0x4143 retweetledi
0x4143
415 posts
0x4143
@0x4143
Purple Teaming by day, Malware Hunter by night 🏴 (All opinions are my own, not of my employer)
::1 Katılım Eylül 2012
4.9K Takip Edilen2K Takipçiler
0x4143 retweetledi

Given the recent events with VMPSoft DMCA'ing educational YouTube videos demonstrating how to unpack malware protected with VMProtect, we have decided to release a free to use unpacker which works for all versions of VMP 3.x including the most recent version.
Simply sign up/login here: app.codedefender.io and then click on "Unpacker" on the top right corner.
For context:
x.com/rhotav/status/… x.com/allthingsida/s… x.com/herrcore/statu…

English
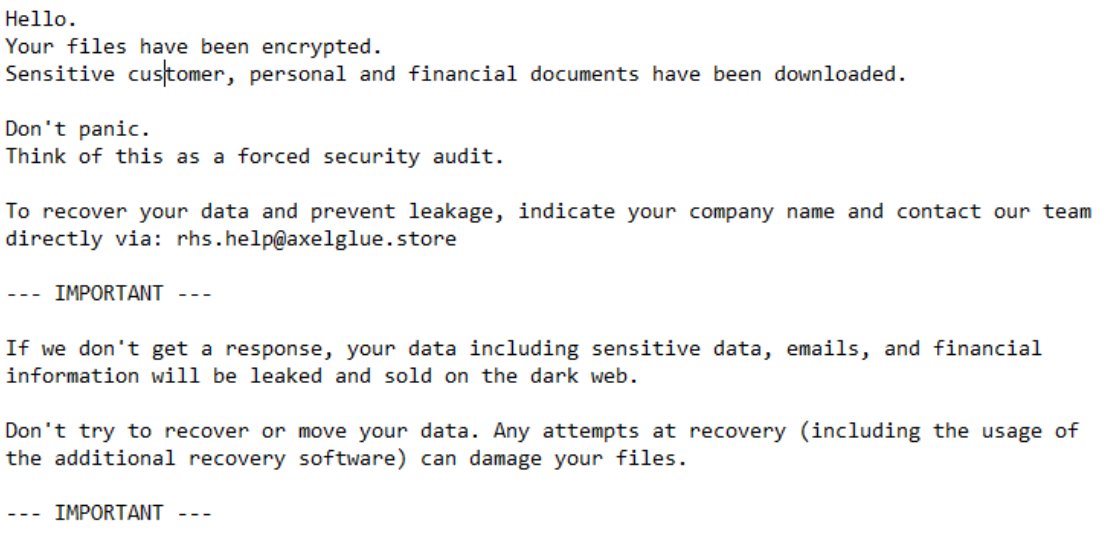
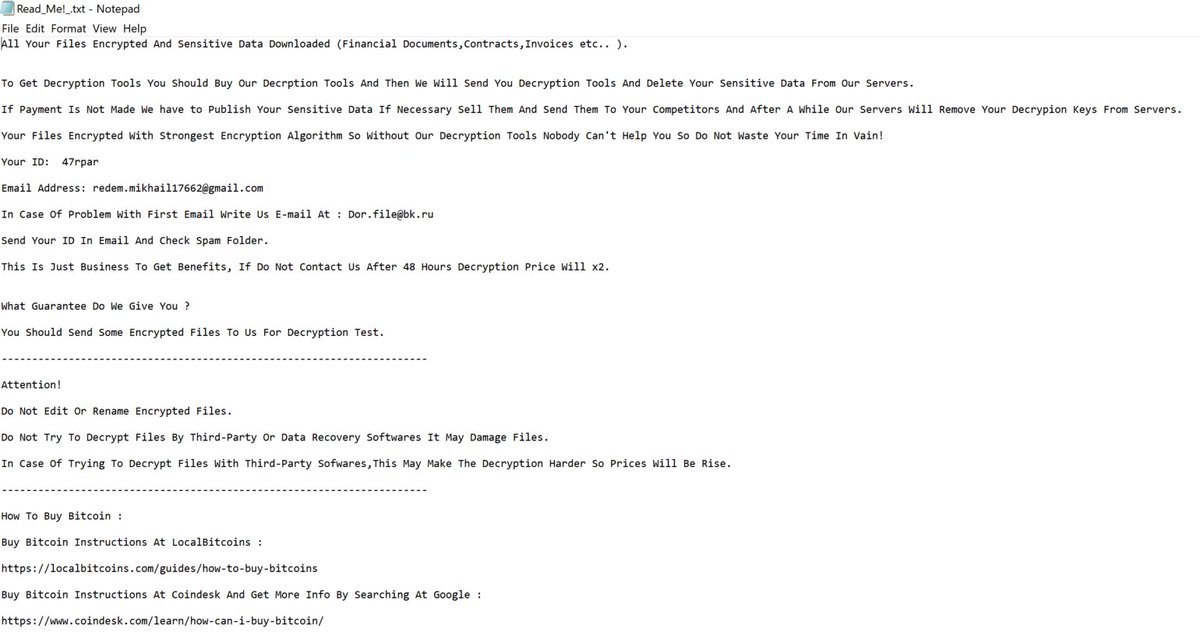
New ransomware...
MD5: c85b8d8a130e475bd294feb1be152890
SHA256: db7244e877f1801fd83dc504295ba04f362bc1b7966fc5c41a06f0fb1ddd7bd7
file.ext -[james.shaw.junior@gmail.com]id-[<10randomchars>].aaabbbccc
ransom note: howtoDecrypt.txt

