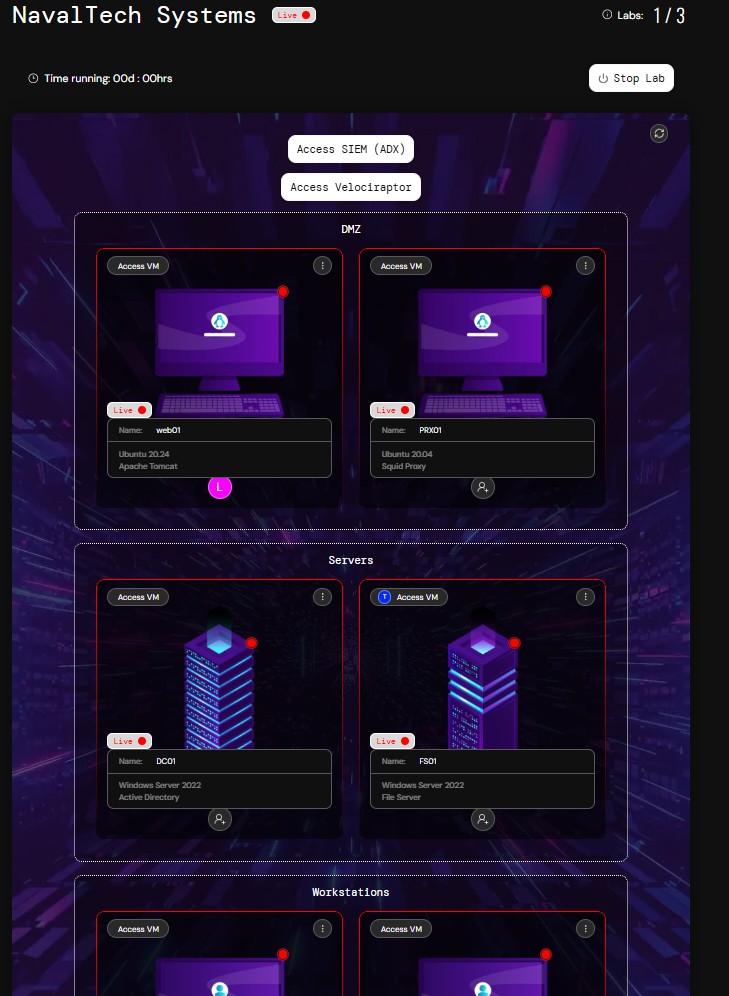
Introducing XINTRA Enterprise Live!!!! Real-world threat simulation with live infrastructure. Our team took nearly 8 months to build it, and it's finally here :) We designed it for SOC/IR teams, with the power to collect evidence, deploy your own tools, and assign tasks... along with: 🔹 Fully private infrastructure per customer 🔹 RDP into compromised systems 🔹 Sentinel + ADX integration 🔹 Deploy your own EDR/XDR 🔹 Velociraptor for forensic collection 🔹 Assign hosts to analysts 🔹 Insights hub for team performance Enquires → contact@xintra.org xintra.org/labs/enterprise You’re no longer confined to solving challenges inside a locked-down VM 😉. With full internet access across all hosts, you can download evidence, upload files, and deploy any tool directly into the environment @XintraOrg