Sabitlenmiş Tweet
Mohamad Kontar
1.3K posts

Mohamad Kontar retweetledi

Worth trying, Great job @0xMaz
SilentStrike@SilentStrikeLab
Evading EDRs requires going deeper. Our new blog breaks down advanced Rust evasion with Cobalt Strike ArtifactKit, demonstrating how to strip and rebuild PE headers to fly under the radar. Read the technical breakdown: blog.silentstrike.io/posts/Advanced… #CyberSecurity #RedTeam #EDR
English

@AzizAlsannat اكتشفت انك مبلعني ميوت، وصايا ابو تركي هذي ههههههههههه
العربية
الحمدلله، حصلت على شهادة OMSE بعد رحلة مع دراسة iOS/Android internals واستغلال ثغراتها مع تجاوز security mitigations (SPTM-TXM/RKP/PAC/kalloc_type) وتخطي RASPs و advanced obfuscations وصولًا إلى advanced forensics لأنظمة iOS/Android المُخترقة بثغرات n-days
credly.com/badges/b13ca89…
Mohamad Kontar retweetledi

The Ark that hunts the Stars ✨
I’m sharing my latest tool, Stelark. Stelark is a Compromise Assessment tool for ADCS that detects vulnerabilities and hunts suspicious certificates issued by vulnerable templates.
It also includes an intense mode for historical threat hunting that enumerates all issued certificates to uncover past ADCS abuse even after templates have been fixed.
Stelark generates an interactive HTML report and exports dump files of all identified templates and certificates for further investigation.
Check it out github.com/0xMuhannad/Ste…
GIF
English
Mohamad Kontar retweetledi

ضمن سلسلة جلسات Securetalk يشرفنا دعوتكم للتسجيل في الجلسة الخامسة اللقاء بعنوان Modern Cyber Threat Intelligence Tradecraft متحدثنا الرهيب:عبدالرحمن العمري 📅 16-07-2025 | 7 مساءَا @t2_ltd
رابط التسجيل: docs.google.com/forms/d/19pusd…
العربية

إذا غامَرتَ في شَرَفٍ مَرُومِ
فَلا تَقنَعْ بما دونَ النّجوم
Flareon11 award! Proud to add it to the collection🏅
#flareon11 #reverse_engineering


@traveler0x01 صادق مو دائما تنفع وقد واجهت اخر كم انقيجمنت صعوبة بسبب الdot1x، لكن تستحق التجربة ويعطيك العافية على إثراء المحتوى عن طريق الخبرة والتجارب🌹👍
العربية

@traveler0x01 شكرا على الافادة
اعتقد ايضا احيانا استخدامك لhost غير الwindows سواءا MacOS device او Linux كhost يسوي bypass للNAC
Mohamad Kontar retweetledi

NetExec has a new Module: Timeroast🔥
In AD environments, the DC hashes NTP responses with the computer account NT hash. That means that you can request and brute force all computer accounts in a domain from an UNAUTHENTICATED perspective!
Implemented by @Disgame_
1/3🧵

English
Mohamad Kontar retweetledi
Mohamad Kontar retweetledi

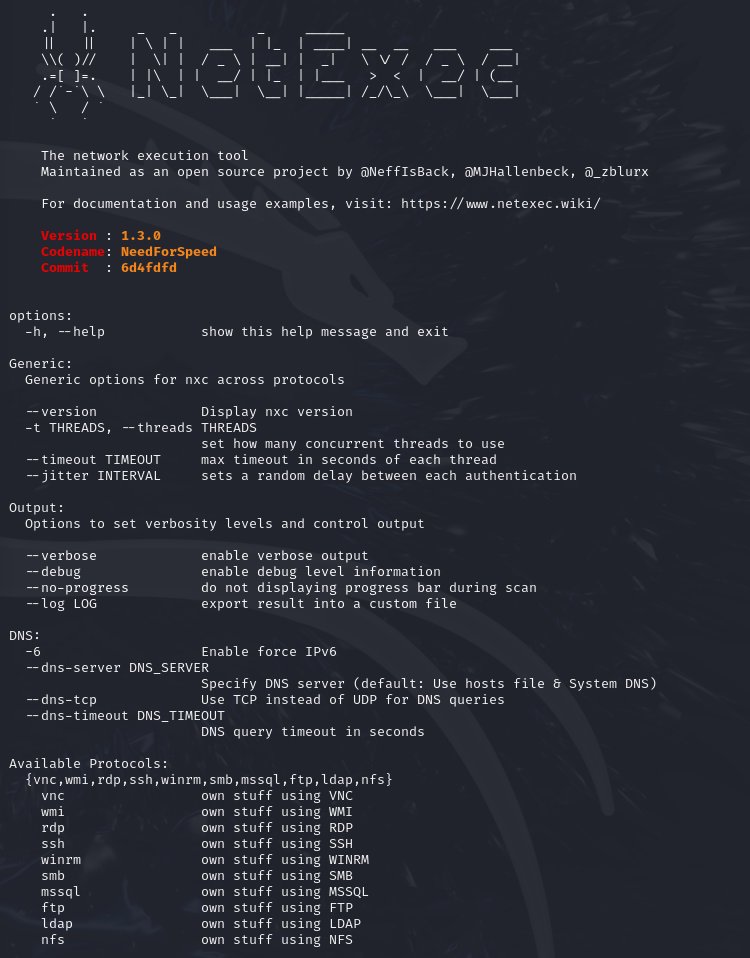
NetExec Version 1.3.0 has been released🔥
Biggest new features:
- New NFS protocol
- SCCM Enumeration
- Coercer_plus module
For the detailed release notes check out: github.com/Pennyw0rth/Net…
Or our wiki as soon as a feature rundown is available.
English
Mohamad Kontar retweetledi

@DFIRx eLearnSecurity Certified Digital Medical Professional 🔥🔥🔥♥️
Español