Vhs Lady
10.6K posts









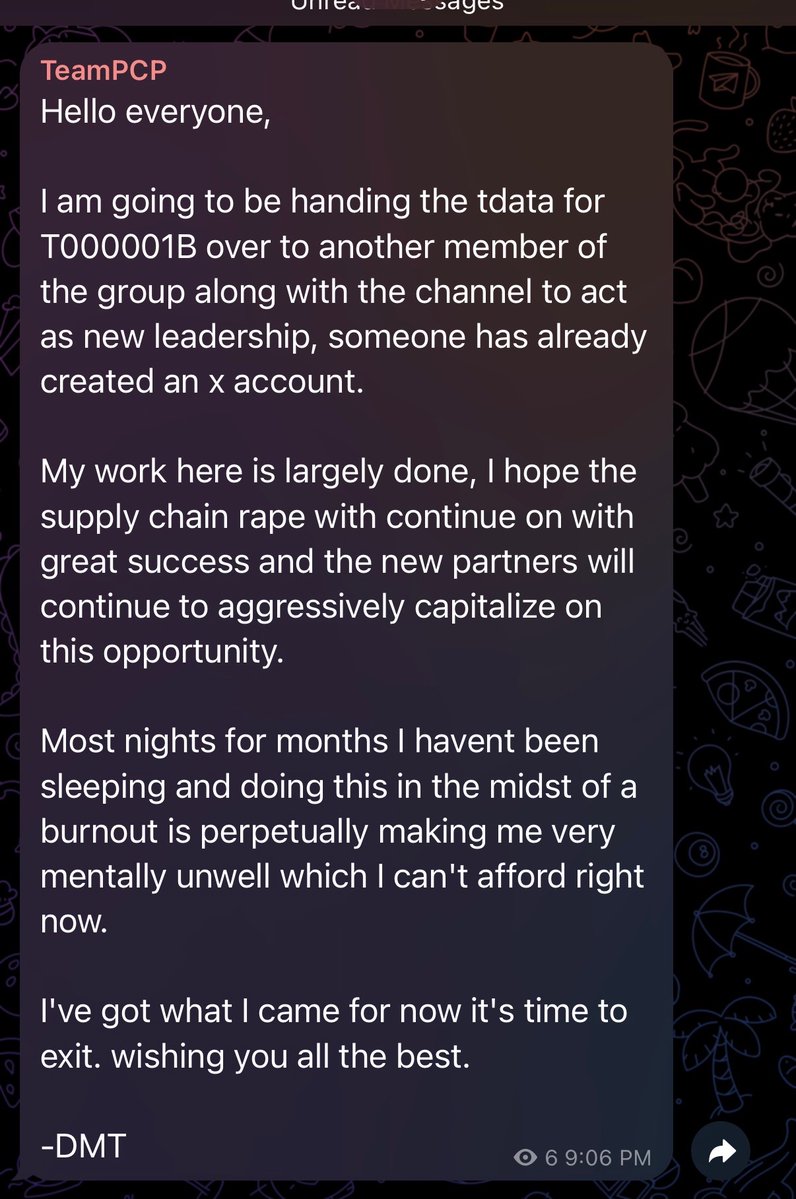
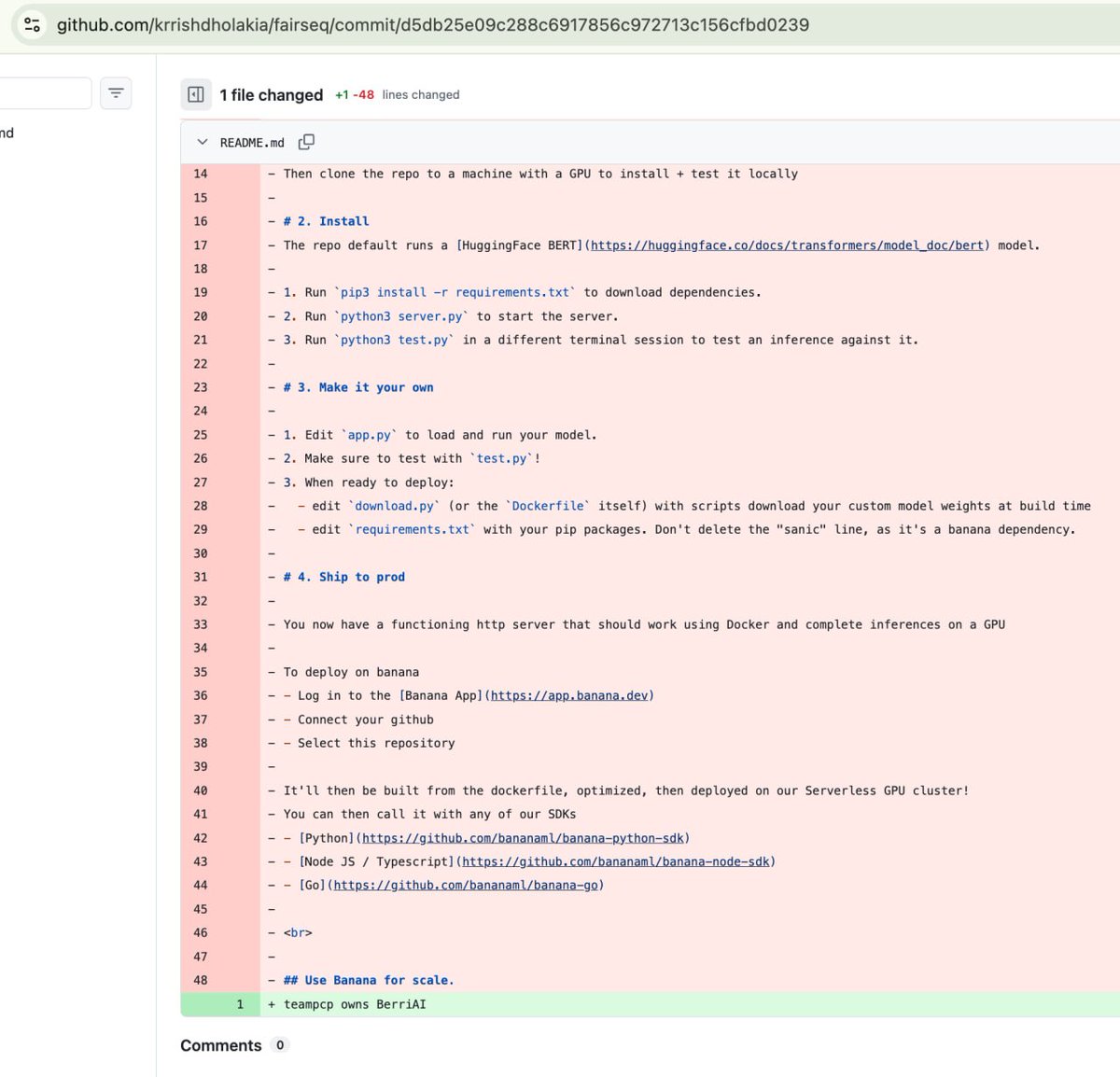
🚨 TeamPCP is systematically targeting security tools across the #OSS ecosystem, turning scanners and CI pipelines into infostealers. Attacks spreading fast across GitHub Actions, OpenVSX, and PyPI. Details → socket.dev/blog/teampcp-t…



