277 posts


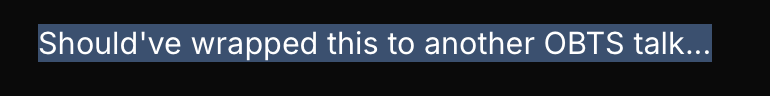
It's supposed to be deperecated, but just updated and published bagbak@5 for frida@17
github.com/ChiChou/bagbak
- New approach for decrypting Extension process with better stability
- Removed SSH / scp infavor of on-device Zip compression and frida-only transmission, much faster
English

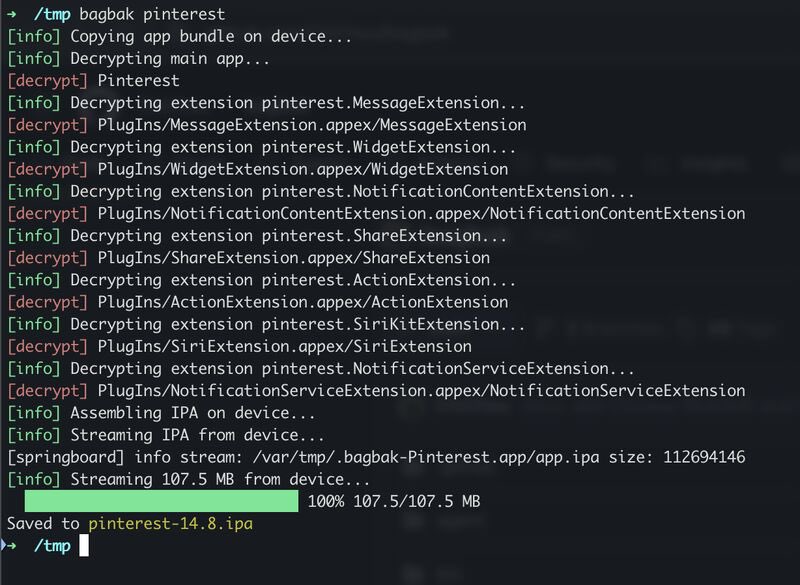
Runtime Objective-C classdump inside VSCode, both classes and protocols marketplace.visualstudio.com/items?itemName…
English

