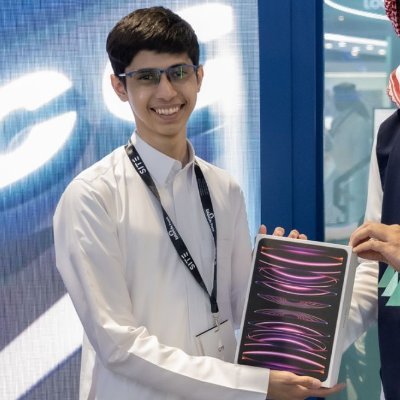
Abdullah
663 posts
Abdullah
@0x3bdullah
ㅤ ㅤㅤ ㅤㅤ ㅤㅤ
Kingdom of Saudi Arabia Katılım Temmuz 2019
666 Takip Edilen1.6K Takipçiler
Abdullah retweetledi

HTML smuggling is a sophisticated technique that embeds malicious payloads within seemingly benign HTML files, enabling attackers to bypass security measures like file filter blocks and sandboxes. Check out Part 1 of ‘Make HTML Smuggling Great Again’ here:
blog.silentstrike.io/posts/Make-HTM…
English
Abdullah retweetledi

#blackhat #blackhat_MEA
Day 1
تشرفت بلقاء أخواني @0x3bdullah و @moh2en وتنظم رائع الصراحه ولازم نشوفكم أن شاء الله بكره وبعده ♥️🙏

العربية
Abdullah retweetledi

Explore in-depth methods for bypassing EDRs, stealth persistence, and anti-forensics with undocumented APIs and memory tricks.
blog.silentstrike.io/posts/masterin…
English
الله وكيلك يقول لي الكلاينت خلصها باسبوع :)
Horizon3.ai@Horizon3ai
If you're running a pentest once or twice a year to check a compliance box, there's a lot you could be missing. Take it from @KomoriAmerica Director of IT Andy Katz: You might be leaving open pathways for attackers to enter your network for six months or more. ➡️ Learn how #NodeZero makes a difference and read the full case study with Komori America at horizon3.ai/customer-story…. #pentesting #infosec #cybersecurity
العربية
Abdullah retweetledi
Proud to share my cybersecurity training accomplishments with @offsectraining scl.io/ImcD3CX via @offsectraining

English
Abdullah retweetledi
Abdullah retweetledi
Abdullah retweetledi

الحمد لله.
بفضل من الله عزّ وجلّ،
GIAC Cloud Penetration Tester (#GCPN) ✔️
credly.com/badges/f266578…
Abdullah retweetledi

ضمن سلسلة جلسات Securetalk
يشرفنا دعوتكم للتسجيل في الجلسة الثانية
معي انا و ماجد اللاحم.
اللقاء بعنوان: A Story From Low Privilege User to Domain Admin
مع متحدثنا الرهيب:
@MHMDQi
📅 14-8-2024 الأربعاء
🕖 7-9 مساءاُ
📍مقر شركة @t2_ltd
للتسجيل: forms.gle/TZxXBHkJbyLfFg…

العربية
Abdullah retweetledi
Abdullah retweetledi
@Diefunction @offsectraining الف الف مبروك يابو حاتم 👏👏👏
امر غير مستغرب منك 🫡
العربية
Abdullah retweetledi

I’m happy to announce that I passed the @offsectraining #OSED exam 🥳. I decided to go after #OSCE3 since I already got #OSWE. Thanks to everyone who helped me on my journey.

English
Abdullah retweetledi

Released .NET tool for extracting Windows Defender exclusions & ASR rules! 🌟
🔹 Works from low user context .
🔹 Supports local & remote queries
🔹 Extracts paths from Event ID 5007 and ASR from Event ID 1121 using regex
🔹 Enumerates ASR rules from MSFT_MpPreference WMI class(works perfectly from low user context as well).
🔹 Displays results in a clean, tabulated format
works smoothly with inline-assembly!
Thanks to @VakninHai for the original trick!
github.com/0xsp-SRD/MDE_E…
English