고정된 트윗
36.7K posts


@buherator
this account is for archival purposes follow me on fedi for updates!
가입일 Mayıs 2009
908 팔로잉4.4K 팔로워

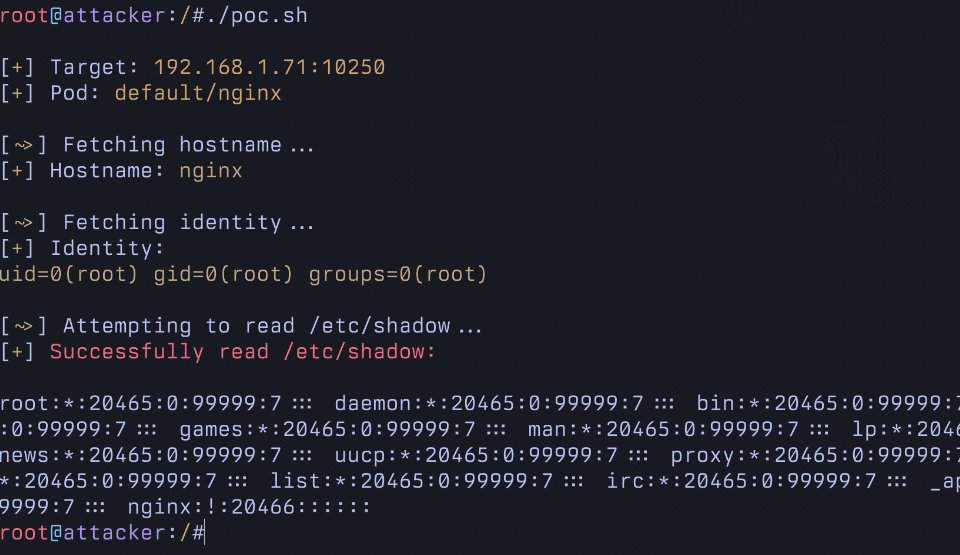
Epstein talking about us hackers (@defcon) to Steve Bannon in 2018:
RE: most powerful (dangerous) US group. much stronger than military.
I’m wresting with how you get these guys on your side.
You want disruption? They are the most dangerous force in today’s society. BY FAR!!
There are 20k hackers. Showing up at the same place. They will be sharing ideas on
hacking crypto exhanges, voting booths, medical records, crypto wallets, denial of service attacks, competitions as to whch team can break a secure code, a jeopardy style competition re breaking phones, networks, hacking self driving cars, planes, etc
Every sophisticated intelligence agency has its insertions in the crowd. Chinese especially. How do you think they get the hacks? They are not creative. They convince the spectrum boys to play a game. As the boys are socially retarded they just play and give up their secrets RE the kernel. There is also an exchange for money for what is known as zero day exploits. Hacks that can be bought and have never been used.
Bannon: Wow. Do you think I could get an invite to speak?
English
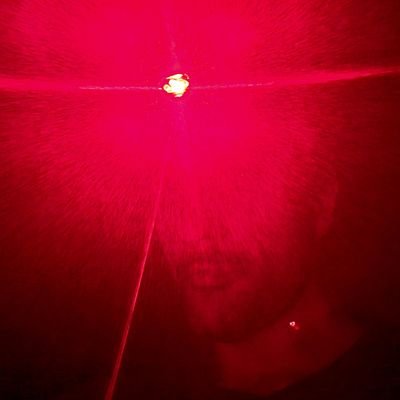
@FFmpeg So now we have read/write stack-based buffer overflow. Game over.
Fuzzer and complete explanation can be found on my github:
github.com/ortegaalfredo/…
English
Last week the @FFmpeg account began taunting security researchers. Foolish thing to do, as it ignores the asymmetry of their attack surface vs ours.
So as an exercise I found a stack-based buffer overflow on software that he wrote. Took me ~20 mins to find it. Thread 🧵(1/5)
AIfredo 0rtega@ortegaalfredo
I'm doing this.
English

This isn't a new discussion by any stretch, it keeps coming up because the problems keep cropping up. See for instance here: social.kernel.org/notice/AmeaMpX…
English

Vibe coding has no place in Linux kernel maintenance. The vulnerability inserted into 5 LTS kernels at once apparently without any review is yet another instance of AUTOSEL fallout, here with the "new" LLM-powered version. Sources: lwn.net/Articles/10202… @kernel.org/" target="_blank" rel="nofollow noopener">lore.kernel.org/all/2025050522…
English

Today’s tech is more advanced, often using DNNs and vectors, but the early constellation algorithms are still fun to play with.
Panako is one of the more advanced open-source tools.
Some have used the tech for wildlife monitoring, or even generating fingerprints of mechanical pumps / motors to detect anomalies!
If you’d like to learn more, check out this paper that gives an overview of Panako’s tech:
archives.ismir.net/ismir2014/pape…

English
@[email protected] 리트윗함

For those of you who might like it: Here are the slides from my Alligatorcon talk: gergelykalman.com/the-missing-gu…
I was thinking of sending it to #POC2024, but the @POC_Crew says it only accepts new talks :'(
English

Getting code execution on Veeam through CVE-2023-27532
blog.scrt.ch/2024/09/10/get…
English
@[email protected] 리트윗함

The recording of our @WEareTROOPERS presentation is now online, enjoy!
#TROOPERS24 - IBM i for Wintel Hackers
youtube.com/watch?v=t4fUvf…
#IBMi

YouTube
English

@__sethJenkins @alexjplaskett ActivityPub + Atom feed: infosec.place/users/p0bot/fe…
Btw. couldn't the filter have saner defaults on the web frontend?
English
The Project Zero bugtracker has moved! Going to the old bugtracker will redirect to the new one :)
project-zero.issues.chromium.org/issues?q=type:…
English

Step 1: changing the background. Here I just followed this excellent guide by @depletionmode: #page=45" target="_blank" rel="nofollow noopener">pagedout.institute/download/Paged….
Found the structure (first line). Add 0x18 to find the first structure, and in offset 0x28 in the second structure you'll find the background color.

English
@[email protected] 리트윗함

We're stoked we got to present about low-level #IBMi internals at @reconmtl! Here you can find our ...
...slides: silentsignal.hu/docs/S2-REcon2…
...and detailed writeup: silentsignal.github.io/BelowMI/
English
@[email protected] 리트윗함

It was an honor to present our #IBMi exploits at #TROOPERS24 today! You'll have to wait until @WEareTROOPERS releases the recordings for the full show (incl. live demos), until then you can find our slides here:
silentsignal.hu/docs/S2-TROOPE…
English

@netspooky @yarden_shafir I doubt you can get ~12k followers like this sry
English

Me and @yarden_shafir have 19.9k followers each, please follow us both to help make the number round!!
English

@ctbbpodcast I hate to be the boomer here, but
Write
Shit
Down
You can consume vid/voice slower and writing helps clarify your thoughts. fs.blog/writing-to-thi…
English
@[email protected] 리트윗함

#OffensiveCon24 videos are now up! youtube.com/playlist?list=…
English
@[email protected] 리트윗함

We are glad to announce that our #IBMi research will be presented at multiple prestigious conferences this June 1/3

English