LiteLLM HAS BEEN COMPROMISED, DO NOT UPDATE. We just discovered that LiteLLM pypi release 1.82.8. It has been compromised, it contains litellm_init.pth with base64 encoded instructions to send all the credentials it can find to remote server + self-replicate. link below












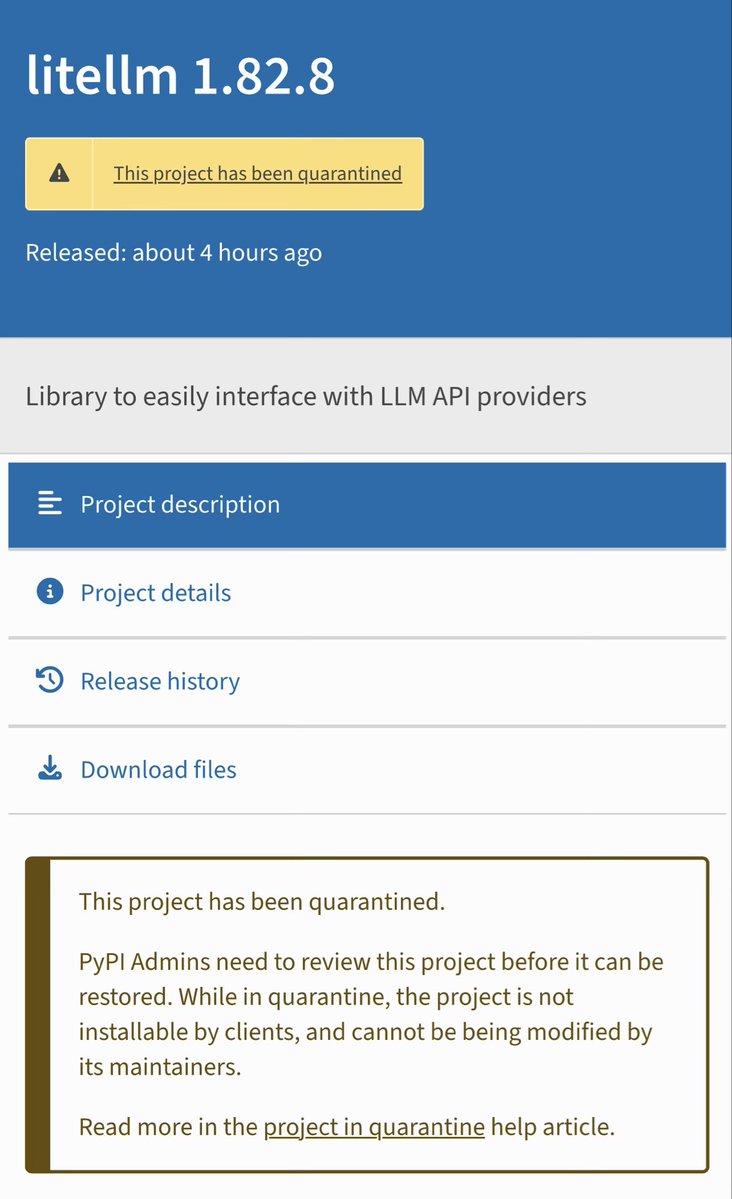
LiteLLM HAS BEEN COMPROMISED, DO NOT UPDATE. We just discovered that LiteLLM pypi release 1.82.8. It has been compromised, it contains litellm_init.pth with base64 encoded instructions to send all the credentials it can find to remote server + self-replicate. link below