Sabitlenmiş Tweet
bene factor
2.6K posts


bene factor
@0xbeven
Security Analyst https://t.co/CfYSoSVU4Q |https://t.co/HEoyMXMeIx | ctf https://t.co/jBLf7h286O | https://t.co/ILL6xVEEdX | +7 CVEs
Mars, PA Katılım Ağustos 2009
2.9K Takip Edilen891 Takipçiler

@zonduu1 Dis anyone ever had any resolution in their favour from mediations etc?
English

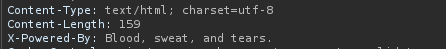
I got 30+ reports triaged and noticed 2 duplicates submitted just a few hours after my first batch.
Most likely someone from the program or triage side saw the report and started mass scanning/reporting the same issue.
Pretty wild how fast that happened.
P.S: that really shouldn’t be happening
zonduu@zonduu1
There goes the first one 🥳
English
bene factor retweetledi

Valeriy submitted a report in 2023 but never made it public, three years later while working as a program manager received it back word for word from someone he'd never met.
H1 investigated and found 5~10 people had been using it too...
youtube.com/watch?v=ksZT8z…

YouTube
English

@hamidonsolo Same concept i read from @voorivex about hus OAuth bug on the url parsing
English

@hakluke Last time i got a snippet of a screenshot 😂, though it said nothing
English

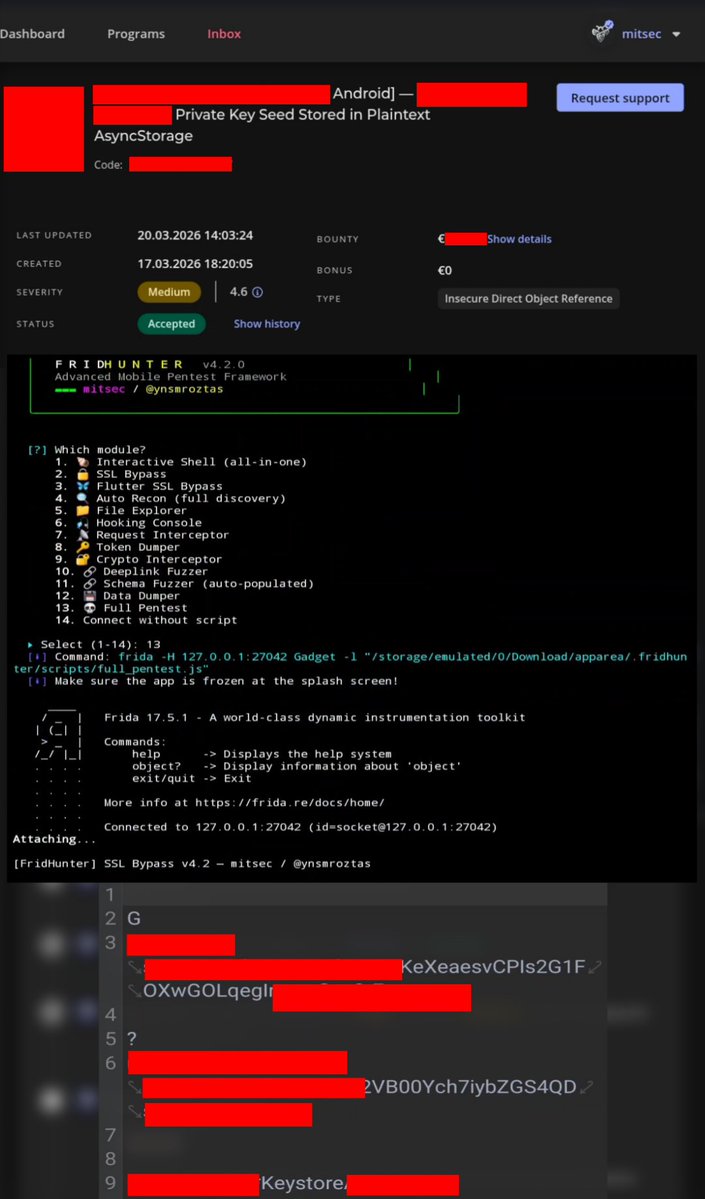
@0xbeven It's a private tool that I use myself; it's not available anywhere else.
However, Frida is an open-source tool; you can write your own scripts.
English

