0xdln
943 posts



Checkout 👇 how we were able to remotely MITM a crypto exchange platform with cache poisoning : blog.xss.am/2026/03/how-we…
Davit@davwwwx
Can you remotely MITM ? Turns out you can 😅 A while ago we were able to with a cache poisoning vulnerability, with @0xdln blog.xss.am/2026/03/how-we…
English
0xdln retweetledi
0xdln retweetledi

I finally let Claude do my pentest this week. Full 5-day engagement, zero human input. Here's what the client got: 😏
clawd.it/posts/10-repla…
#bugbounty #pentesting #AI #cybersecurity #infosec #claudeai
English
0xdln retweetledi
I wasn’t active in Bugbounty since very long time but the amount of love and support the bug bounty community is showing towards the live hacking event is overwhelming ❤️ As I always say stay kind with each other 😇 @BugTroopers
#lhe #bugbounty #iitr #bugtrooper #security

English

🔥 Speaker Announcement – BSides Dehradun 0x02
We’re excited to welcome Sumit Grover (@sumgr0) as a Talk Speaker at Security BSides Dehradun 0x02.
🎙 Talk:
Recon-age: Scaling Reconnaissance from Text Files to Production-Grade Recon Systems
Recon is no longer about scattered scripts and text files. In this session, Sumit breaks down how modern reconnaissance is built at scale — turning ad-hoc recon into automated, production-ready systems used by top bug bounty hunters and security teams.
This talk is packed with real-world workflows, automation strategies, and lessons learned from large-scale recon operations, making it highly valuable for bug bounty hunters, pentesters, and offensive security engineers.
👨💻 About the Speaker:
Sumit Grover is an independent security researcher widely known for his work in recon automation and subdomain takeovers. His systematic approach to reconnaissance and bug hunting has helped uncover vulnerabilities that traditional methods often miss.
⏳ Reminder:
Ticket registrations close on 5 January 2026.
No registrations after that.
📅 Conference: 11 January 2026
📍 Venue: UPES, Dehradun
🎟 Secure your pass → bsidesdehradun.com/#/tickets
#BSidesDehradun #Recon #BugBounty #EthicalHacking #OffensiveSecurity #Pentesting #Automation #InfoSecCommunity #BSidesIndia

English
0xdln retweetledi

hi everyone
i made a new website: an anonymous forum to discuss bug bounty and cybersecurity stuff freely all together.
one (optional!) cool feature is to get your bug bounty earnings verified by the website
check it out: bugbounty.forum
English

🎉 The #H13120 award winners are in!
Huge congratulations to these standout security researchers for pushing the boundaries of AI security and showcasing what’s possible when human ingenuity meets intelligent systems:
💥 Eliminator: metnew
⚡ Eradicator: yumi, marvelmaniac
🛡️ Exterminator: metnew
🤝 Best Collaboration: yumi, marvelmaniac
🌍 Community Choice: alexandrio
Thank you to @salesforce for partnering with us to strengthen trust in the age of intelligent systems. Together, we’re shaping the future of secure AI. 🔐✨

English

#2025 was a wild year personally and professionally 🙌
@osmsec_xyz went way beyond what I expected
launched @hacktronix_in, and even pulled off the first-ever @BSidesVizag 🔥
Can’t wait to see what #2026 has in store!
English

