Aref Abdollahi
87 posts



Aref Abdollahi retweetledi

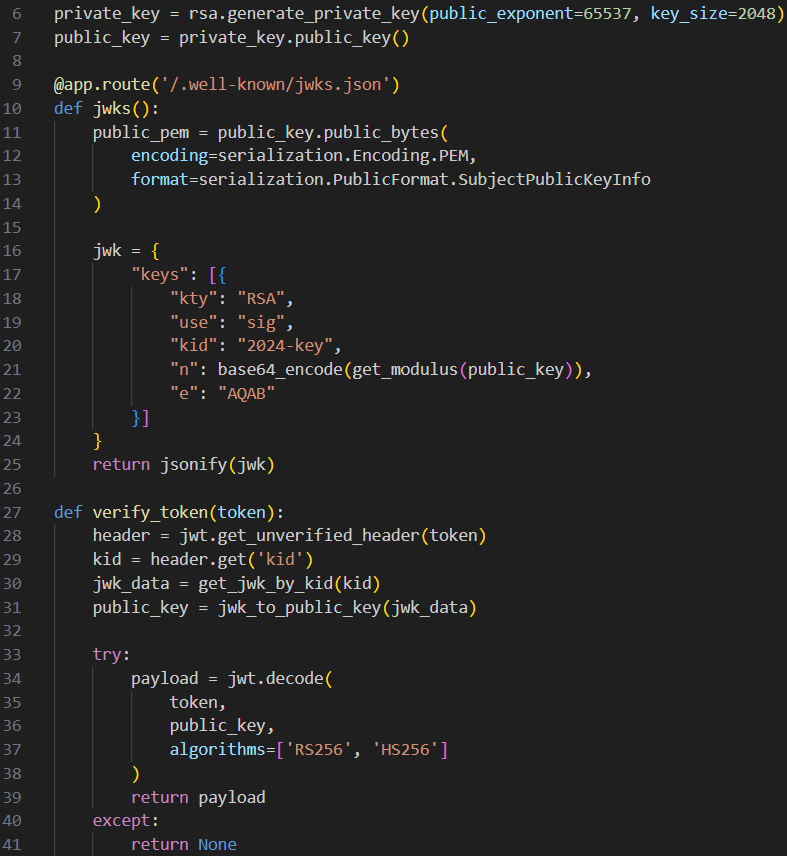
It's time for sharing, this is not a simple write-up, we are sharing our methodology and reasoning, detailing how we approached and hunted the flaw, I hope you like it :]
blog.voorivex.team/uxss-on-samsun…
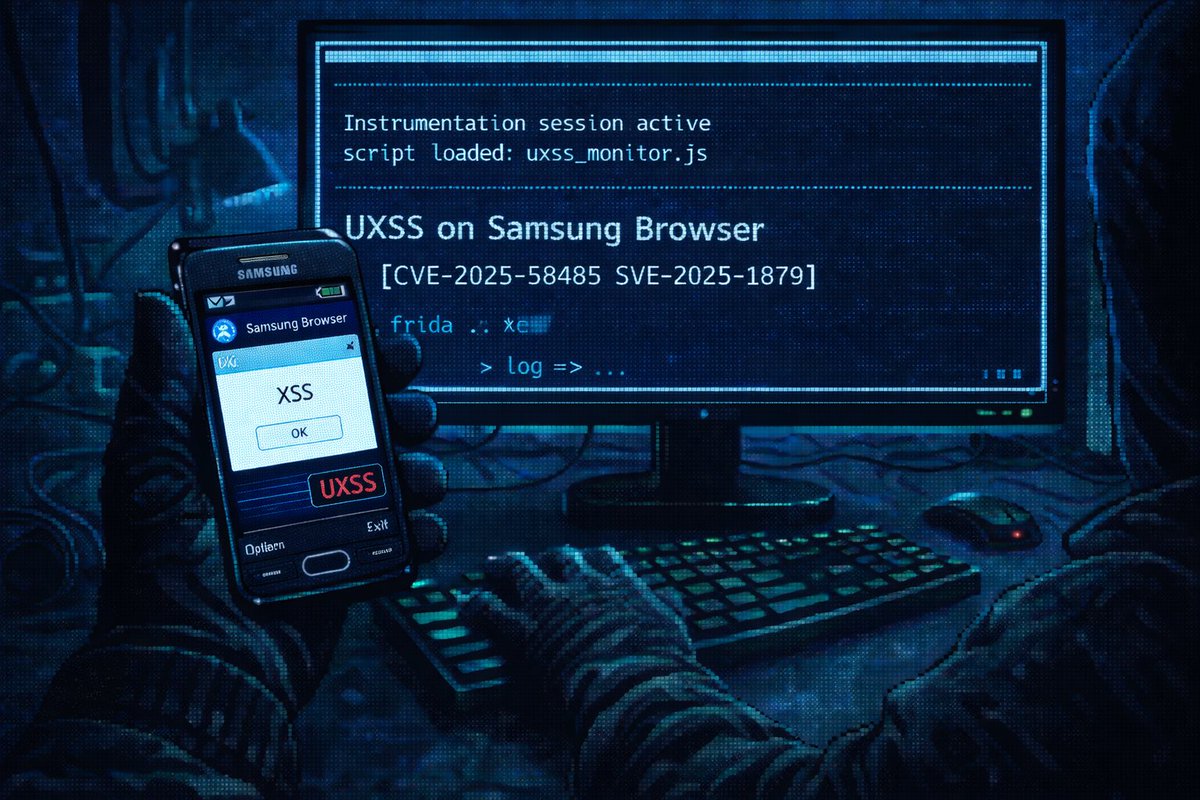
Omid Rezaei@omidxrz
We got permission from the Samsung Security team to disclose this uXSS that we found in Samsung Browser, it was assigned a CVE (CVE-2025-58485) and patched. Here is the PoC, expect the write-up in the next upcoming days.
English