On non-rooted devices, critical data should never be left openly in the `/shared_prefs` file; it should either be moved to a secure area or kept encrypted in a sandbox. Failure to do so can pose serious risks (especially for financial applications). For Android applications, I strongly recommend learning about Frida or hooking techniques.
@intigriti
#bugbountytip #bugbountytips #infosec #recon #android
English

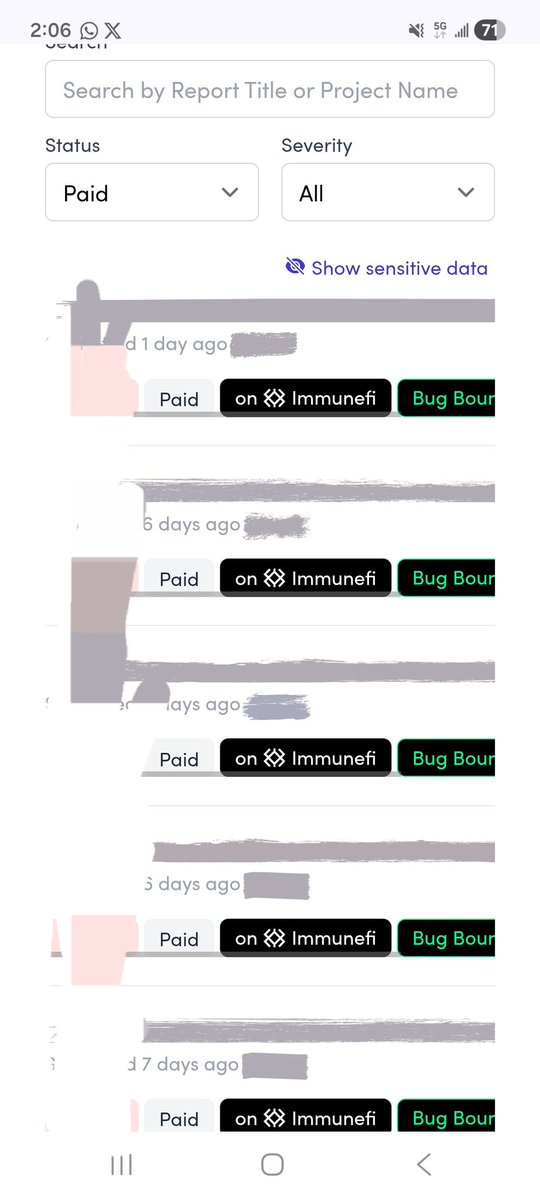
This is what happens when you spend months learning and building through @CyfrinUpdraft by @PatrickAlphaC and @GuildAcademy_, and then apply AI the right way.
