
Julian Derry
4.6K posts

@CyberSamuraiDev
Digital Frosenics | Cybersecurity | Manchester United


I get your point, but this still pushes people toward reusing the same password, which is where the real risk is. 1.Compromised passwords don’t only come from breaches. People reuse them on random sites, fall for phishing, or even expose them themselves (sticky notes, saved files, etc. 2. Saying a password is “safe to use for all” because it’s complex is misleading. Once that password is exposed anywhere, attackers don’t need to guess it, they just try it across multiple platforms. At that point, every account using it is at risk. So the issue isn’t how complex the password is. It’s reuse. Even a strong password becomes a single point of failure if it’s used everywhere.
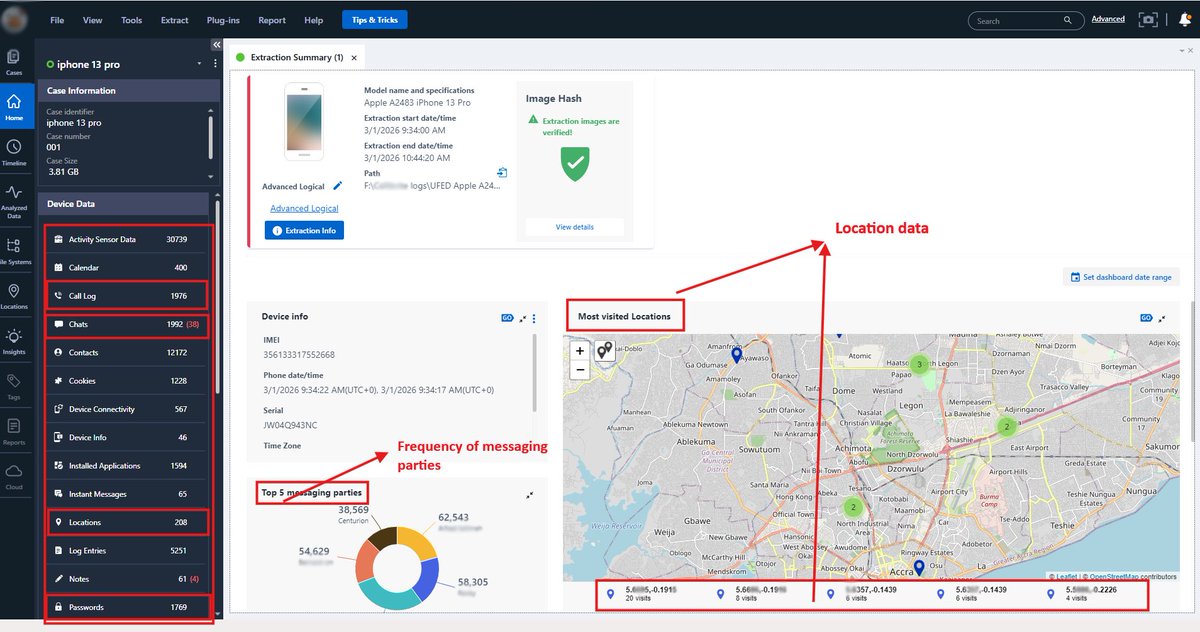
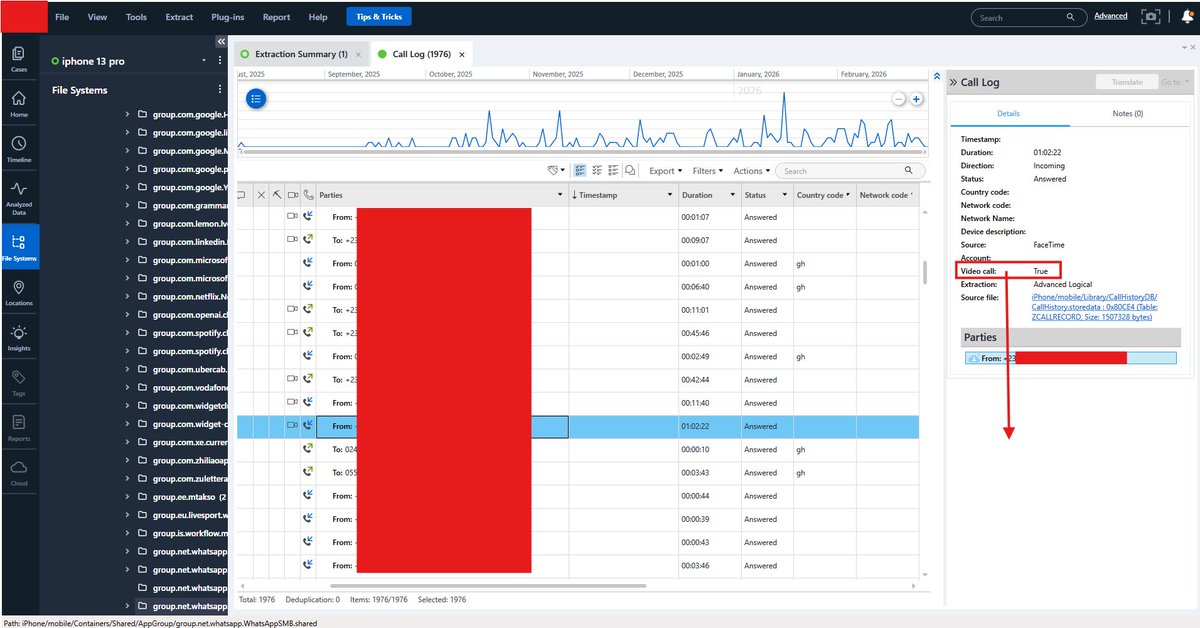
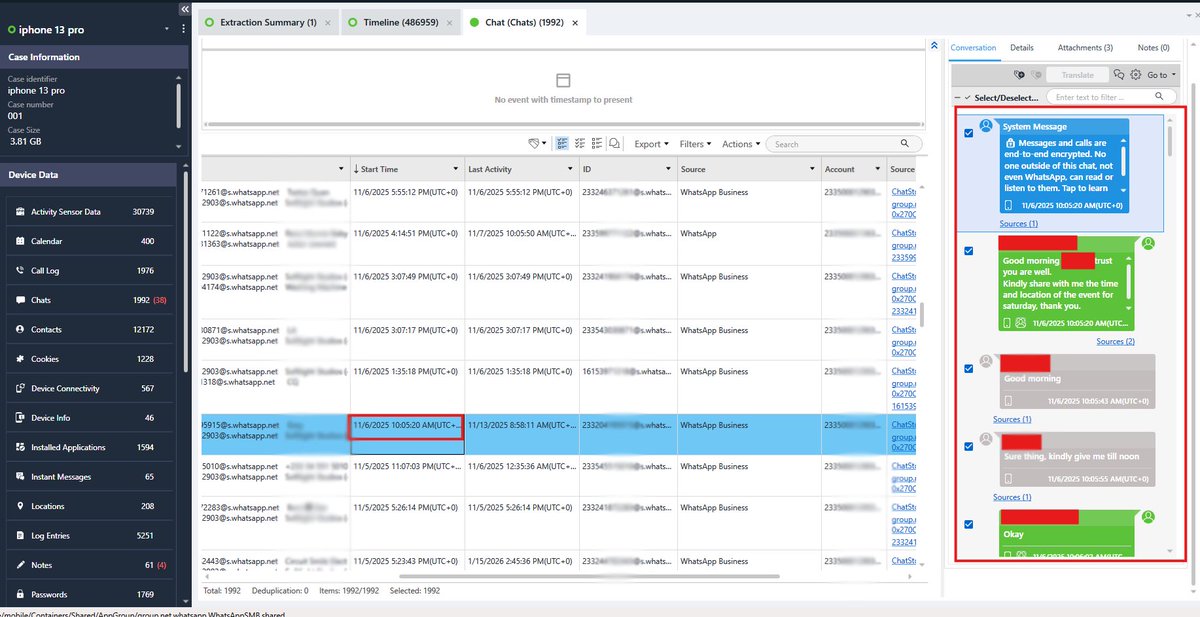
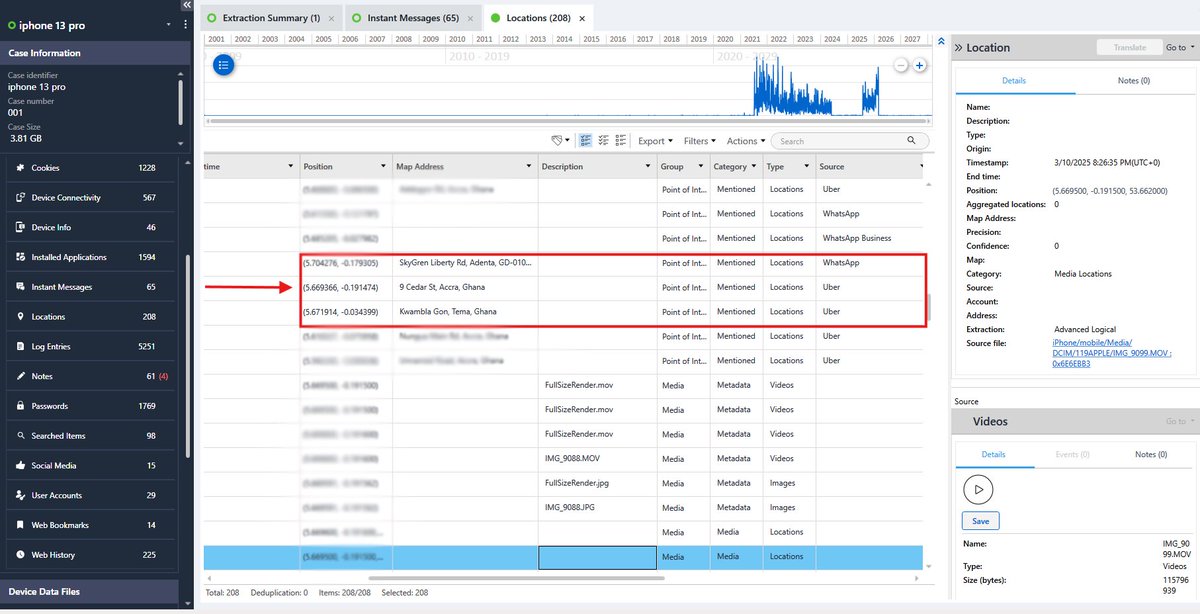
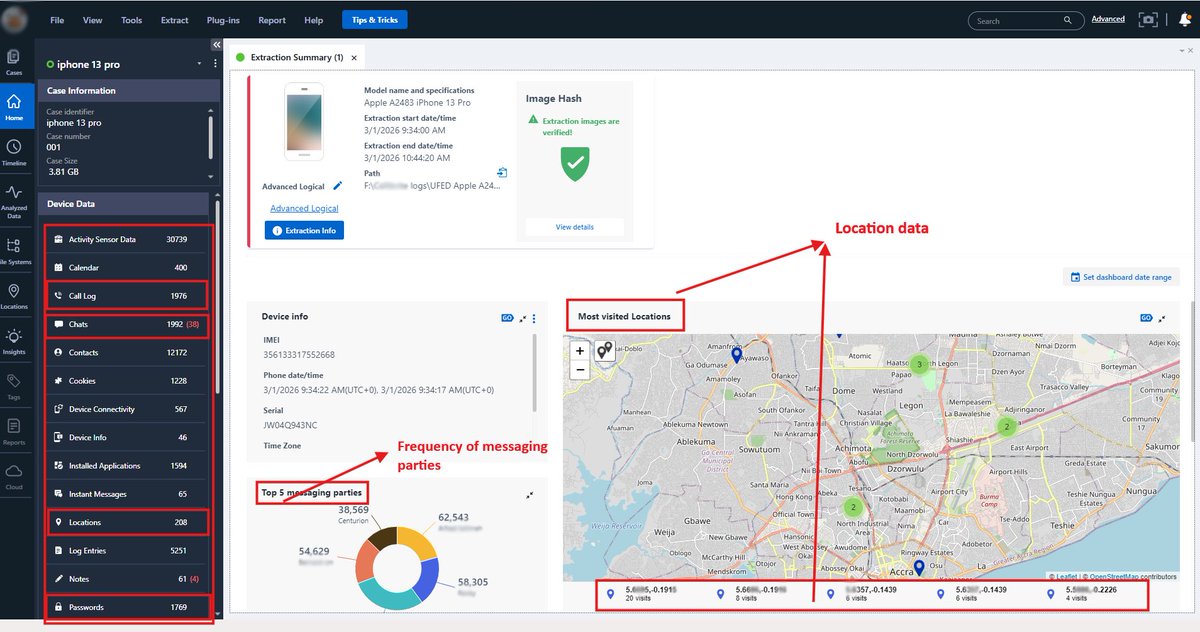
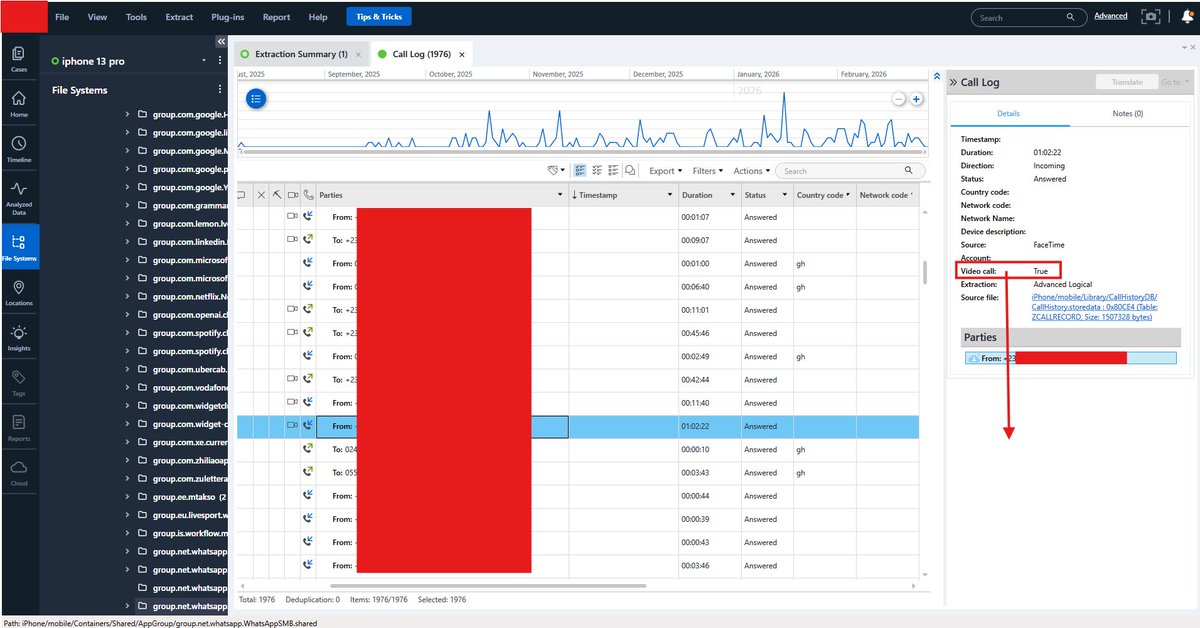
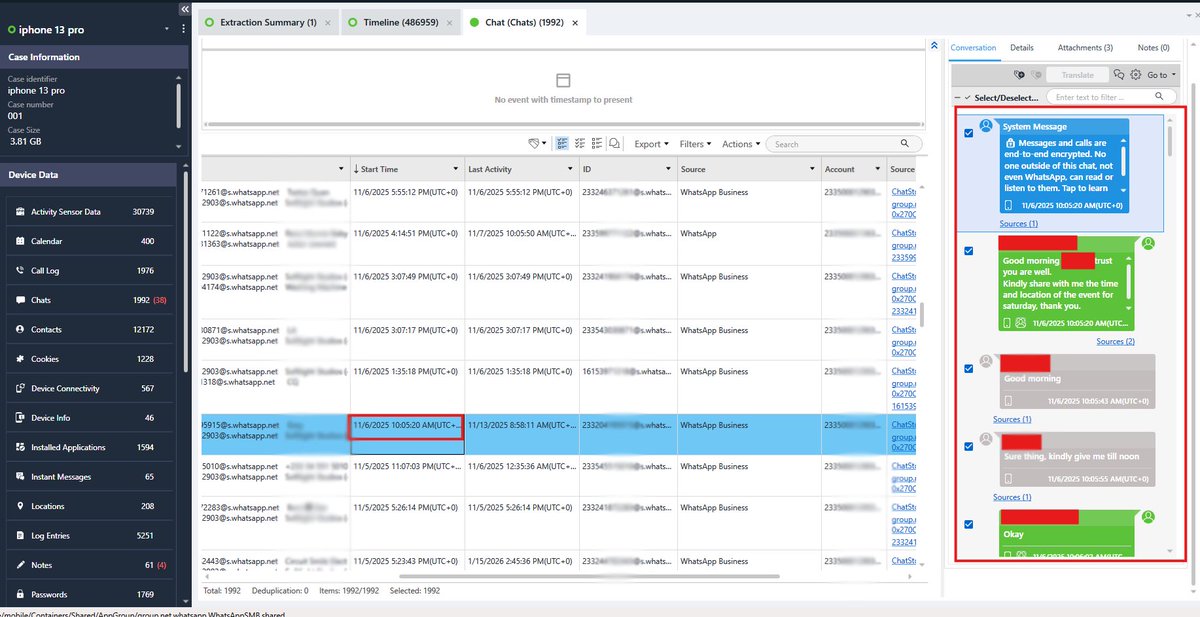
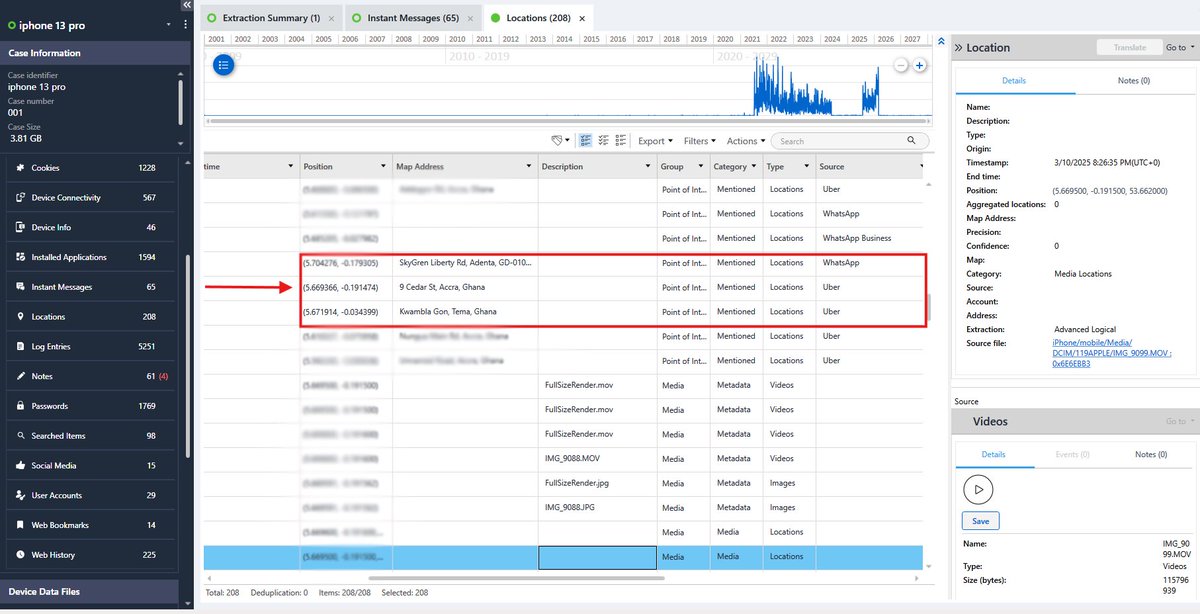
Think deleting an app wipes it off your phone? Think again. Mobile forensics can still recover traces like - when