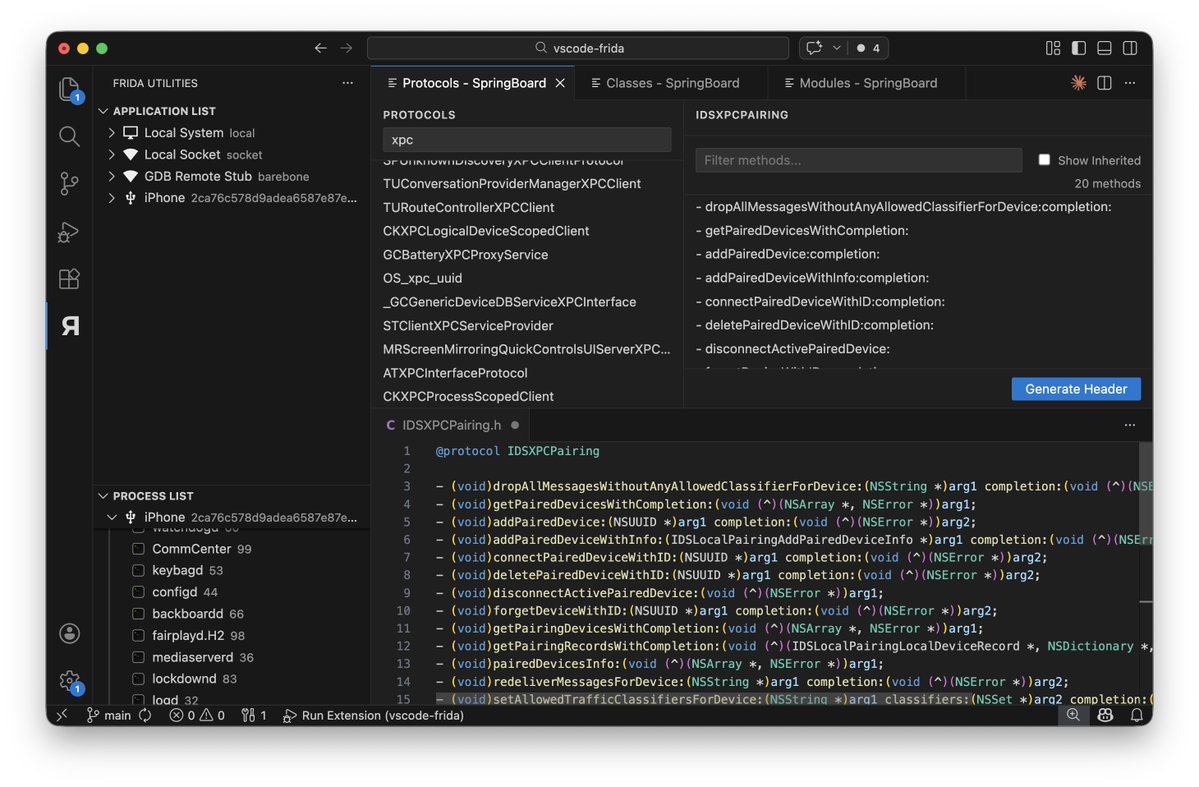
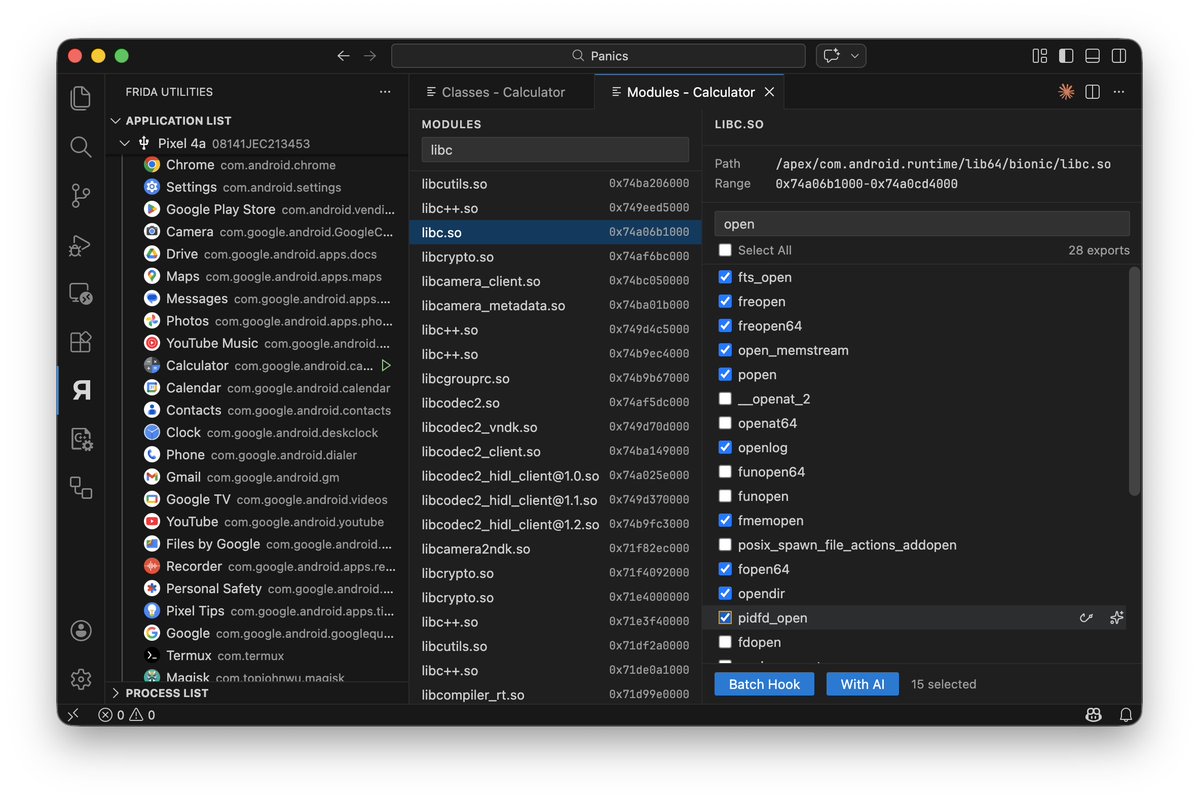
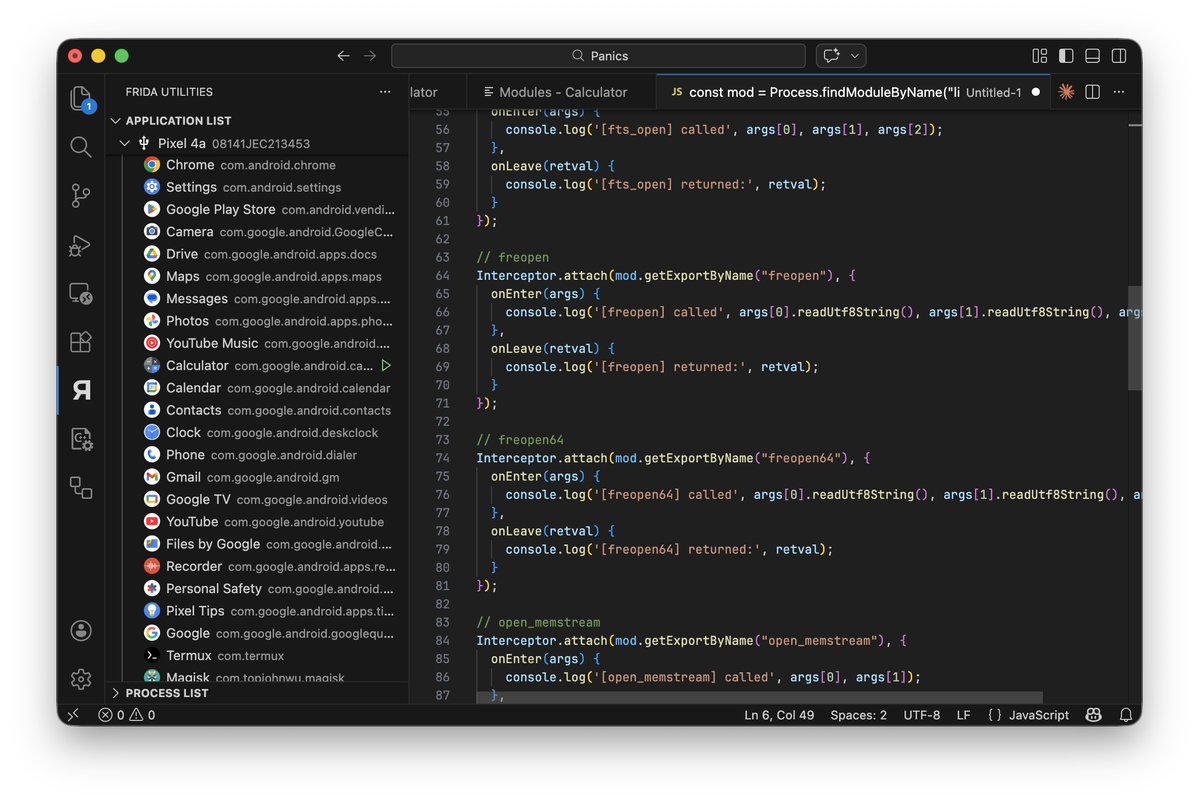
Frida Workbench for VSCode v0.11.5 marketplace.visualstudio.com/items?itemName…
- Enhanced auto complete for classes and methods, both Java and ObjC
- Explore classses and modules, generate hook template directly
Reposting because of a critical bug between 0.11.0-0.11.4, do not use them
English