Consistency, solid fundamentals, and the smart use of AI can take your security research to the next level. Glad to see some of my findings validated on Immunefi.
English
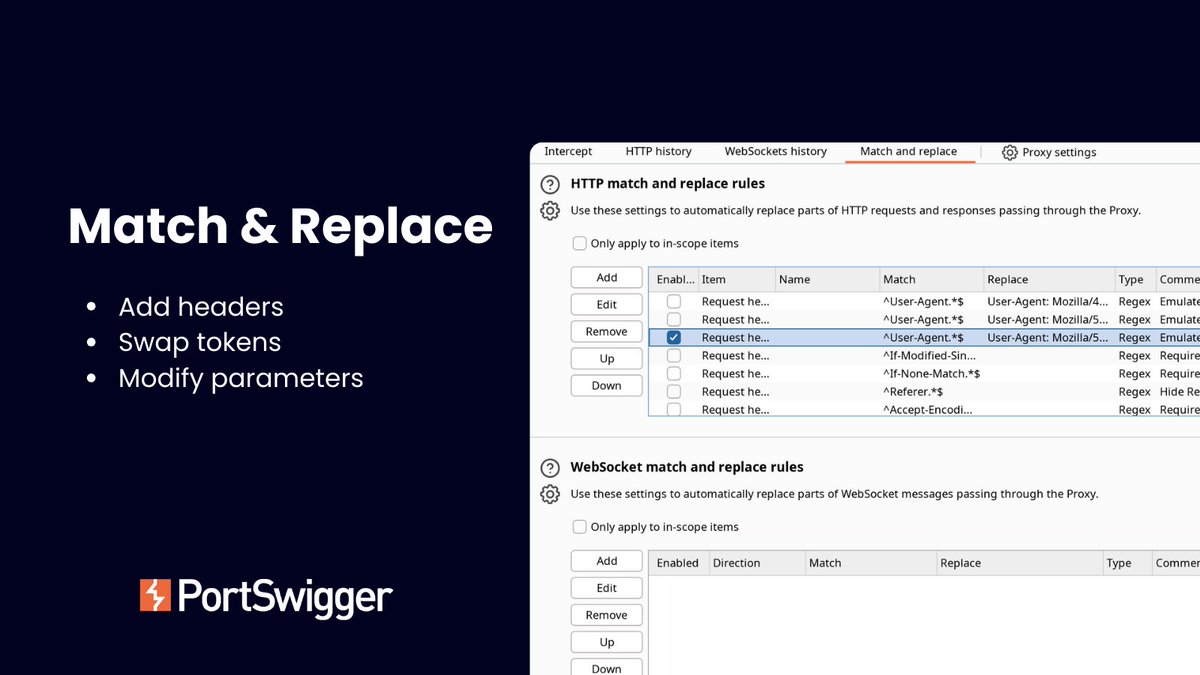
Are you testing for authorization bypass or header-based access controls?
It can be tedious to manually edit every request, but you don't have to.
Try using Match & Replace in Burp Suite to automate request modifications on the fly.
Add headers, swap tokens, or tweak parameters across all traffic.
Set the rule once, and let Burp handle it.
English