the app was installed - when it was first used - when it was removed Database journaling, system artifacts and data carving often leave behind fragments the OS doesn’t fully clean up. Delete doesn’t equal disappear.


Using the same password for multiple accounts has its own advantage and disadvantage. The advantage there is that, it will be easy for you to access all your account easily cuz they are all the same passwords...in that case there will be nothing like, I forgot my password. But the disadvantage there is like this, if one of the account you have the password in, gets breached then all your other accounts are automatically gone and you just wrote yourself a death wish letter. But here is the Catch, if you account is full of alphanumeric and special symbols...in other words, it's not even a word ...I can say it's save to use for all..but also beware of the disadvantage. Example of an alphanumeric strong password: 9e|°£tyW&$π let's see what @h4ruk7 have to say to this one



















Exclusive: Legendary director David Lynch left behind a massive estate to his four children and substantial gifts for his close friends. tmz.me/ahrmuOG
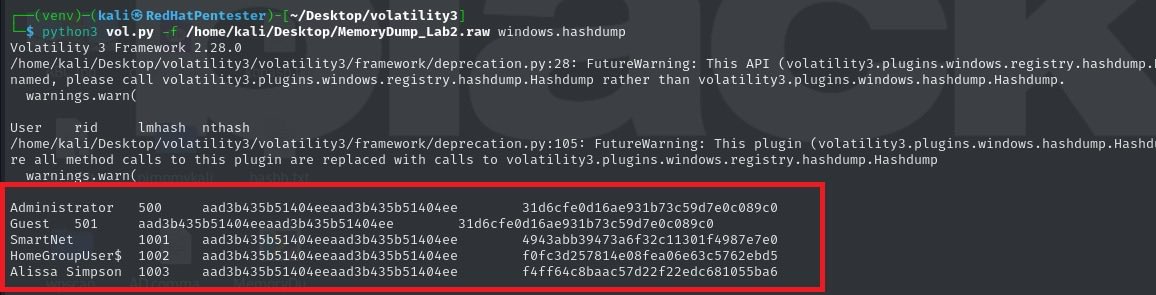
A high-profile environmental activist lost access to his system. His company needed critical data recovered, browser files, password manager credentials… everything. No disk access. Just memory. I loaded the memory dump into Volatility 3. Chrome and KeePass immediately stood out among active processes. From there, I carved out browser artifacts directly from memory and began recovering traces of stored data. Here’s what people underestimate. Even when files aren’t saved to disk, user activity still lives in RAM. Memory forensics isn’t just a backup plan. Sometimes, it’s the only place the truth still exists.