English

My first blog post with @sublime_sec!
We followed an infostealer campaign that had some very weird and fun levels of obfuscation.
Sublime Security@sublime_sec
TROX Stealer is a new MaaS stealer attackers are using to exfiltrate stored credit cards, credentials, crypto wallets, and more. Our Threat Research team performed a deep analysis to see how it works, how it’s packaged for large-scale deployment, and its distribution mechanisms: sublime.security/blog/trox-stea…
English
0x4143 retweetledi

My presentation slides "UEFI Bootkit Hunting: In-Depth Search for Unique Code Behavior" @REverseConf are available online github.com/binarly-io/Res…
English
0x4143 retweetledi

The Windows Kernel Exploitation tutorial series is complete for both English and Spanish speakers. Huge thank you to @HackSysTeam for creating HEVD to begin with and thank you to @corelanc0d3r and @ret2wargames for creating resources that are free for those who can't afford them!
English
0x4143 retweetledi

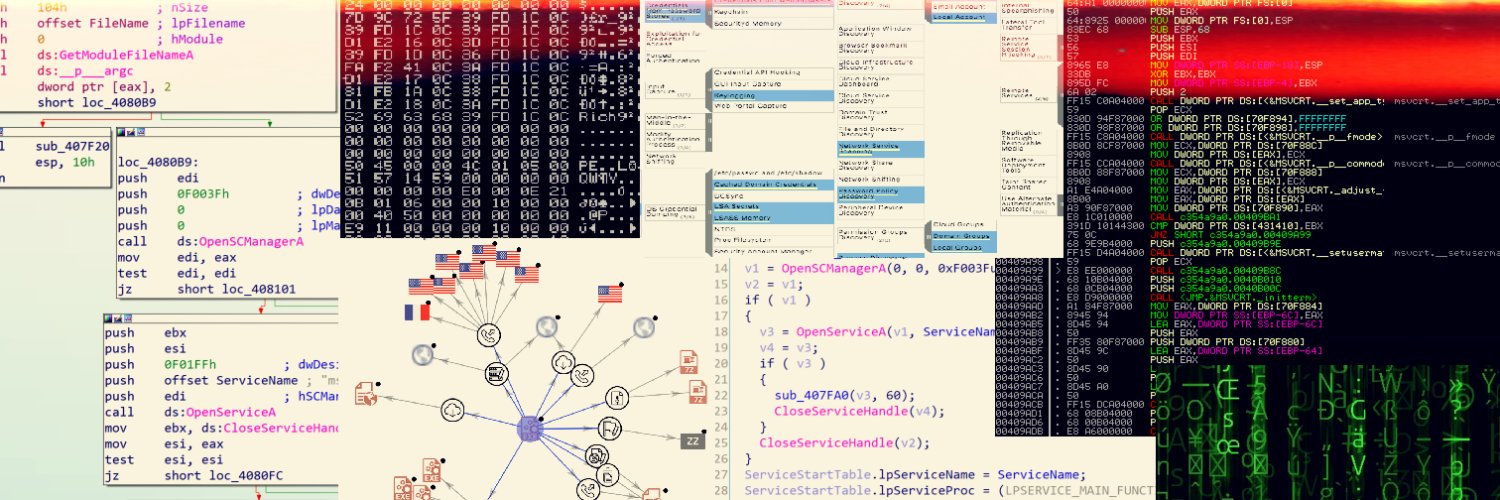
6 months ago, I started working on a way to better map the #ransomware ecosystem and its evolution, including rebrands.🔎
I am really happy to share this handmade cartography, which is based on @orangecyberdef resources, #OSINT and reverse engineering.
➡️ github.com/cert-orangecyb…

