One of the most dangerous new attack techniques at @OneRSAC this week is the pace gap: adversaries are operating at machine speed.
The barrier to entry for machine-speed attacks has collapsed. GTG-1002 proved it: Chinese state actors running Claude Code with MCP for autonomous recon and lateral movement across 30+ targets, at rates Anthropic's own team called physically impossible for human operators. (The CCP ran the proof of concept. I'll take the validation.)
The answer is not faster humans. The answer is AI-augmented defenders, which means matching AI speed with AI speed.
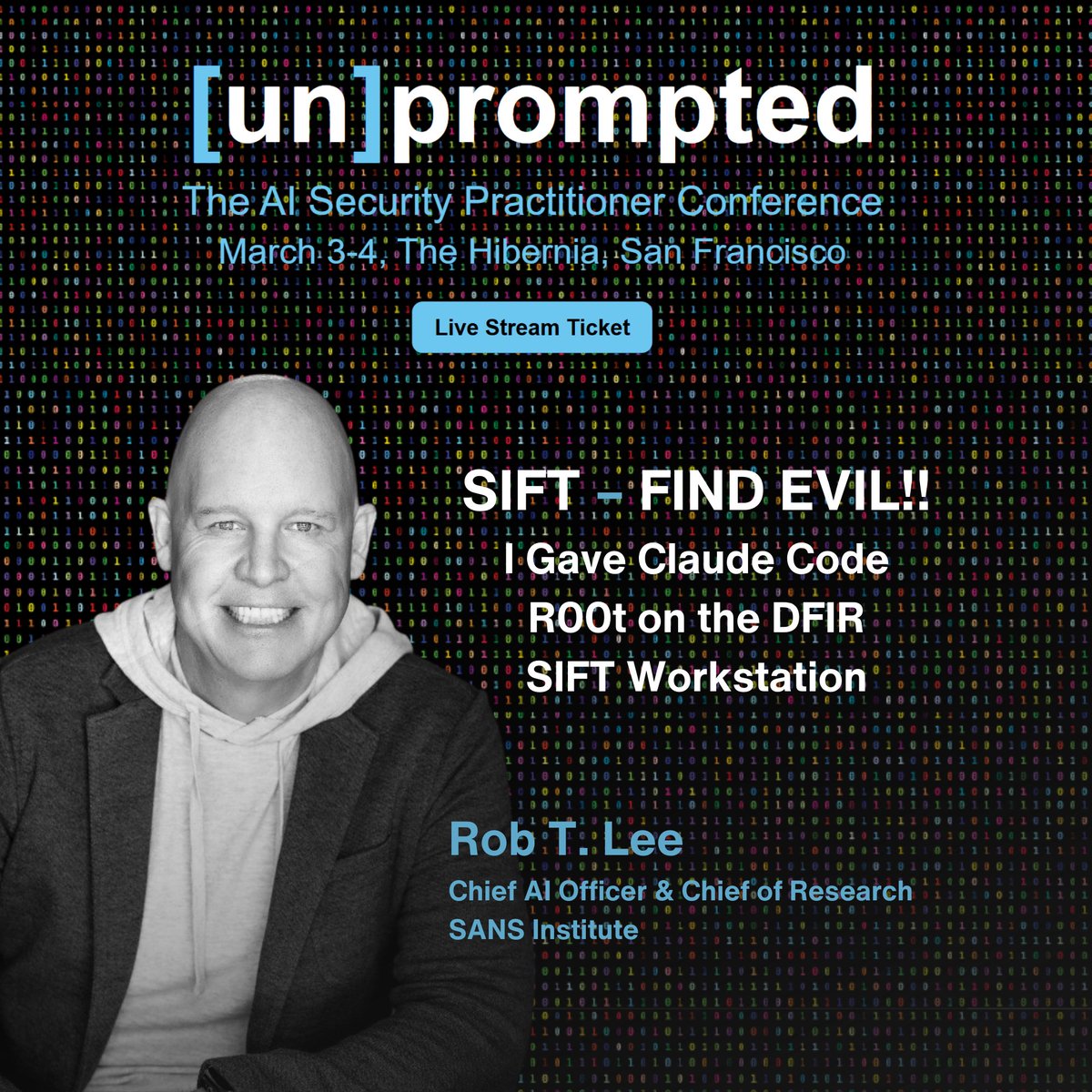
At the AI security practitioner con [un]prompted, I typed two words, "find evil," and fourteen minutes twenty-seven seconds later had a complete C drive analysis. (I know it was accurate. I ran the intrusion myself.)
