
Pat_H
211 posts

@pathtofile
Dad, researcher, and infosec psudo-specialist, posts and thoughts are my own. He/Him. @[email protected]


New XINTRA course‼️ Advanced IIS Post Exploitation, Detection & Evasion Modern APT groups are actively weaponizing ToolShell and fileless IIS tradecraft to compromise Exchange, SharePoint, ASP workloads. If your detection and response capabilities lag exposure, this course bridges the gap with: - Memory dump analysis (Windbg) - Deserialisation exploits & detections - ViewState attacks - .NET Reflection - Deobfuscation techniques Syllabus and preview videos here👇 xintra.org/courses/9-adva… @XintraOrg





Thanks to Winsider Seminars & Solutions (@yarden_shafir & @aionescu) for Sponsoring #OST2 at the Gold🥇 level! Learn more about them here: windows-internals.com






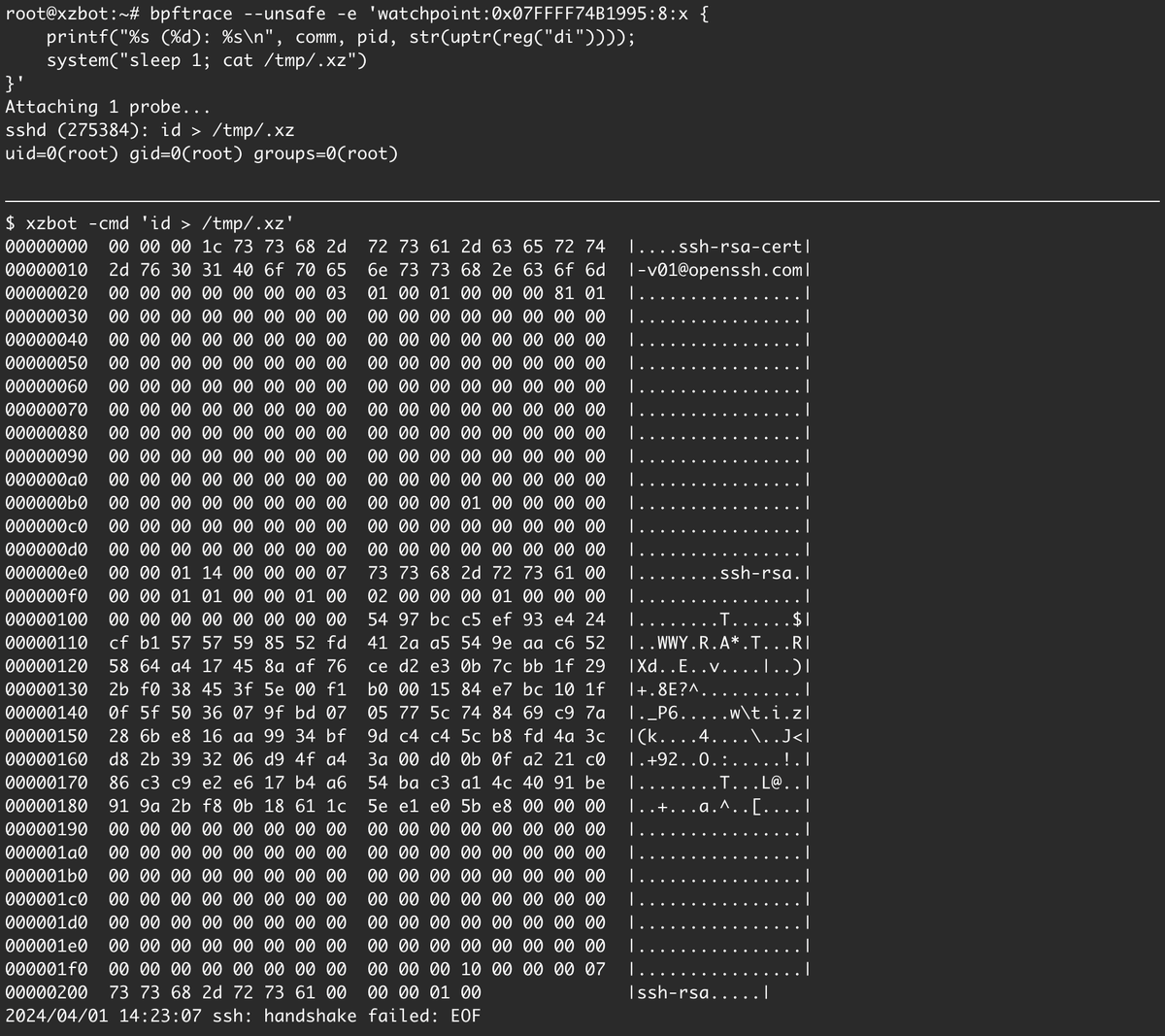
xz bd engineer 1: bro, we need a way to probe the address space to make sure we never SEGV sshd xz bd engineer 2: we'll just do a pselect syscall with empty fd sets, a timeout of 1 nanosecond and the addr we want to probe is passed as the sigmask pointer, EFAULT means unmapped