c0rnbread
52 posts

Sabitlenmiş Tweet

Today I'm releasing Xenon, a custom Mythic agent for Windows targets written in C.
Notable features include:
📁 Modular command/code inclusion
🦠 Malleable C2 Profile support
🪨 Compatible with Cobalt Strike BOFs
github.com/MythicAgents/X…
Blog series -
c0rnbread.com/creating-mythi…
English
c0rnbread retweetledi

The RedSun zero-day proved that you cannot patch against bad logical design.
We are broadcasting The Operator View live right here on X today at 1:00 PM EST.
Nick Swink (@0xC0rnbread ) is performing a deep-dive dissection of the recent Windows LPE 0-day vulnerabilities by Nightmare-Eclipse.
Today’s agenda:
Full breakdown of the RedSun exploit code.
Live demo: Standard User -> NT AUTHORITY\SYSTEM.
Why the vendor’s initial dismissal created a crisis for the enterprise.
Join us at 1:00 PM EST to see the technical ground truth of the RedSun exploit. Drop your questions in the replies and we will address them live.
#CyberSecurity #0day #LiveStream #InfoSec #ThreatIntel #TheOperatorView #Armada #ArmadaOps #RedSun

English

@lildylannn Great research! It was quite the adventure working with Claude to get the c-style COM interfaces / headers / etc. still mulling over what the “so what” or use case is really gonna be for the BOF version
English

👀 Claude go brrrrr
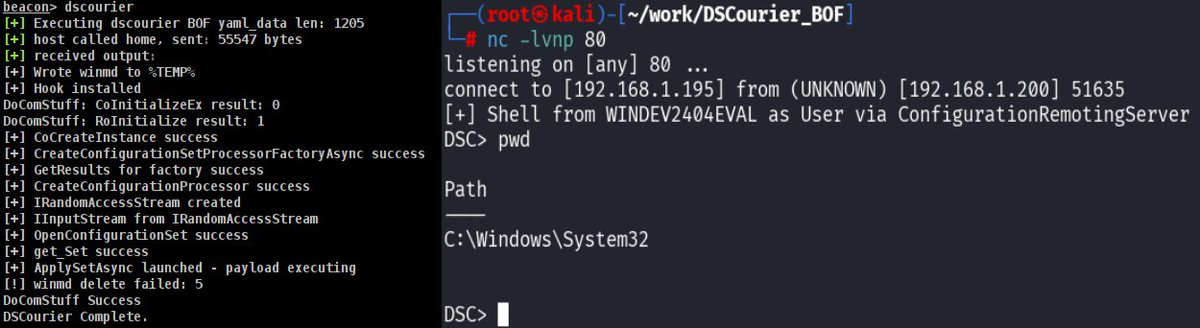
dylan davis@lildylannn
I just dropped some research: DSCourier and would love for your opinion and to check it out!! It’s a novel post-exploitation technique abusing WinGet’s COM API to execute code through Microsoft-signed binaries. GitHub: github.com/DylanDavis1/DS… Blog: dylansec.com/DSCourier/
English

@sullycodesstuff @weezerOSINT That's incorrect actually, you do not have to be local admin to use this and get a SYSTEM shell
English

@weezerOSINT this is a uac escalation exploit
there’s another that is still unpatched and has been around since at least nt 6.0
no popups, no detection, etc
this is nothing new
had the same experience reporting to microsoft, they brushed me off, even gave them fully functional poc source
English

Windows defender has been compromised.
right now there is a public unpatched exploit that gives any app on your windows PC full system admin access. no password. no popup. nothing
your antivirus doesnt stop it. your antivirus IS the exploit. windows defender is the attack vector
ransomware gangs can use this to encrypt your entire machine and steal every saved password, browser session, and discord token you have. fully patched windows 11. real time protection on
thread


English
c0rnbread retweetledi

Another zero day exploit released by some nerd (can't remember name right now) because they're annoyed with Microsoft. It's been confirmed by other nerds. It is yet another legit zero day. Whew.
github.com/Nightmare-Ecli…
English
c0rnbread retweetledi