@hetmehtaa More interesting thing is when you can find SSRF on its converter like HTML to PDF and extract sensitive data.
English

This website has all of your sensitive documents like Financial Records, SSN, Aadhar, Pan, DL, Heath Documents etc.
It might even have confidential government data as well. It's so easy to use, just upload & convert, all free of cost.
Banks insist on password-protected files, forcing people to rely on third-party tools just to unlock them.
Government portals impose arbitrary limits, like requiring documents to be under 500 KB in an era of virtually unlimited storage, so citizens go to these external sites for file compression. These unnecessary hurdles are created by institutions, while ordinary people are left to deal with the inconvenience and privacy.
Aditya@AdityaShips
Whoever built this, you just saved my entire day
English
Aref Abdollahi retweetledi

This was some really nice research by @zerodaykb from late last year: lab.ctbb.show/research/unico… - this trick can be super useful in secondary contexts!
English

@RoundtableSpace Everybody uses mac studio, why they don't use nvidia spark really?
English
Aref Abdollahi retweetledi

Step 3: Watch the #NahamCon talk tonight! I hope this is useful for some of you, especially if you’re new to the subject. Check @NahamSec messages for the exact time.
This was a 3–4 hour in-person workshop, turned into a 90-minute talk. I recommend following the side quests, and feel free to ask me questions or submit PRs for the lab:
github.com/irsdl/viewstat…
Note: YSoSerial .NET v2 needs a few tweaks to work properly. Please be patient, and you may need to use an older Visual Studio version, like Visual Studio 2017.

Soroush Dalili@irsdl
So yes CrapSecrets is a thing for now 😅 hopefully BadSecrets can catchup soon! github.com/irsdl/crapsecr…
English

Unfortunately my workshop for exploiting asp .net viewstate in most scenarios didn't make it to @BSidesLondon due to other better workshops perhaps! Damn it AI categories 🤭
Please comment if you would like to read a blog post in a lab like style about it. You will need to have your own IIS server to follow it.
Given it is asp net and IIS I thought people might not be too interested.
I had presented a version of this in a Synack (SRT) meeting a few months ago.
English
Aref Abdollahi retweetledi

Our Security Researcher @softpoison_ published his first research post, reverse engineering CVE-2025-54236 (SessionReaper) - a critical unauthenticated RCE in Magento. From understanding @Blaklis_'s original discovery, we wrote up our analysis here: slcyber.io/assetnote-secu…
English
Aref Abdollahi retweetledi

📢 Confirmed! @SinSinology and @_mccaulay of @SummoningTeam used a pair of bugs to exploit of the Synology ActiveProtect Appliance DP320. That rounds their day off with another $50,000 and 5 more Master of Pwn points. (And clean that screen!) #Pwn2Own

English
Aref Abdollahi retweetledi

I'm teaming up with @Ch0pin to hack the Samsung Galaxy S25 this year!
And holy shit we can't wait to disclose what we fucking found!
TrendAI@trendaisecurity
The draw is on. Good luck to all the participants! #P2OIreland #Pwn2own @thezdi
English
Aref Abdollahi retweetledi

The watchTowr Labs team is back, providing our full analysis of the Oracle E-Business Suite Pre-Auth RCE exploit chain (CVE-2025-61882).
Enjoy with us (or cry, your choice..)
labs.watchtowr.com/well-well-well…
English
Aref Abdollahi retweetledi

Surprise episode drop! Thanks @pod2g for coming on the pod to talk about the early days of iOS hacking 📱😊
open.spotify.com/episode/6795JF…
PS: this episode was recorded before the release of MTE so adjust for that 😅
English

@hkashfi به نظرم Mobile Exploitation به اندازه کافی جذاب هست، همون رو ادامه بدیم، مخصوصا iOS
فارسی
Aref Abdollahi retweetledi

I'm working on a new Android hacking course together with Mobile Hacking Lab
It will review the current record holder of "most amount of bugs used in a single Pwn2own entry"
For a limited time, you can pre-order the course for 50% off
Check it out here: mobilehackinglab.com/course/advance…
English
Aref Abdollahi retweetledi

Sup, I'm the guy that hacked the Samsung S24 during Pwn2Own Ireland 2024
I just released a non-beginner Android application security course on Udemy. The course is released under my company, Malicious Erection LLC
Check it out here! udemy.com/course/pentest…
English
Aref Abdollahi retweetledi

NEED YOUR HELP!
My Friend/Teacher Soroush (@irsdl) Is looking for a new company to join, you know him as the .NET-God, the guy who has popped exchange, sharepoint, has maintained ysoserial_.net for years, contributed to the exploitation scene numerous times, taught all of you about what .net ghost webshells are, taught you about what viewstate exploitation is, how .net remoting exploitation issues can be solved, iis cookieless, web_config exploitation, countless of blogs, talks, techniques,...
but companies keep saying:
"we aren't hiring right now!"
if i was in position of hiring, woudln't wanna miss out on having one of THE BEST in my team
you're retweet is Extremely appreciated ❤️🔥
soroush, if you see this, don't hate me, had to do it without telling you
English