English
0x4143 retweetledi

Interesting maldoc was submitted from Belarus. It uses Word's external link to load the HTML and then uses the "ms-msdt" scheme to execute PowerShell code.
virustotal.com/gui/file/4a240…
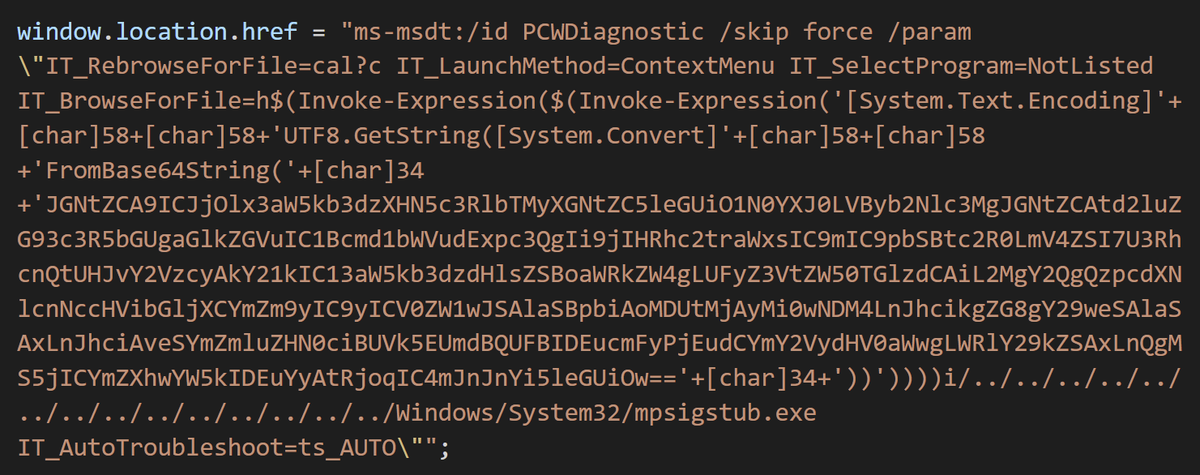
English
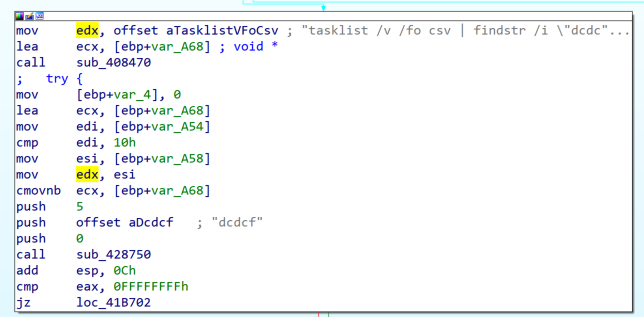
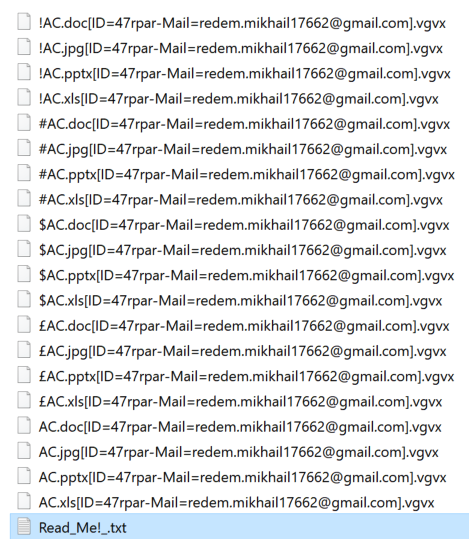
Unknown (new?) #ransomware
Encrypts files with .vgvx extension
SHA256: 81a27b3dcfbd52ceb68043465a9aaa3ff6a2e4d04e487197bb23db5c76eec740
CC: @demonslay335 @Amigo_A_
English
0x4143 retweetledi