Reminder: We are broadcasting The Operator View live right here on X today at 1:00 PM EST.
Nick Swink (@0xC0rnbread ) is taking over the timeline to show exactly how malicious browser extensions silently steal credentials and bypass your MFA.
You do not even have to leave the app to watch the full technical breakdown.
Drop your questions in the replies and we will see you at 1:00 PM.
#CyberSecurity #AppSec #LiveStream #InfoSec #ThreatIntel #TheOperatorView #Armada #ArmadaOps

English
c0rnbread retweetledi

GDC day 3 is here!
Tomorrow morning, we’re taking the stage to talk about the "wild west" of game enforcement.
Armada's very own Threat Intelligence Lead, Steven Guris, will be sharing how we hunt down bad actors and protect IP at scale.
Don’t let your EULA be just a piece of paper. Steven will discuss:
- Tracking anonymous targets across borders
- Turning intel into legal action
- Real-world strategies for fraud & anti-cheat
📍 Catch him tomorrow, 3/11 at 11:30 AM PT in Room 2000, West Hall
#GDC2026 #ThreatIntelligence #GameSecurity #InfoSec #CyberLaw #ArmadaExperts #ArmadaOps

English
c0rnbread retweetledi

Leveling up game security requires more than just code. It takes a solid legal strategy. 🛡️ 🎮
Catch Threat Intel Lead, Steve Guris at #GDC2026 on March 11th (11:30 AM PT) for an essential panel on fighting fraud, cheating, and IP infringement. Learn how @armadaops and other industry leaders coordinate across legal and security teams to protect players.
See you there! 🤝
#GDC #GameDev #GameLaw #CyberSecurity #IndieDev
English

Join if you want to work through an obfuscated mess with me!
Armada@armadaops
The Operator View webcast is going LIVE TODAY @ 1pm ET here on X! 🚀 Join @0xC0rnbread where he will be covering a recent Supply Chain Attack on Plone CMS. He will be doing a deep-dive into what happened and a malware analysis of the ACTUAL cross-platform JavaScript malware 🦠, including features like heavy obfuscation, EtherHiding, websocket C2, and more.
English
c0rnbread retweetledi

DC bound!
We are officially a Silver Sponsor for @DistrictCon this weekend and we couldn't be more excited to support this amazing community.
Looking forward to the talks, the hacking, and meeting all of you. Come say hi!
#DistrictCon #ArmadaOps #Security #risk3sixty

English
c0rnbread retweetledi

Having responded to probably hundreds of incidents at this point, from ransomware to APT's, in my experience, the lack of knowledge on how to adequately secure Entra applications and service principals continues to be the biggest knowledge gap most defending teams have.
You should be able to securely configure apps, detect compromise of apps and understand how to investigate compromise of apps. It seems overwhelming at first, but it isn't.
Get started like this
Secure them:
•Use managed identities where possible - negates the need for credential handling
•Limit privilege - reduce both the permissions granted and add additional API specific restrictions (i.e don't grant read/write all to all SharePoint sites, just the ones an application needs to access). This includes pushing back on vendors or internal teams that request privilege not required
•High privileged applications should have no direct owners - lower privileged users can be granted direct ownership of an app, don't do this, govern the ability to manage applications via Entra ID roles
•Configure credential restrictions such as requiring shorter lived secrets or enforcing use of certificates
•Remove unused apps and service principals, this can prevent existing high privileged apps being leveraged and reduces your supply chain compromise footprint for multitenant apps
•Monitor risk events for service principals like you would users
Detect compromise of them:
•Alert on application creation or application credential creation - may be noisy in large environments, but a good starting point
•Alert on credentials being added to service principals - credentials generally live on the application object, service principal credential creation should be rare
•Alert on permission consent - this can detect not only malicious activity but permission creep
•Alert on anomalous resource access - does your app usually access only Azure Storage, and suddenly it accesses Microsoft Graph? - this may indicate a compromised credential
•Alert on anomalous ASN or location access - does your app usually access only from a specific ASN or country, and suddenly that changes? - this may indicate a compromised credential
Many of these are covered by Defender for Cloud Apps and other tools out of the box, but it is worth ensuring you are covered down and what they actually mean.
Investigate compromise of them:
Know how to query the following logs and understand the events surfaced
•Entra ID sign in data - filter on service principal sign in events via the Entra portal or Kusto in the Defender XDR portal
•Entra ID audit logs - filter on events related to the service principal via the Entra portal or Kusto in the Defender XDR portal. Service principals can be used to further establish persistence, such as creation of users or additional service principals, rinse and repeat for any malicious additions to your environment
•Microsoft Graph - was the compromised app used to access data via Microsoft Graph? You can query via the Defender XDR portal using Kusto to find these events
•Defender for Cloud Apps - did the compromised app access other M365 services? You can query via the Defender XDR portal using Kusto to find these events
•Unified Audit Log - you can retrieve the events related to the compromised app via the audit functionality inside the Defender XDR portal
English
c0rnbread retweetledi

