︎
27.8K posts

︎
@0xocdsec
︎ 🏴☠️ 🇪🇺 💚 🇺🇦 | computers | 💚 🏴☠️ party | 603,628 km² ︎︎| ︎ https://t.co/F5dgX7Bcej
Katılım Temmuz 2010
7.5K Takip Edilen4.3K Takipçiler
Sabitlenmiş Tweet
︎ retweetledi

❗️The leaked sample data from China's National Supercomputing Center in Tianjin includes a video of what seems to be a simulation of a bunker buster bomb, designed to penetrate bunkers and damage underground structures.
International Cyber Digest@IntCyberDigest
‼️🇨🇳 Massive breach: Confidential data from China's National Supercomputing Center in Tianjin has been put up for sale. We've looked at the samples — the data includes aerospace engineering, military technology, bioinformatics, and nuclear fusion simulations.
English
︎ retweetledi
︎ retweetledi

Critical RCE in SGLang AI Framework
Pickle deserialization exploit, no auth, CVSS 9.8
SGLang unresponsive to patches - isolate networks now
fortbridge.co.uk/research/sglan…
#CyberSecurity #AI #RCE
English
︎ retweetledi
︎ retweetledi
︎ retweetledi
︎ retweetledi

i found chain halting bug on a network carrying $120M in stablecoins and $1.85B in market value. anyway, good morning! @HackenProof #HackenProof

English
︎ retweetledi
︎ retweetledi

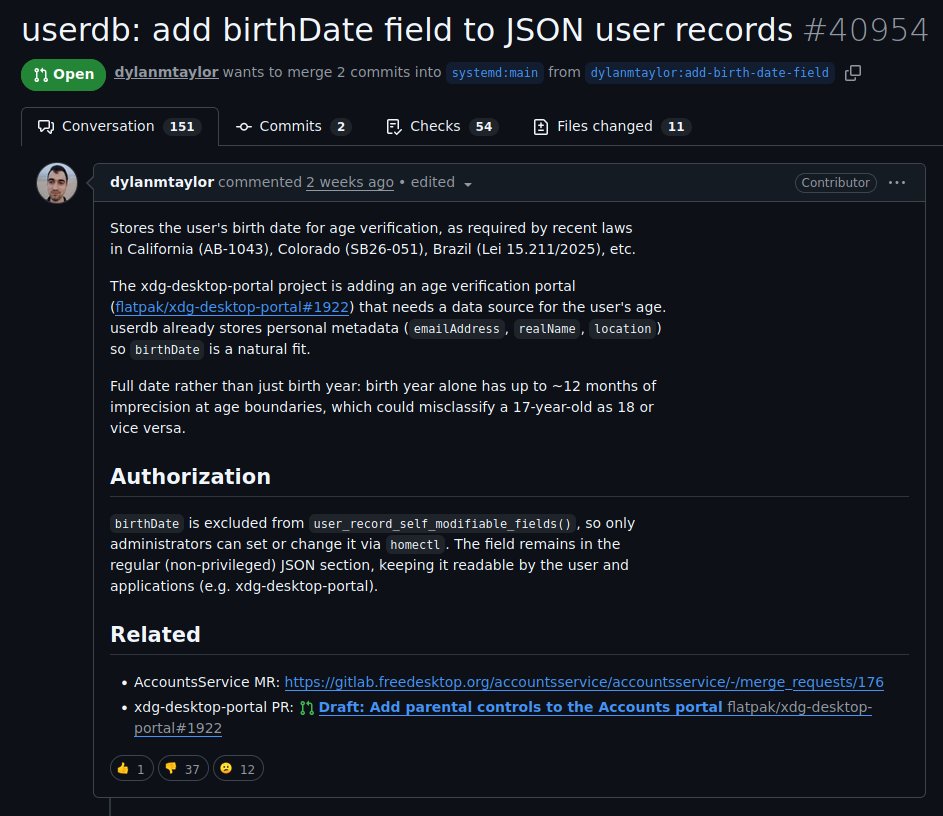
Found yet another high severity systemd bug in Ubuntu: local root privilege escalation (CVE-2026-3888) cybersecurity88.com/news/ubuntu-cv… Let us wish all Devuan users a wonderful day out with their family for a merry father's day, instead of showeling unicorn shit.