I usually make short-form satirical videos for fun, but never share them with the world. This time tho, I thought I'd make one for the infosec community. Some might even find it educational 😅
If you're in #infosec and you feel a little down this week, this video is for you💙
English
0x4143 retweetledi

☁️ Awesome Cloud Security ⚔️
Collection of awesome #Cloud security tools, standards, and other resources
🔗 github.com/4ndersonLin/aw…
#cloudsecurity #DevOps #Pentesting #infosec #cybersecurity

English
0x4143 retweetledi
@0xAsm0d3us Thx for the mention @0xAsm0d3us ! I aim to update this again very soon! 😎
English

This awesome repository contains Malware analysis/Reverse engineering related tools, training, podcasts, blog posts, literature and just about anything else closely related to the topic. - by @0x4143
github.com/0x4143/malware…
#malware #hacking #reversing #cybersecurity

English
0x4143 retweetledi

🚨🚨WARNING 🚨🚨 We have confirmed that #Emotet is dropping CS Beacons on E5 Bots and we have observed the following as of 10:00EST/15:00UTC. The following beacon was dropped: tria.ge/211207-t5l24sb… Note the traffic to lartmana[.]com. This is an active CS Teams Server. 1/x
English
0x4143 retweetledi

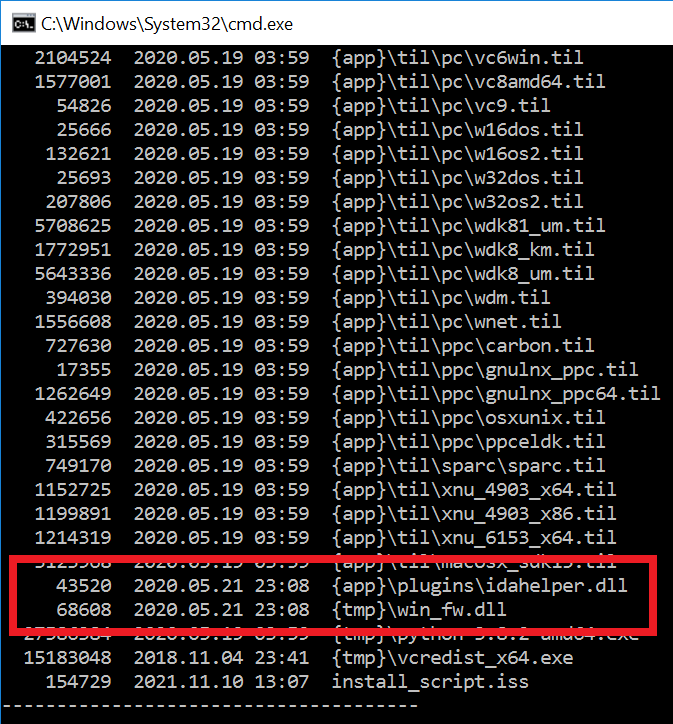
#ESETresearch discovered a trojanized IDA Pro installer, distributed by the #Lazarus APT group. Attackers bundled the original IDA Pro 7.5 software developed by @HexRaysSA with two malicious components. @cherepanov74 1/5

English
0x4143 retweetledi
0x4143 retweetledi
I found some private keys on VT, enabling all of us to decrypt C2 traffic from a subset of all the malicious Cobalt Strike servers that are out there on the Internet. More details: "Cobalt Strike: Using Known Private Keys To Decrypt Traffic – Part 1" blog.nviso.eu/2021/10/21/cob…
English
0x4143 retweetledi

I tweaked overflowedminds.net a little bit and I uploaded trainings, courses, papers, presentations, and posts with the idea in mind that knowledge should be free. Some of the most interesting content follows:
English