We are extra thankful for our incredible lineup of Year 1 Sponsors for DistrictCon! districtcon.org/sponsorships

English
c0rnbread retweetledi

Back in May our team discovered a vulnerability in Netgear routers. Check out the writeup here: risk3sixty.com/blog/hardware-…
English

Last year I wrote about an attack path I executed on a real engagement.
Compromised a self-hosted GitLab runner which lead to pwning every EC2 in their AWS account via SSM permissions.
Check out the blog post here 👉
Armada@armadaops
Devops is always a great attack vector for priv esc. risk3sixty.com/blog/attacking…
English

Devops is always a great attack vector for priv esc.
risk3sixty.com/blog/attacking…
English


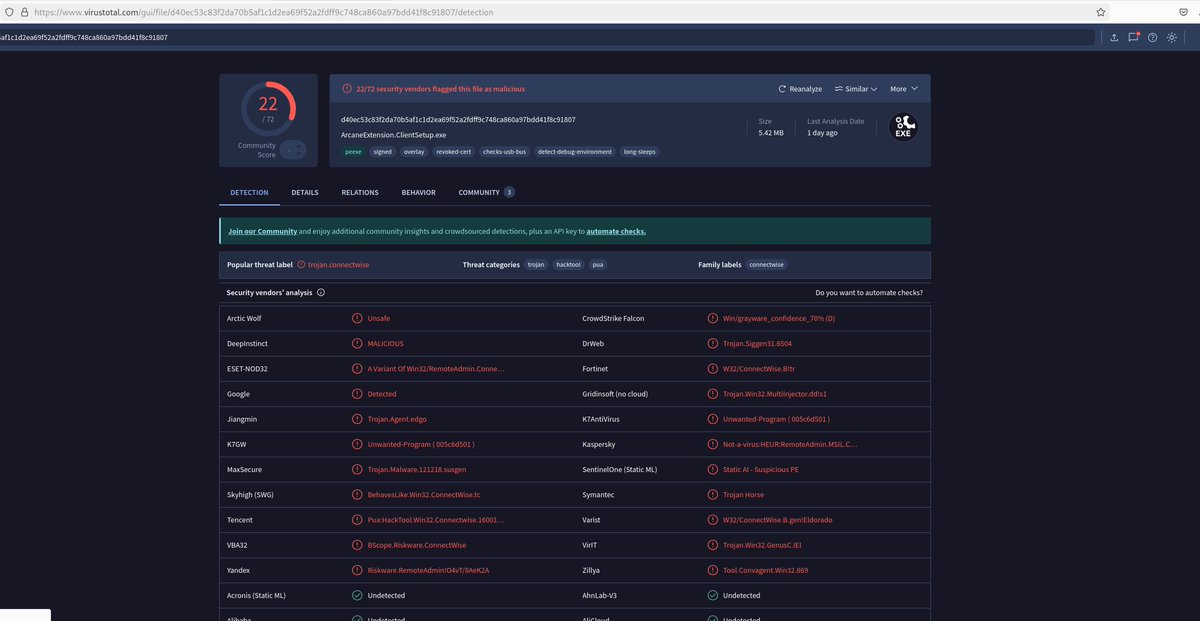
@0x0exchange Be advised! There is an active phishing campaign targeting Arcane wallet users.
It's currently the 3rd result when Googling "Arcane wallet extension".
The phishing page downloads a malicious Windows executable that tries to install remote access tool ScreenConnect.
English