0x4d5a
83 posts

0x4d5a
@0x4d5aC
CTF Player at @ALLESctf and @Sauercl0ud! Security Researcher @Neodyme. Mostly RE, pwn and Windows internals


Recently my RE workflow moved into sandboxed VMs where agents have full control over the environment. I needed an MCP server that runs headless in the same sandbox and exposes way more of the #BinaryNinja API than others. Here's the release: github.com/mrphrazer/bina…



WriteAccountRestrictions fun (@unsigned_sh0rt), RCE in Dell UnityVSA (@SinSinology), Unity Runtime exploit (@ryotkak), Lenovo DCC LPE (@0x4d5aC), and more! blog.badsectorlabs.com/last-week-in-s…





From iframes and file reads to full RCE. 🔥 We found an HTML-to-PDF API allowing file reads and SSRF - then chained it into remote code execution via a Chromium 62 WebView exploit. 👉 Read the full write-up here: neodyme.io/en/blog/html_r…







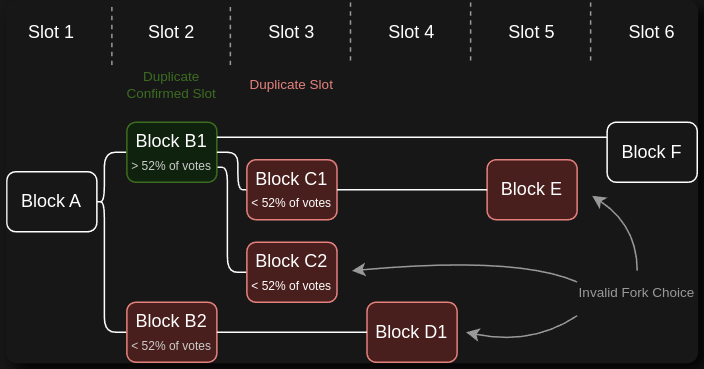
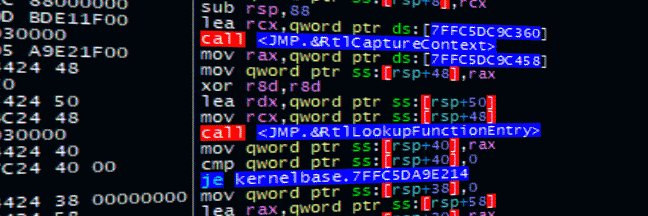
Following our #38c3 talk about exploiting security software for privilege escalation, we're excited to kick off a new blog series! 🎊 Check out our first blog post on our journey to 💥 exploit five reputable security products to gain privileges via COM hijacking: neodyme.io/blog/com_hijac…