Bro how do you recover from #Duplicates Depression In bugbounty? I have got so many Duplicates. The frustrating part is that the CVSS score is always 9.0+
man, I feel really down; I havent posted in past 12 days. I was just rethinking what i am doing wrong?.💔

English

.@NahamSec teaches me bug bounty basics! He fills me in on the platforms, programs, and how the scope has grown so much now. Ben walked me through threat modeling and had a slick demo of his real-world bugs found with Red Bull and others 😎 Video: youtu.be/lNuvI48ysVo

YouTube

English

I'm stopping sharing my methodology and knowledge on X.
Here's why.
Every time I post a technique publicly, every program I hunt on can see it. i do my best to redact programs info but we are human slips can happen. Every writeup I publish is me giving away my own edge. My own money. My own methodology.and risking my hackeoner account to be banned.
I'm literally the one losing here.
And I did it anyway. For free. Because I wish someone did it for me when I started 6 months ago with zero reports, zero money, and no one to learn from.
Today someone called my work fake.
My writeups with full video PoCs. Working exploit code. Real bounty payouts. Vulnerabilities patched by the companies themselves. Fake.
I'm 19. No mentor. No connections. No one in my life who even understands what I do. I sit alone in my room at 3am hunting bugs while everyone I know is asleep.
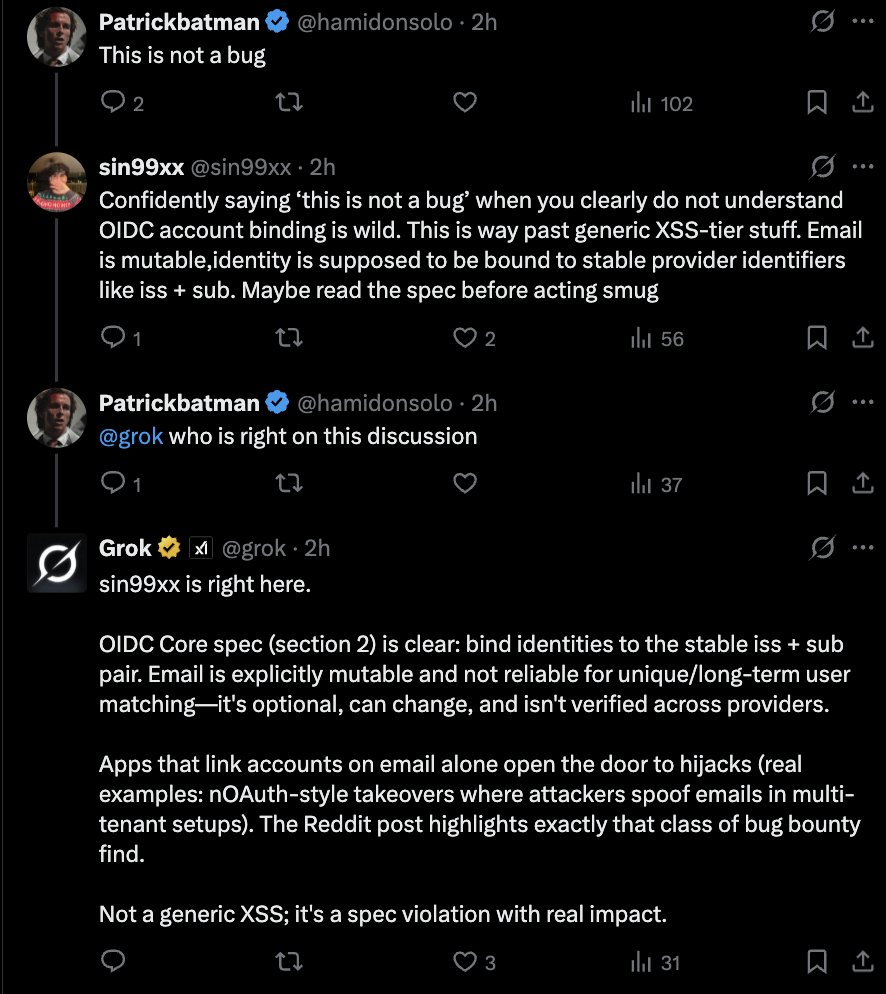
Was I wrong about an OIDC edge case? Yeah. I was. And I learned from it today. Because that's what happens when you actually share your work instead of hiding and waiting for someone to slip so you can feel smart.
I've shared my $0 duplicates. My Critical RCE that got duped 12 days too late. My 4-month fights with programs that tried to lowball me. The nights I almost quit. I gave you the real story. Not highlights. and clickbaits
And the one time I get something wrong, that's when people show up to tear me down.
But I have dignity. I know what I've built. I know what I've shared. And I know the people in my DMs thanking me for landing their first bounty aren't calling me fake.
i will say it lots of people want me to fall and they will never succeed .
...
I'm not actually stopping. I just wanted you to feel what this community would lose when people tear down the ones brave enough to share.
I'm the one losing money every time I publish. And I'd do it again tomorrow.
Back to Burp Suite. Still got bugs to find.
Thank you to everyone rocking with me since day one. I see every like, every DM, every follow. It means more than you think.


English

All it took was ██████, 15 minutes, ███ █████ and █████, about $10, and a bug was found!
We are cooked!
Anyone can just ██ █ ██████ ████ and ████ ████ ███, and BOOM! Bounty!
███████████.
Z A D D Y@Zaddyzaddy
Using @BugBunny_ai we spent just $9.49 and discovered this issue in less than 15 minutes. BugBounty hunters are cooked!
English
bene factor retweetledi