
Takahiro Haruyama
4.6K posts





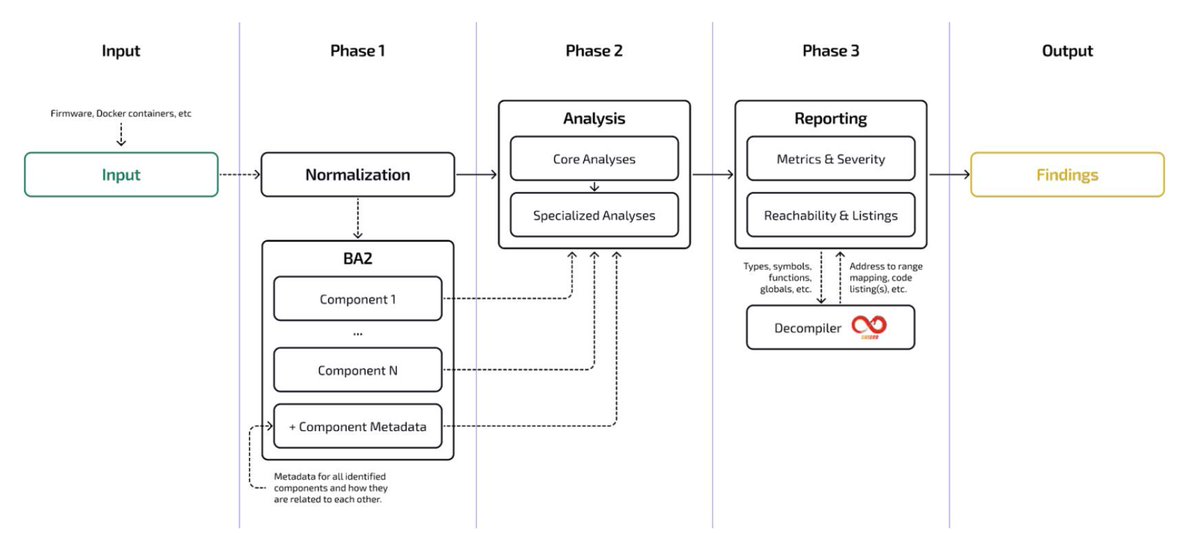
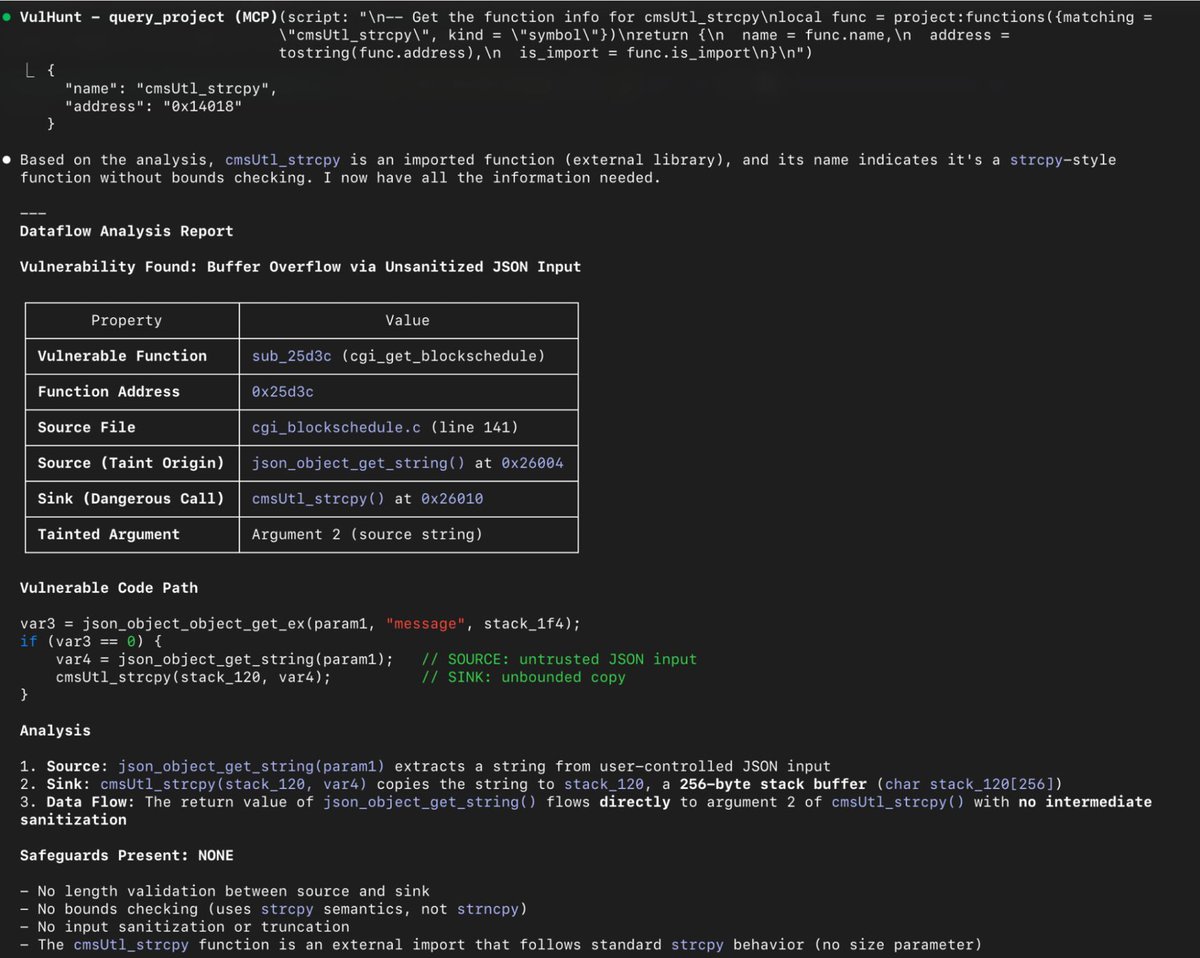

