Sabitlenmiş Tweet

Two days ago I had the pleasure of presenting our latest research at iVerify about #NSO #Pegasus BLASTPASS Exploit Chain at #BHASIA in Singapore. (#you-shall-not-pass---analysing-a-nso-ios-spyware-sample-37980" target="_blank" rel="nofollow noopener">blackhat.com/asia-24/briefi…)
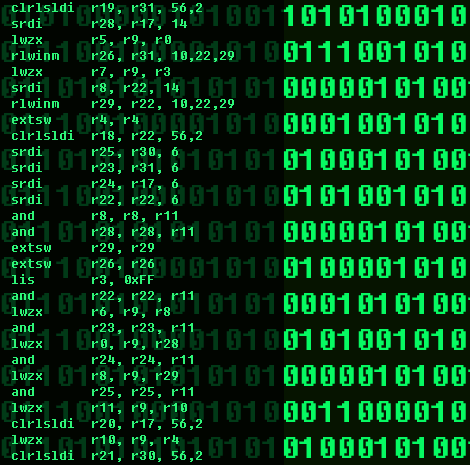
During the talk I presented how forensic analysis led to the discovery of the sample, the amount of steps
English