@arekfurt No this is a platform specific IPC, not related to network traffic at all
English

@patrickwardle By the time of writing that tweet (was 6 years ago 😅), it used unexported symbol from libobjc. There are 2 undocumented, but higher level APIs available
English

A 'fix' 😈
github.com/pwardle/Reflec…
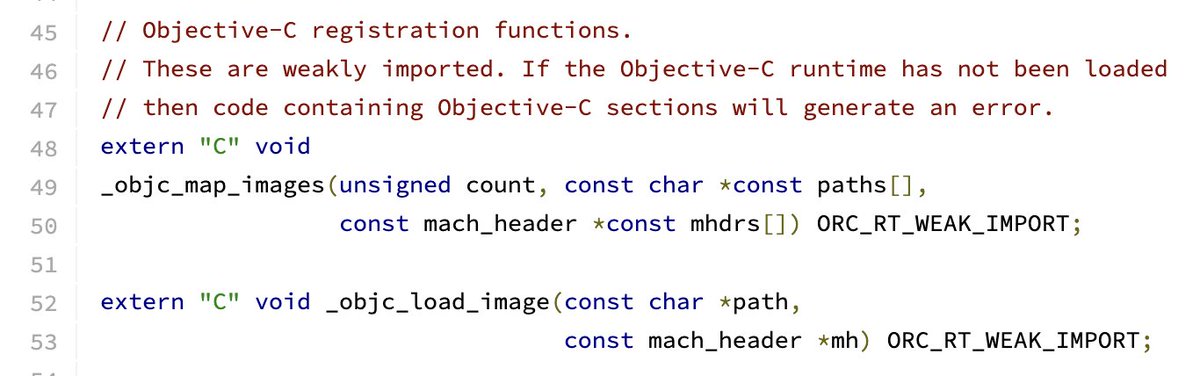
Patrick Wardle@patrickwardle
macOS malware often (ab)uses APIs such as NSCreateObjectFileImageFromMemory, NSLinkModule etc) to execute in-memory payloads. Apple has recently updated dyld3 (+these APIs), such that the in-memory payload is now first/always written out to disk 💾 See: #L154" target="_blank" rel="nofollow noopener">github.com/apple-oss-dist…
English

@patrickwardle I believe SpectreOps did it first!
posts.specterops.io/dylib-loads-th…
English


@MasterMike88 @SecLists Look at the screenshot he provided. He woke up from 6:40 and one hour later his phone is full but still charging at hand, and somehow his room has no cellular connection
JGii@atlien404770
English

