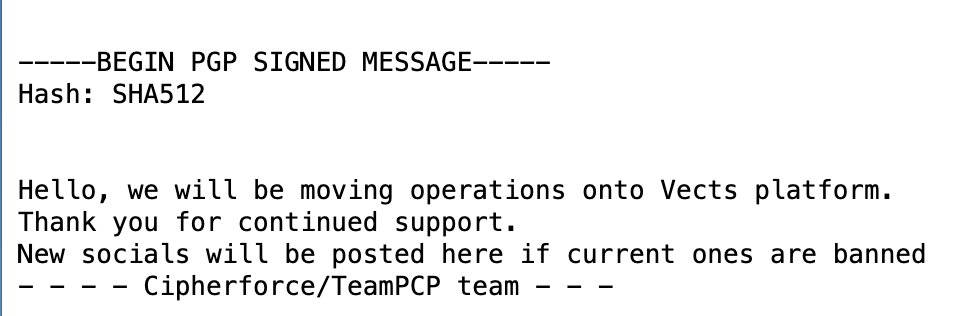
vect
48 posts







TeamPCP has done ANOTHER supply chain attack. My Brother in Christ, how many of these fuckin' things are you going to do? YOU'VE DONE 50 FUCKING SUPPLY CHAIN ATTACKS. 50 SUPPLY CHAIN ATTACKS IN EIGHT FUCKING DAYS. March 19th: - Trivy March 20th: - EmilGroup (28 packages) - OpenGov (16 packages) - Teale-io (eslint-config) - AIRTM (uuid-base32) - PypeSteam (floating-ui-dom) March 23rd: - Checkmarx March 24th: - LiteLLM March 27th: - Telnyx








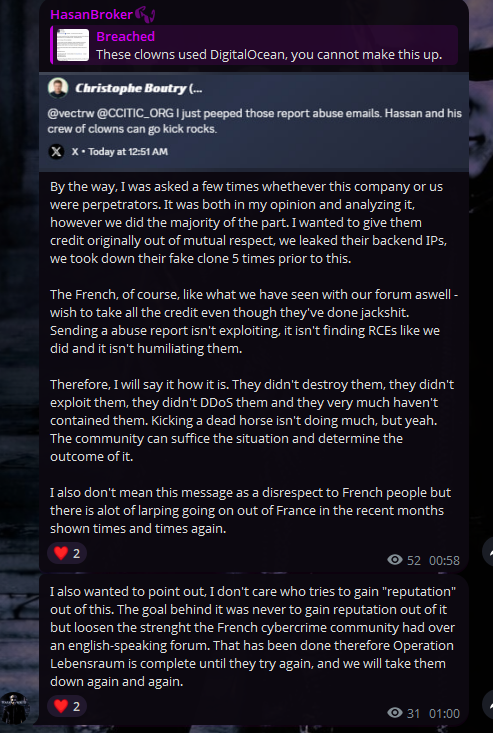
A major partnership with Breached.st is on the way, as a well deserved congratulations to Hassan for his recent victory.






.@CCITIC_ORG (Cyber Counter-Intelligence Threat Investigation Consortium) has identified the AS BreachForums servers. They have a message for the forum: "Sleep better tonight, your leaked data is on vacation." fr.linkedin.com/posts/ccitic_d…

@CCITIC_ORG took no action in this matter. All credit belongs to Hassan and his team for successfully executing the takedown and exposing the associated IP addresses. That intelligence company is attempting to exploit the situation for their own benefit.