English
︎ retweetledi

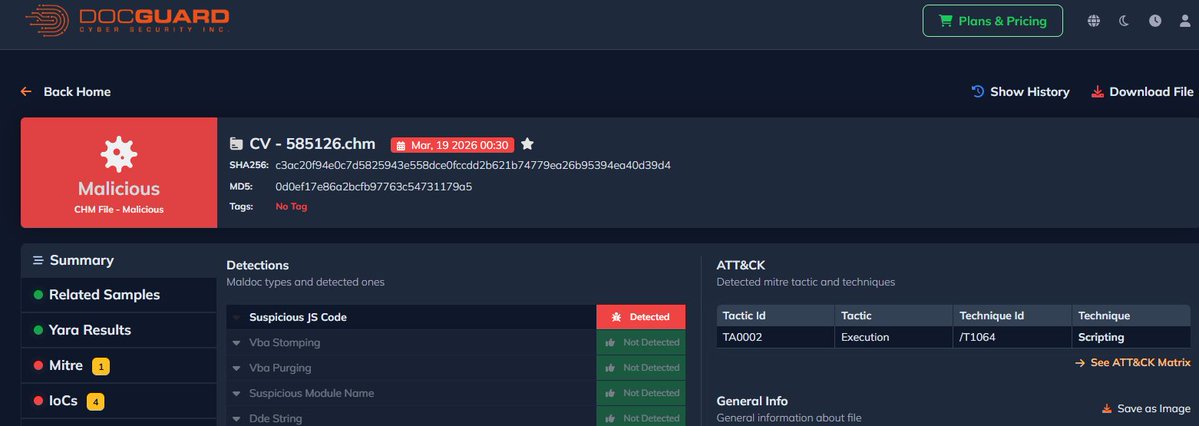
🚨#Malicious #CHM File Evaded All AV Solutions🚨
📌VT Detections 0/64
📁Filename: CV - 585126.chm
🔐MD5: 0d0ef17e86a2bcfb97763c54731179a5
DOCGuard Report: app.docguard.io/c3ac20f94e0c7d…

English
︎ retweetledi

Session Desktop (@session_app) has a critical Electron misconfiguration that turns any XSS or code injection bug into remote account compromise.
A single vulnerability in message/content handling = complete account takeover.
rmoskovy.github.io/posts/session-…
#Session #cybersecurity #threatintel
English
︎ retweetledi

(EXCLUSIVE) New investigation: Who runs Cl0p ransomware?
Months of reporting, cross-referencing forum records, dossiers, and confidential sources identifies the group's operators, developers, access brokers, and infrastructure.
rmoskovy.github.io/posts/who-runs…
#Ransomware #Cl0p #ThreatIntel #osint #clop #security #research
English
︎ retweetledi

Reversing a Vulnerable Driver: Discovering a Process Termination Primitive
New Medium post, in this one see the reversing process of a vulnerable Windows kernel driver to understand how it can be abused to terminate arbitrary processes from kernel
@s12deff/reversing-a-vulnerable-driver-discovering-a-process-termination-primitive-34aea14b9563" target="_blank" rel="nofollow noopener">medium.com/@s12deff/rever…
English
︎ retweetledi

Ubiquiti warns of a critical 10.0 CVSS Path Traversal flaw (CVE-2026-22557) in UniFi Network Applications allowing total system takeover. Patch immediately.
#Ubiquiti #UniFi #CVE #CyberSecurity #NetworkSecurity #InfoSec #Vulnerability #PathTraversal
securityonline.info/total-takeover…

English
︎ retweetledi

︎ retweetledi