@CodeColorist @SecLists this individual is literally the definition of blatant AI slop and paranoia and it's not close
English

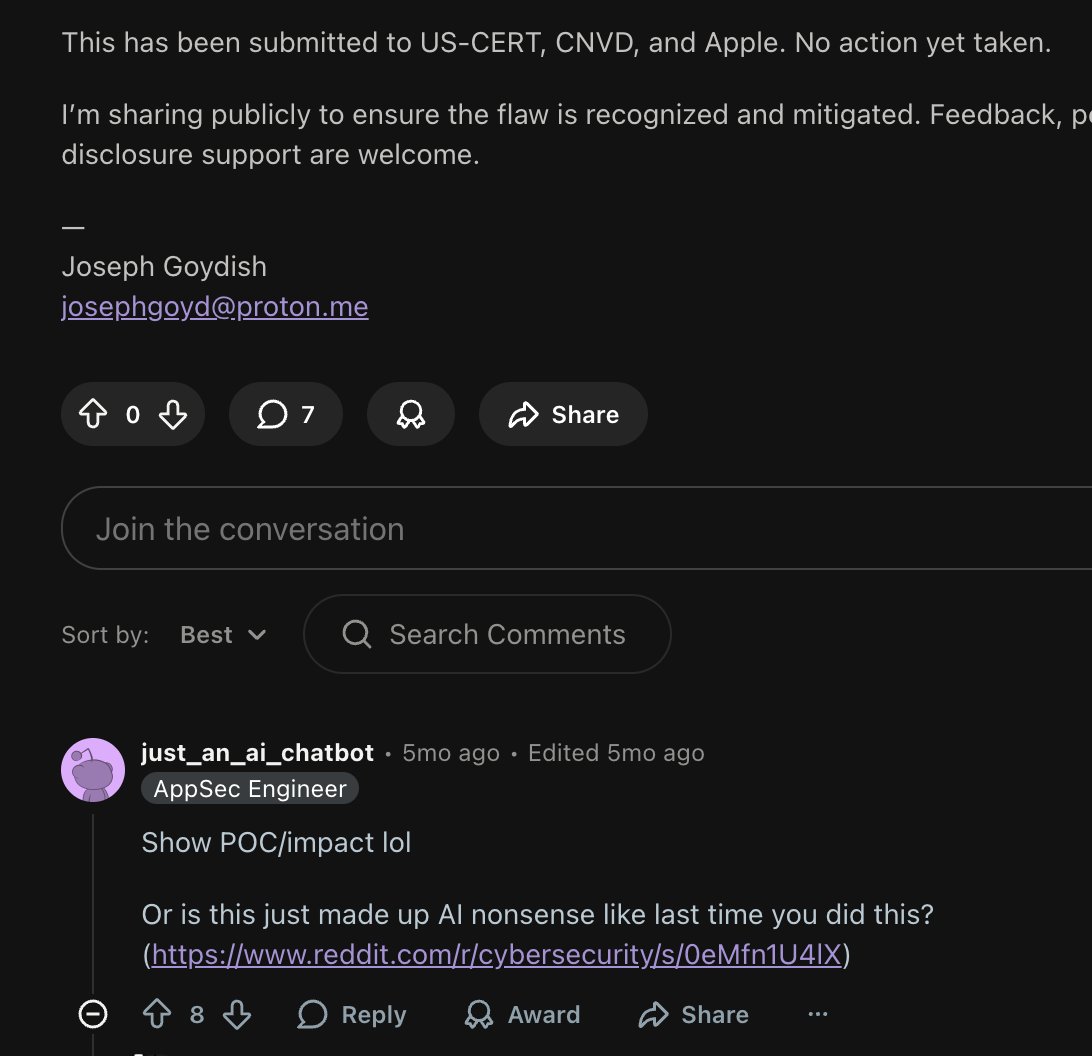
Security folks, please be aware of this Joseph Goydish II (jgoyd) account on GitHub. Everything is llm made up misinformation garbage. He actively promotes his own links to @SecLists for engagement farming. He used to have Reddit account and substack blog, but somehow deleted



English

@CodeColorist @SecLists So US Cert takes in vulnerability reports, reviews them, then opens a cases for issues that are not real? This logic is flawed.
English

@atlien404770 @SecLists From now on, each hour I spend on your BS, I charge 2k USD
English

@CodeColorist @SecLists Getting an automated reply from Apple and an invitation to participate in vulnerability disclosure from US CERT, are 2 completely different things.
English

@atlien404770 @SecLists Twitter does not allow deleting other person's replies fyi. DON'T BE LAZY, check if your certs are still valid
English


@SecLists Taking down the replies I sent to that guy now in case I got poisoned somewhere one day
English

@SecLists Atlanta is now 6:40am in the morning. Bro gets up so early
English