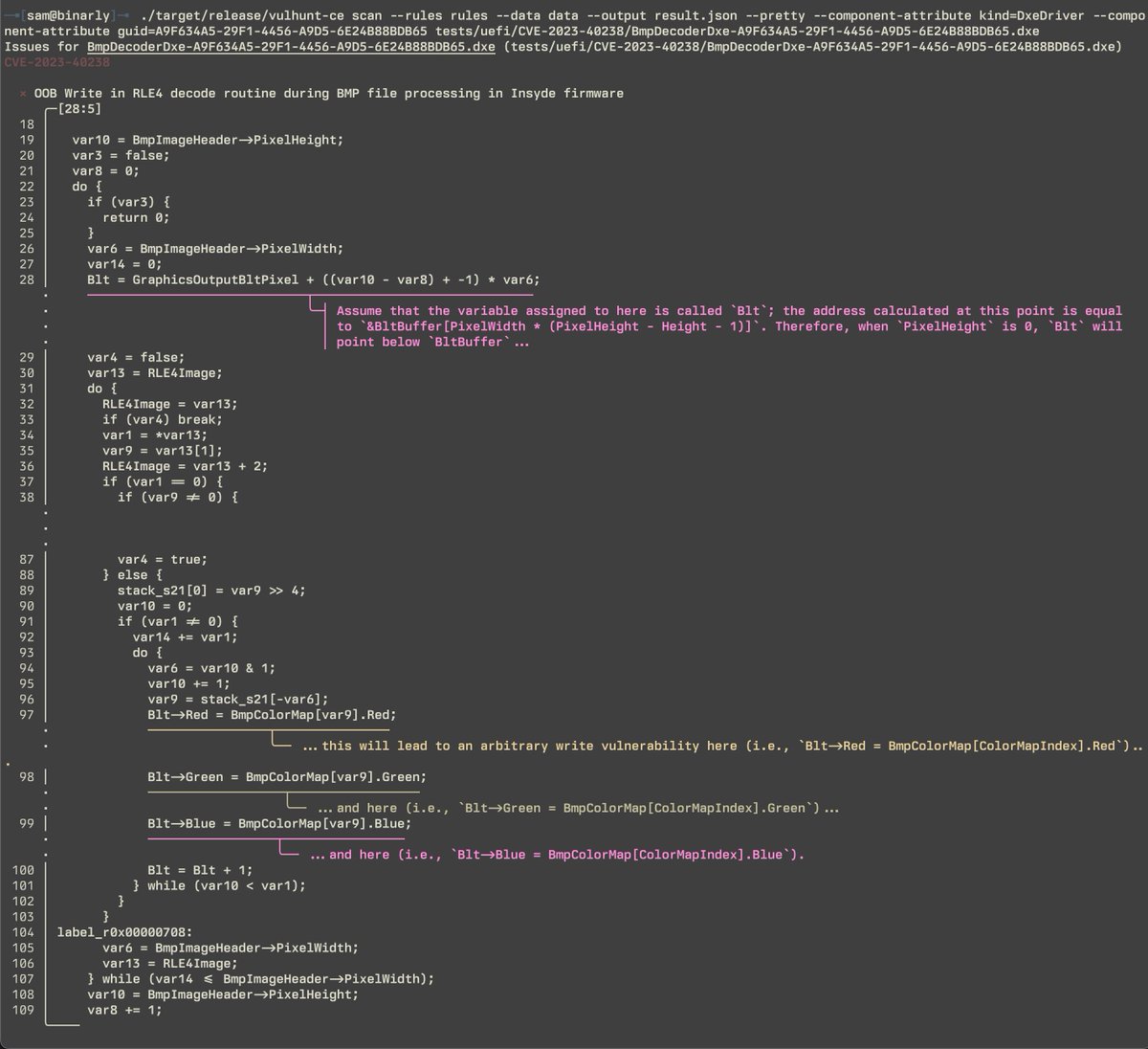


This year at @REverseConf, we’re dropping something special, a project we’ve been heads-down on for a while that boosts semantic-level binary detection with reachability + taint analysis. Like CodeQL/Semgrep, but for binaries. VulHunt use cases: Vuln REsearch: binarly.io/blog/vulnerabi… Detection Eng: binarly.io/blog/vulhunt-i… VH Intro: binarly.io/blog/vulhunt-i…







