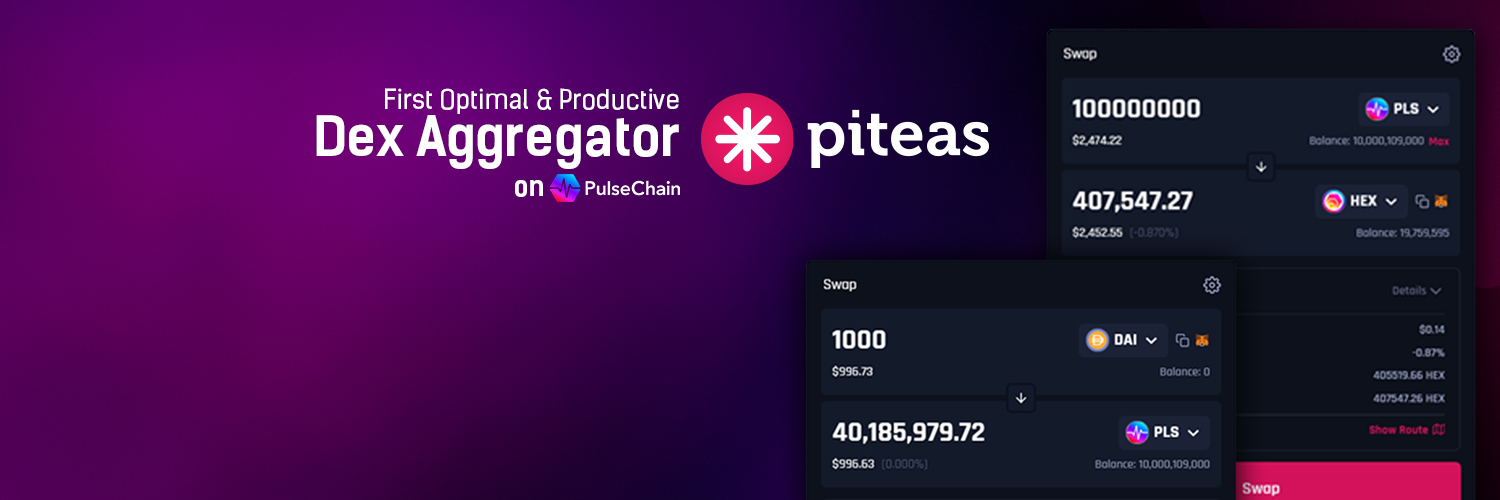
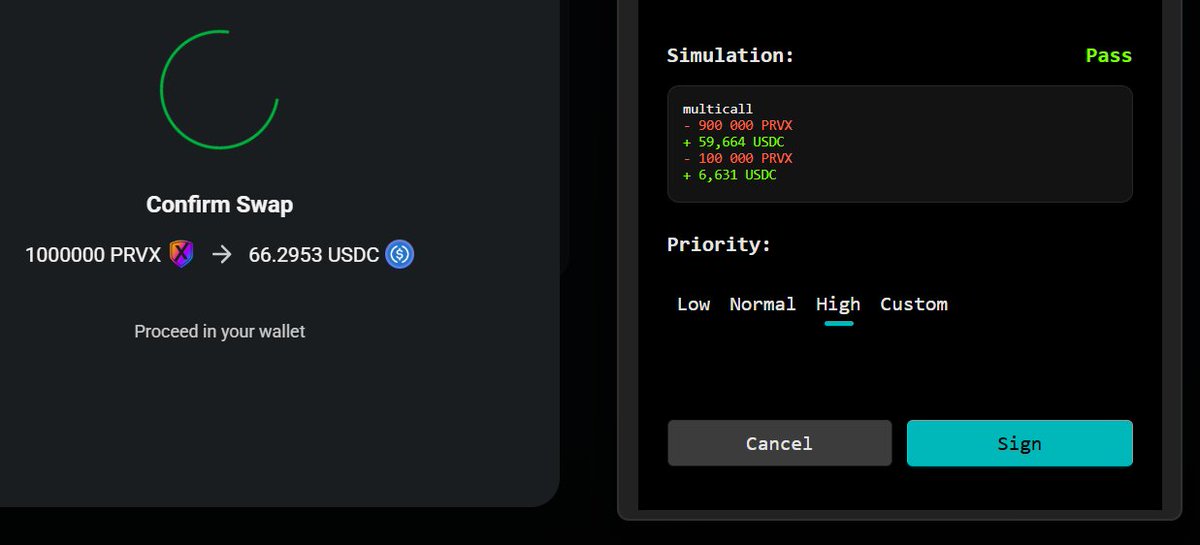
Occasionally, if you trade coins that have deprived PulseX of buy and burn by putting their liquidity somewhere else, you can get better order execution using piteas dot io. They're an order aggregator that combines liquidity from places outside PulseX. But for instance, if you're trading stable or weth for PLS, PLSX, HEX it's basically the same, except for infrastructure risk. You have to actually check what you receive as well, because some estimates aren't as good as others. Thus it's nice to have an aggregator for weird coins, but sucks a bit that it starves PLSX of buy and burn. Attached are some tests showing routes.