The tool handles the syntax so the investigator can focus on what actually requires a human: reading the findings and driving the case. Only someone who knows DFIR can interpret that output.
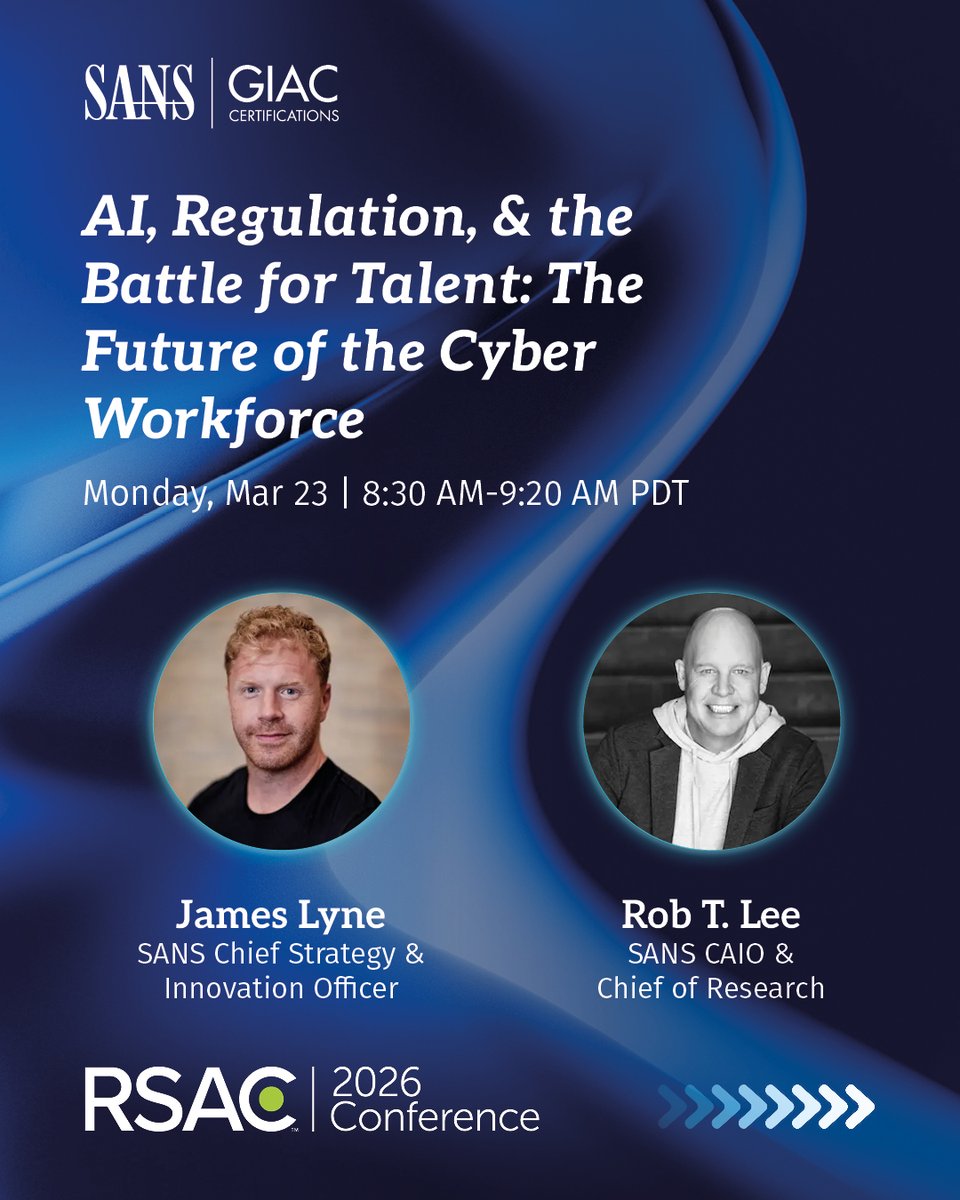
The full case gets made at the @SANSInstitute "Five Most Dangerous New Attack Techniques" panel at RSAC, Moscone West, Tuesday, 3:55 PM PT. I'll share more about the Find Evil! Hackathon ($22K+ in prizes, April launch) to get the entire defender community building on this together.
Offensive teams have a handful of developers working in secret. We have the open source community. Let's go.
English