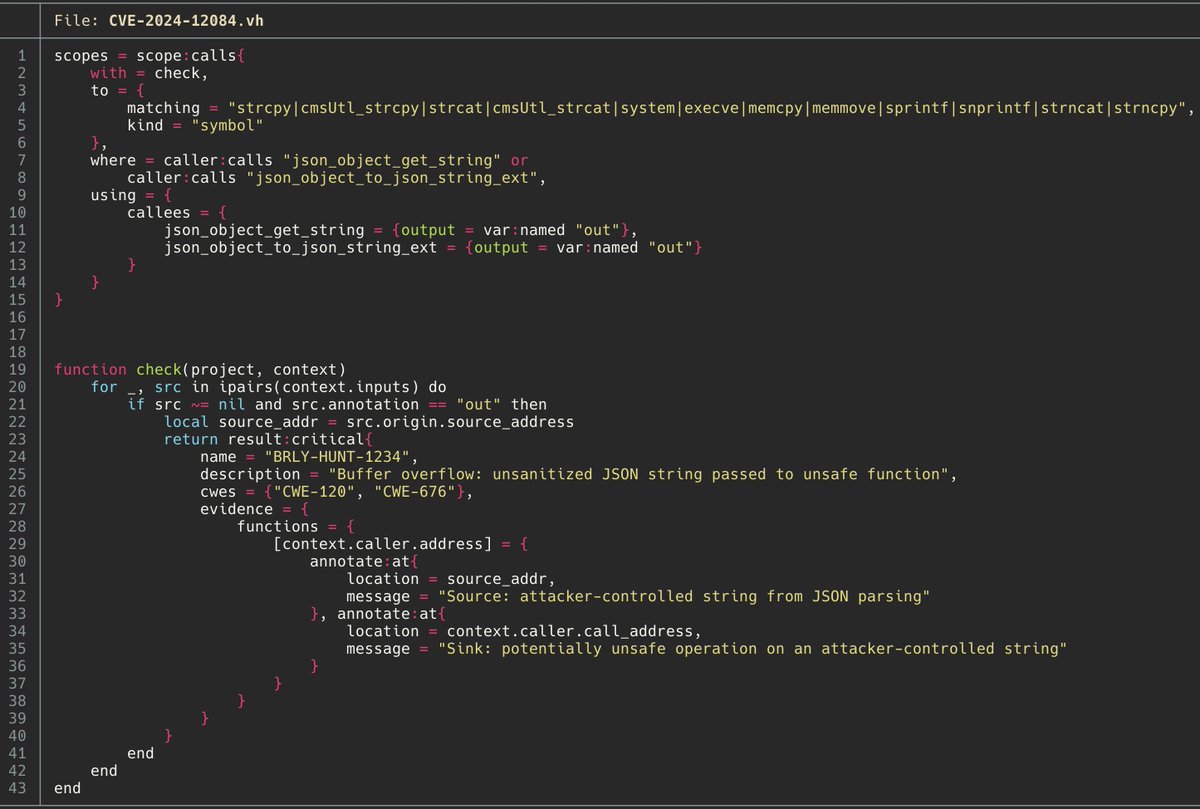
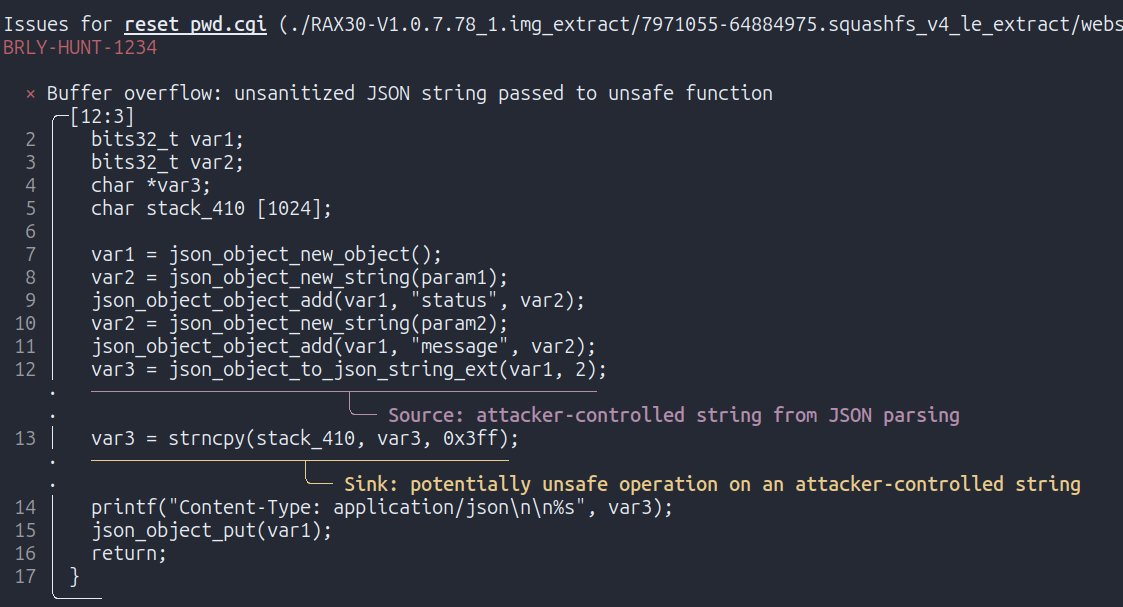





@francesco_ev will be presenting VulHunt, our framework for scalable vulnerability detection and hunting, at @REverseConf this year!

On my way to @DistrictCon with new firmware update verification bypass on Supermicro BMCs (previously "fixed"). NEW: CVE-2025-12006 & CVE-2025-12007) @ant_av7 👏 Backstory: Ghost in the Controller binarly.io/blog/ghost-in-… Broken Trust binarly.io/blog/broken-tr… Stay tuned!

【体調最高ラジオ・特別回】話題の「高額療養費制度」。知らないうちに決まりかねない制度変更が、誰の生活に、どんな影響を与えるのか。数字と現場の声から見えてくるのは、医療の話であり、暮らしの話であり、これからの選択の話。選挙前に、立ち止まって考えたいテーマです。医療統計学者の伊藤ゆり先生に、たっぷり語っていただきました。国民の誰もにかかわる話です。 podcasts.apple.com/jp/podcast/%E7…
