azox 리트윗함

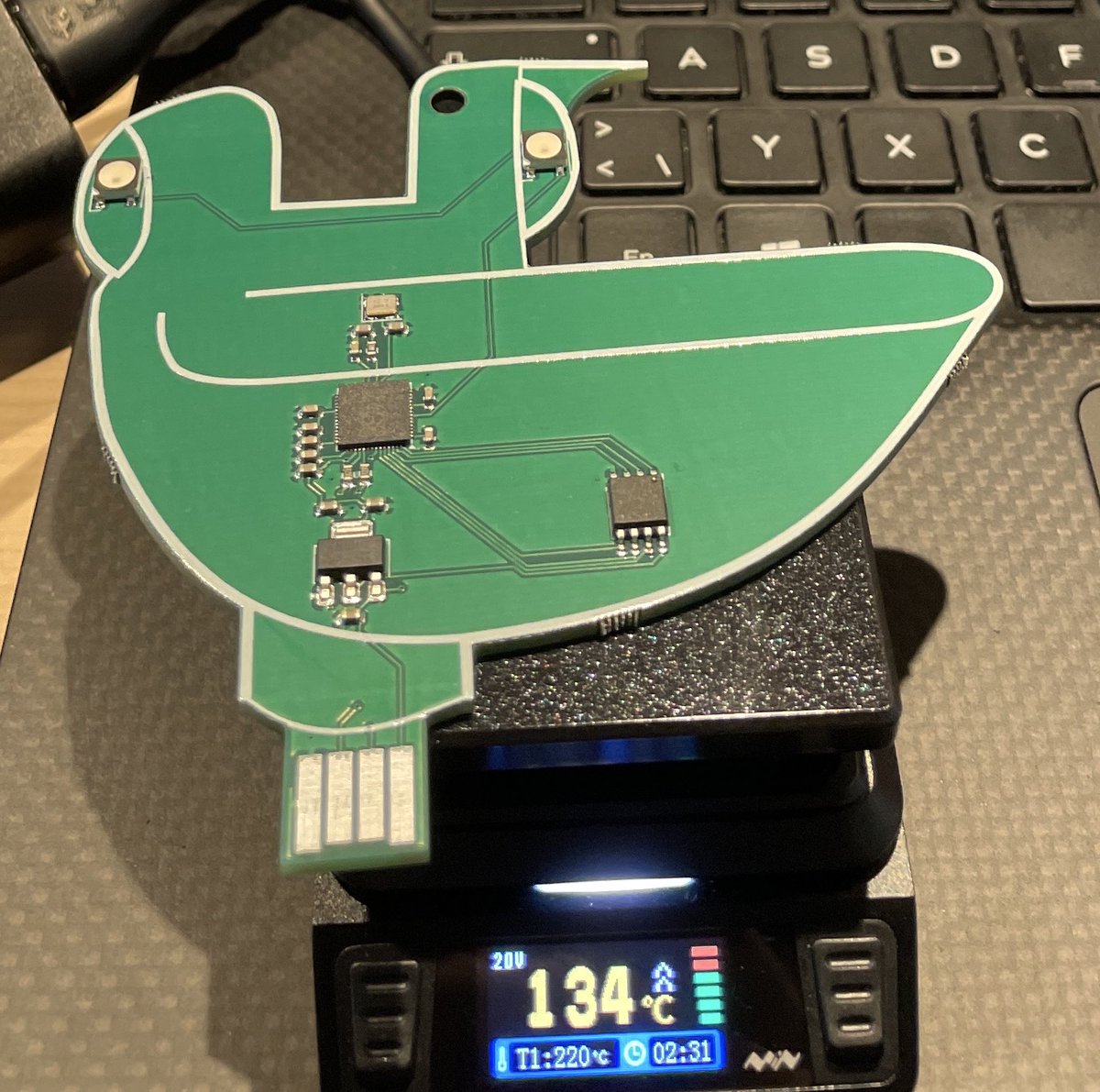
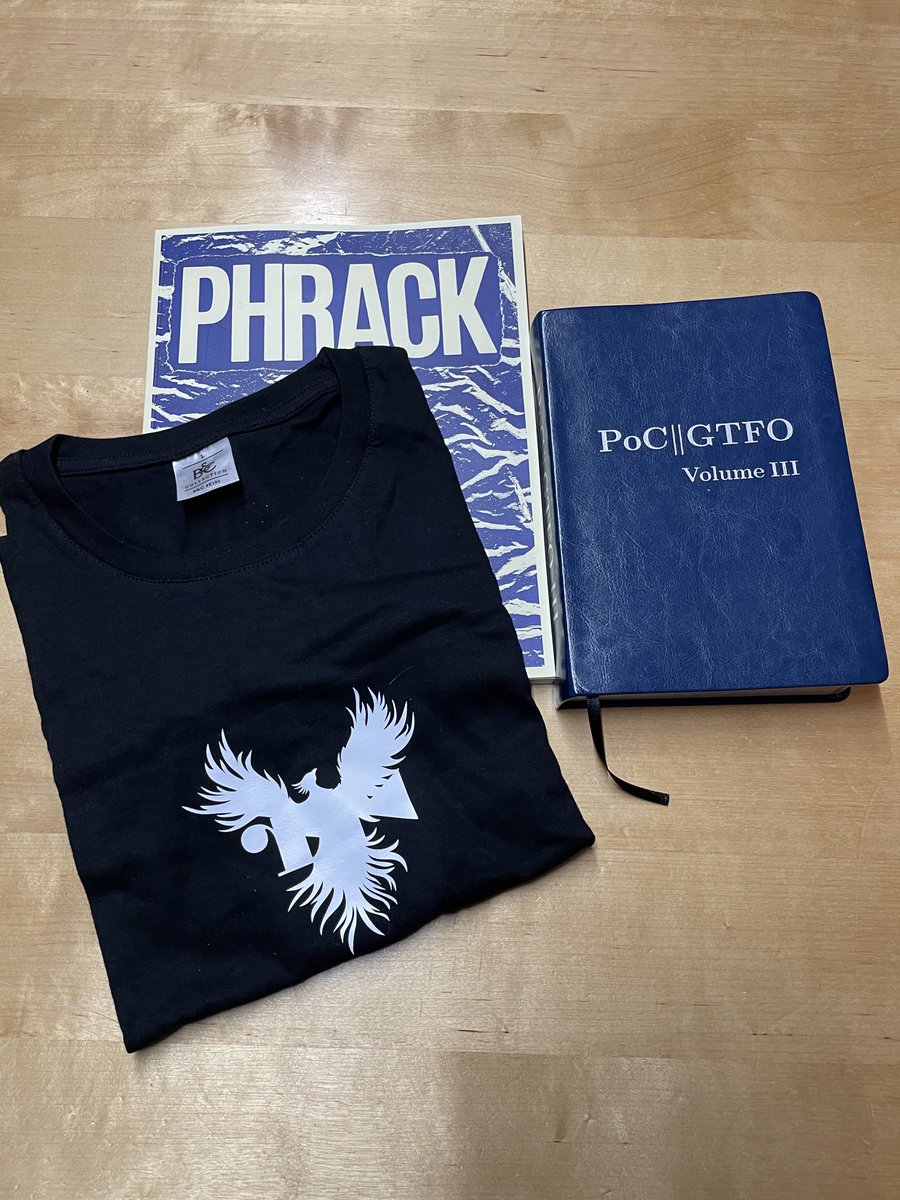
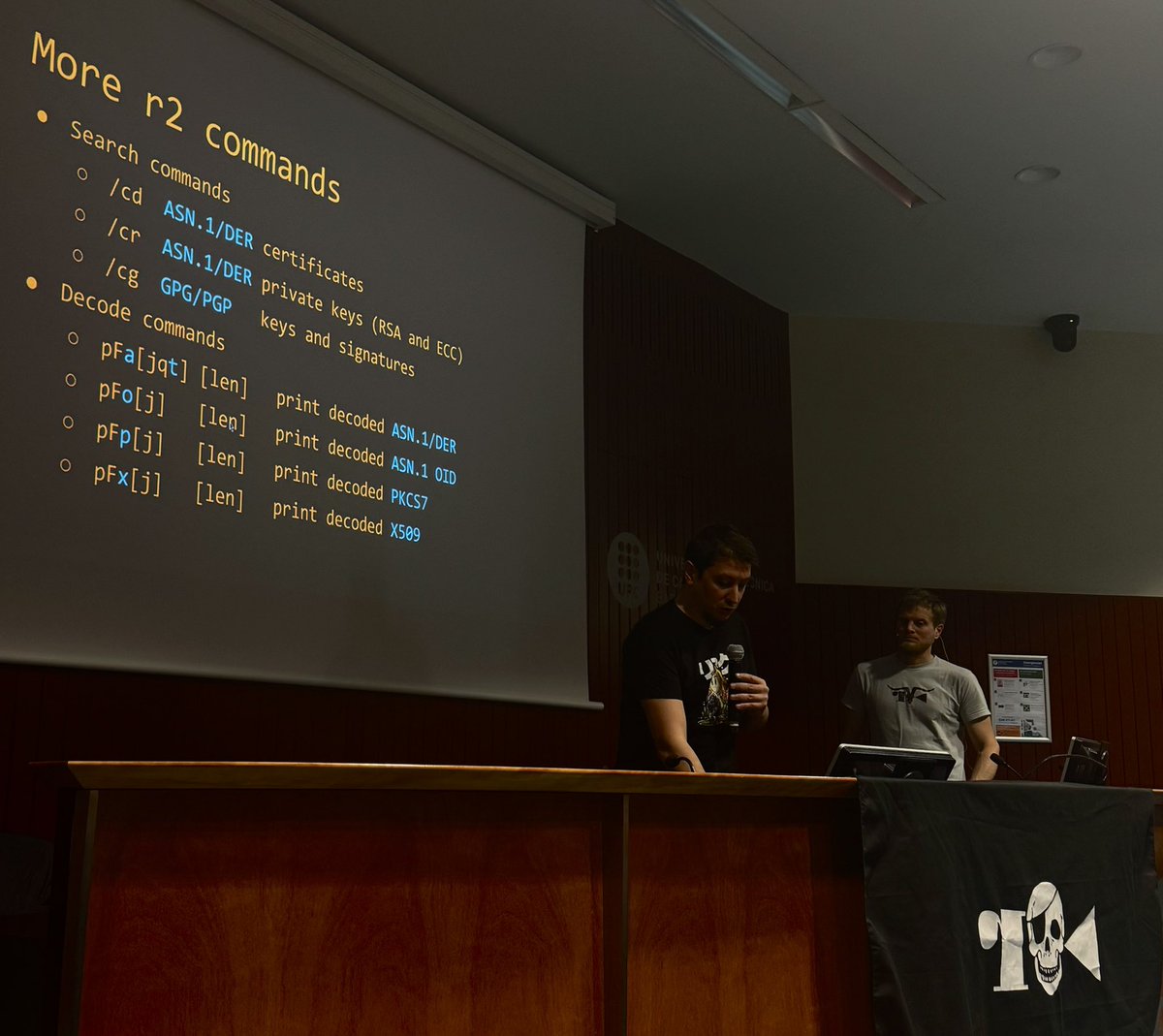
Prizes for Ph0wn CTF, sponsored by @hardwear_io
Huge thanks for supporting us each year, since 2017!
We also have another prize sponsor, but for secrecy, we can't reveal their name and prize before the CTF ;-)
Register on ph0wn.org - we're waiting for you!

English