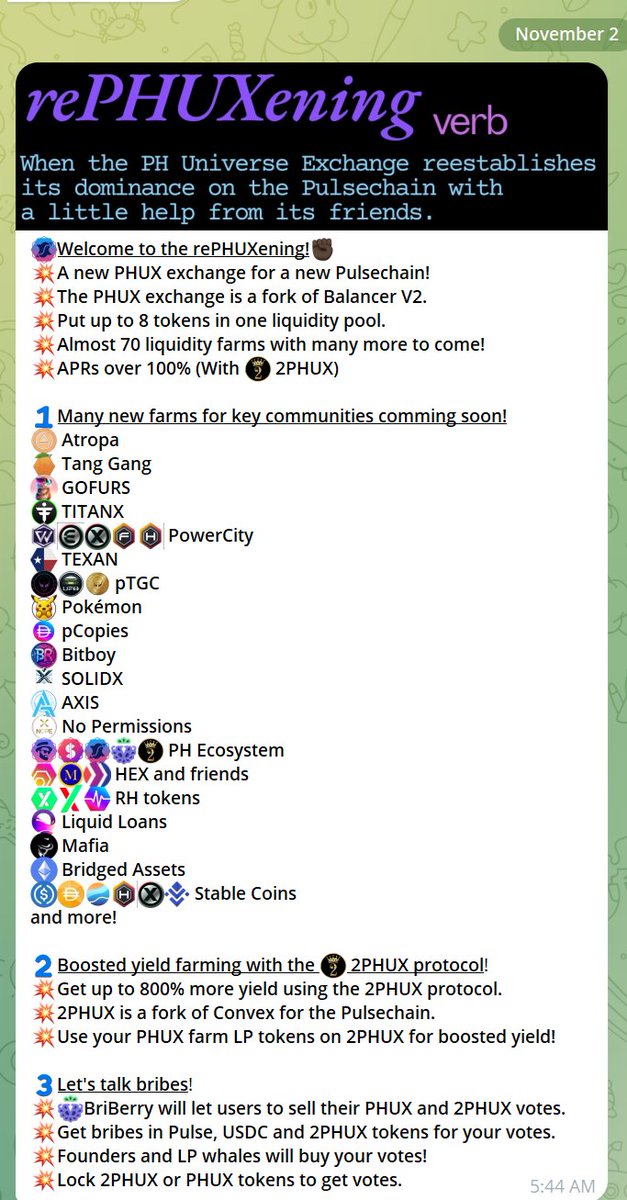
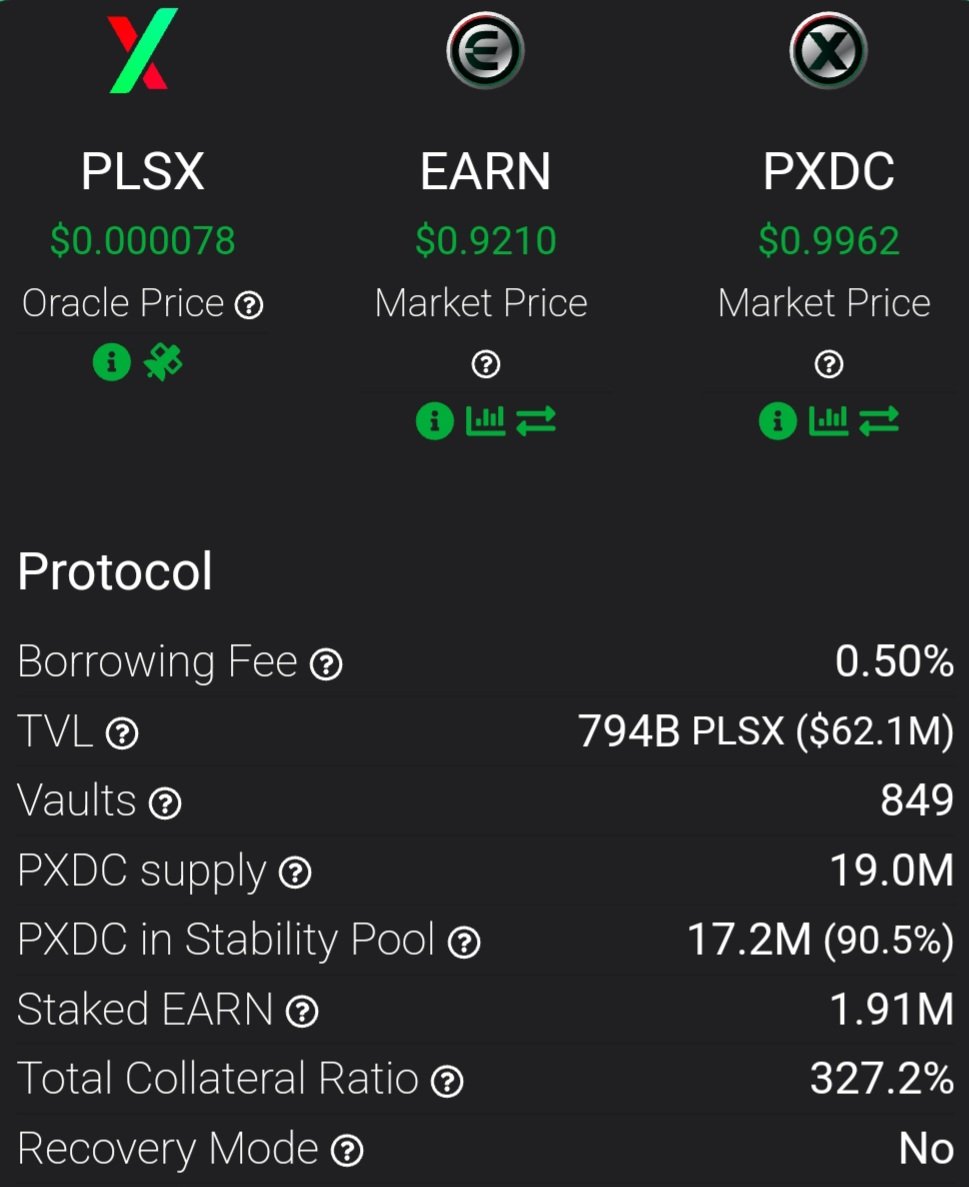
Current assessment of Balancer Exploit as it pertains to Phux.io We do not believe manageUserBalance itself is the universal attack vector that makes all Balancer-style forks or pools vulnerable. Our analysis indicates that the recent exploits primarily relied on invariant manipulation in composable-stable-type pools, exploiting rounding and scaling interactions inside the pool math. Most balancer pools are not affected by this mechanism. The risk appears limited to stable pools that combine non-unit rate providers, ERC-4626-style wrappers, or other custom scaling factors—configurations where token scaling is dynamic or fractional rather than fixed by simple decimals. Fortunately, we have been very conservative in the types of pools we have allowed on the platform eschewing complexity from Day 1. Our own stable pools use only straightforward decimal normalization (powers-of-ten scaling), so we have not identified any evidence of the same vulnerability in our deployments. We note that we are not aware of any similar Balancer pools being exploited. An example of which is this Balancer pool on Arbitrum: balancer.fi/pools/arbitrum… Another on ETH balancer.fi/pools/ethereum… For our pools to be vulnerable then these pools would need to be as well. Nonetheless, we are reviewing all pool math paths and monitoring for any edge-case deviations to confirm this assessment, and we will update the community promptly if new information arises. We will keep studying this and update you with anything we find. -PH Team