ADR19c | 🌋 💎
6K posts


@0xADR19c
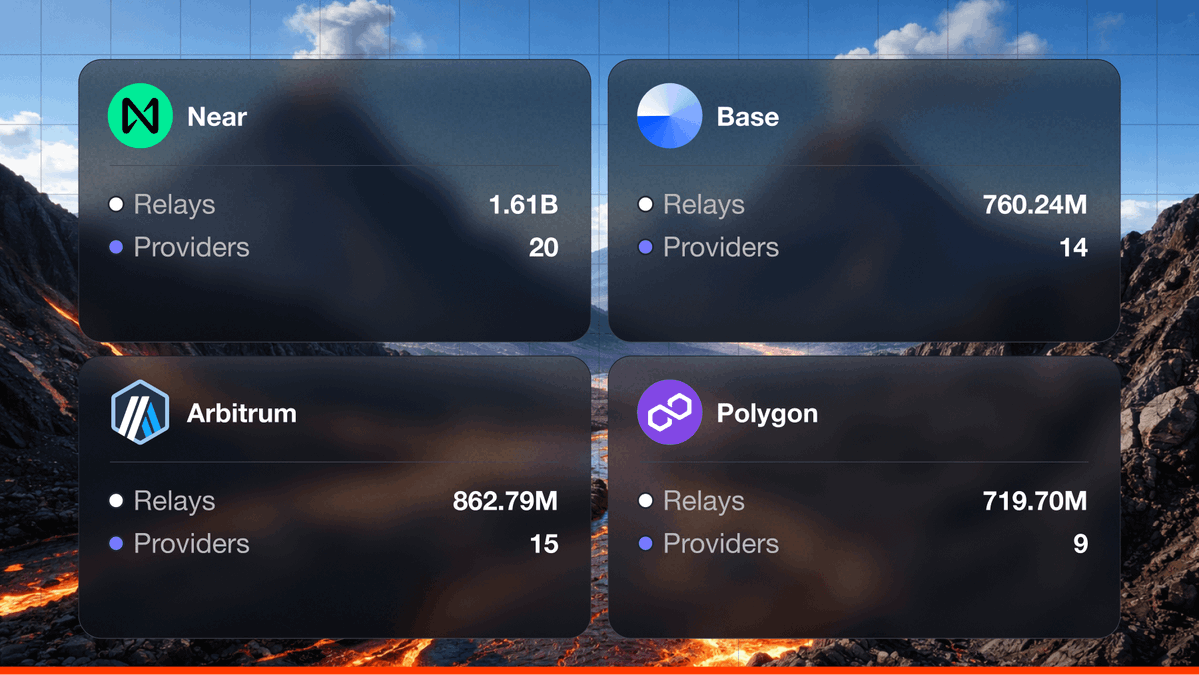
https://t.co/2ZEEqn5IQi CMngr/MOD - @lavanetxyz - RPC provider CT/CMngr/MOD - @TakaraLend - Lending Protocol on Sei Network





RPC security has been on my radar since day one in this space- long before it became a headline. After years of building on the infra layer, the team just shipped something I'm genuinely proud of: a security product that addresses exactly the attack vector behind the @KelpDAO exploit. If you're running on-chain infra, now is a good time to check your exposure. Great work team. TBC

5 questions every CISO should be asking after the KelpDAO exploit: 1. Do you run your own RPC infra? 2. Do you rely on one primary RPC provider for critical decisions? 3. Do you validate RPC responses across providers, including fallbacks? 4. Do you require multi-source quorum for sensitive operations? 5. Do you use cryptographic proofs to verify on-chain data? If you're not sure about any of these, the full assessment takes 5 min: secure.magmadevs.com

5 questions every CISO should be asking after the KelpDAO exploit: 1. Do you run your own RPC infra? 2. Do you rely on one primary RPC provider for critical decisions? 3. Do you validate RPC responses across providers, including fallbacks? 4. Do you require multi-source quorum for sensitive operations? 5. Do you use cryptographic proofs to verify on-chain data? If you're not sure about any of these, the full assessment takes 5 min: secure.magmadevs.com



RPC security has been on my radar since day one in this space- long before it became a headline. After years of building on the infra layer, the team just shipped something I'm genuinely proud of: a security product that addresses exactly the attack vector behind the KelpDAO exploit. If you're running on-chain infra, now is a good time to check your exposure. Great work team. TBC

The $290M KelpDAO exploit made one thing clear: compromised RPCs are a lucrative attack vector. We've been helping teams harden their RPC setups against similar attacks. We built a 5-min assessment to check your exposure: secure.magmadevs.com