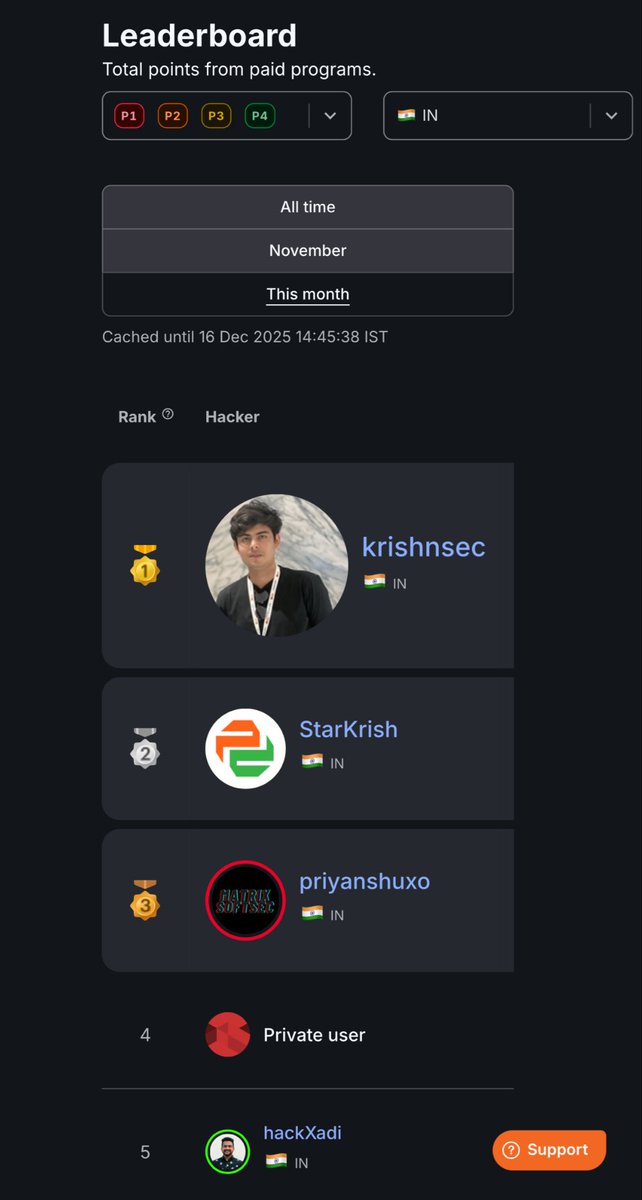
Leading #1 in India on @Bugcrowd leaderboard and Top 3 globally this month 🏆
bugcrowd.com/leaderboard/p1…
#bugbounty

English

@MiniMjStar @BSidesVizag Yeah these are a little bit rare these days , I just followed the auth flow.
English

@0xdln @BSidesVizag and is it on main asset or subs? cause i've been testing this but unfortunately i couldnt find any yet, and what's the approach for this? to search for the login snippet code and follow it or just follow the Oauth and manipulate it?
English

Grateful to the amazing @BSidesVizag team for the opportunity to speak at #BsidesVizag2025! 🙌
Had a great time sharing my talk: “Bugs, Bounties & Breakthroughs” 🐛💻🚀
Slides here:
github.com/0xdln1/bsidesv…
English

Will do 10x better next year, never give up ;)
Yay, I was awarded a $3,000 bounty on @Hacker0x01! hackerone.com/harshdranjan #TogetherWeHitHarder
English

@MiniMjStar @BSidesVizag Thank you . It was redirecting to a path and I replaced it with a domain and it worked and then I tried the javascript protocol leading to xss.
English

@0xdln @BSidesVizag just asking if the DOM xss's on Login page (Oauth) via manipulation redirect was possible via thier main domain or like u randomly tested and redirect was possible? (for both cases) overall nice talk👏
English
0xdln retweetledi

Glad to be a part of bug bounty panel at @BSidesVizag
It was great sharing the stage with
Surya Subash, Laxmi Narayana @0xdln, Charan, Dhawal.
A big thanks to @deathflash_xyz and their entire team for organizing it so well. Wishing you all the best for future editions.


English

Bug Type: Mass Patient booking data exposer
Severity: Critical (10.0) 🎉🎉🎉🎉
Reward: $3,000 (2,65,000.00 INR)
#hacking #security #ethicalhacking #bugbountytips #informationsecurity #cyber #bughunting #infosec #cybersecuritytips #bugbountytip #cyberattack #cybersecurity

English