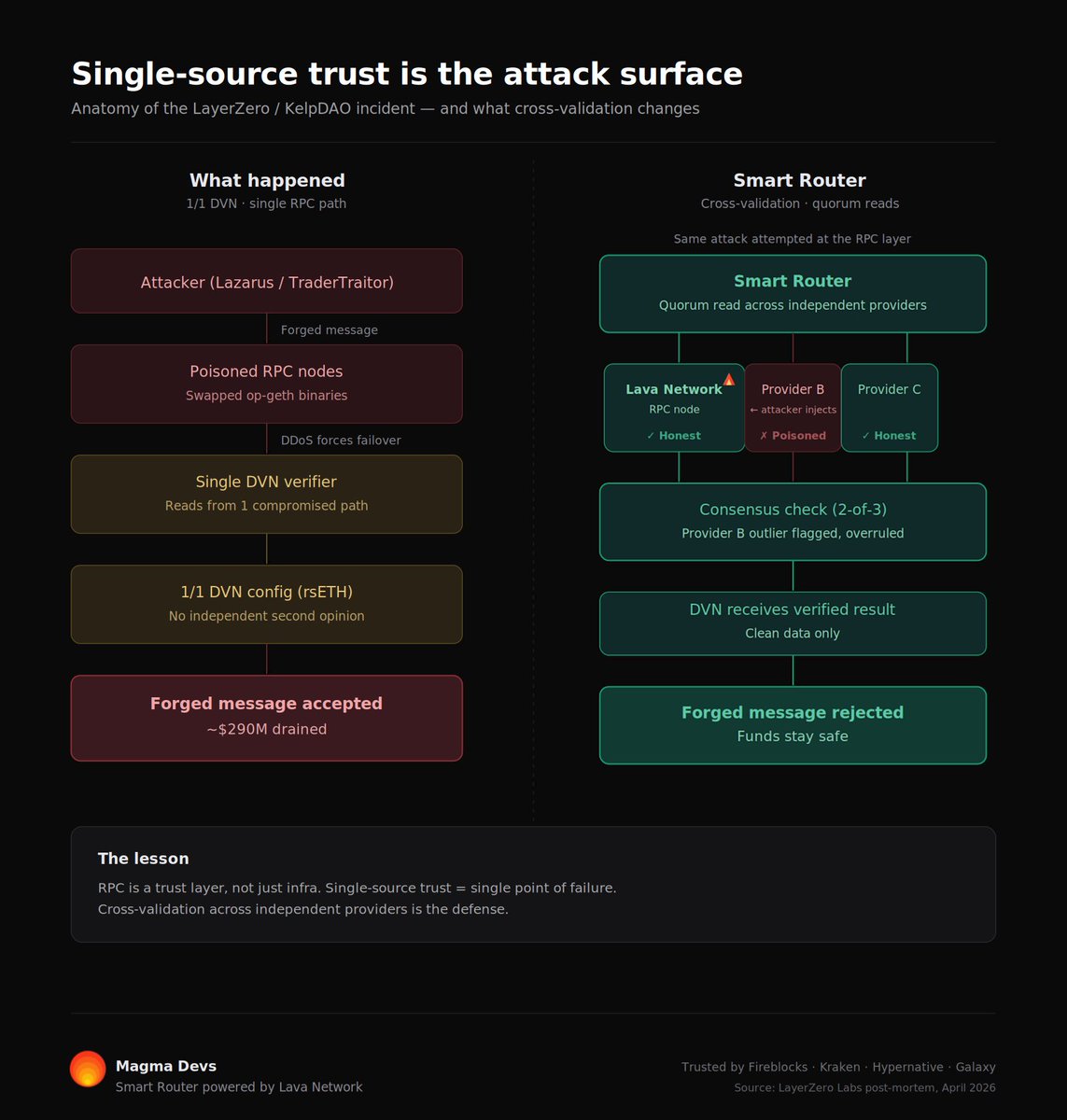
The $290M KelpDAO exploit made one thing clear: compromised RPCs are a lucrative attack vector. We've been helping teams harden their RPC setups against similar attacks. We built a 5-min assessment to check your exposure: secure.magmadevs.com

If your RPC lies, your entire system acts on bad data. That's not a downtime risk. That's a $290M risk. @yaircleper from @magmadevs breaks down the KelpDAO/LayerZero hack from @decentrallugano and why quorum-based RPC validation is the architectural answer the industry needs.