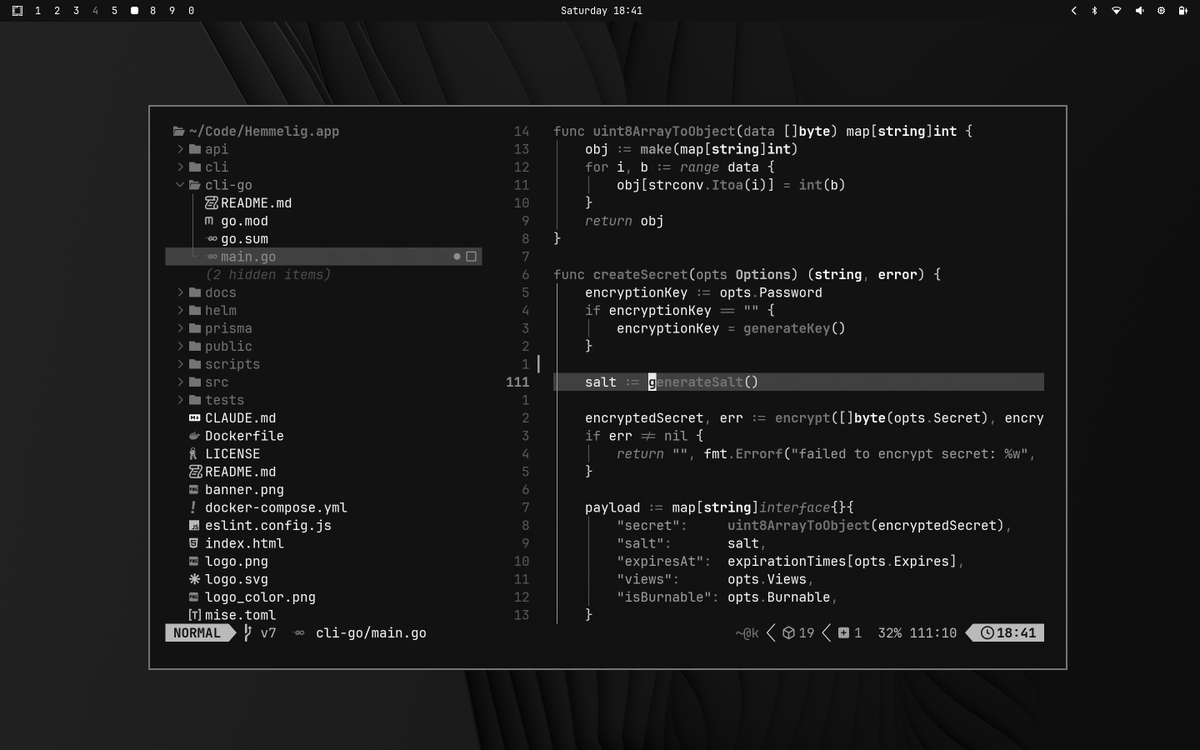
Zeth
294 posts



Hacking the #EU #AgeVerification app in under 2 minutes. During setup, the app asks you to create a PIN. After entry, the app *encrypts* it and saves it in the shared_prefs directory. 1. It shouldn't be encrypted at all - that's a really poor design. 2. It's not cryptographically tied to the vault which contains the identity data. So, an attacker can simply remove the PinEnc/PinIV values from the shared_prefs file and restart the app. After choosing a different PIN, the app presents credentials created under the old profile and let's the attacker present them as valid. Other issues: 1. Rate limiting is an incrementing number in the same config file. Just reset it to 0 and keep trying. 2. "UseBiometricAuth" is a boolean, also in the same file. Set it to false and it just skips that step. Seriously @vonderleyen - this product will be the catalyst for an enormous breach at some point. It's just a matter of time.






Franstalige website 21News op de vingers getikt voor 'kritiekloos' publiceren van speech van J.D. Vance #Echobox=1772710500" target="_blank" rel="nofollow noopener">tijd.be/ondernemen/med…







Today the HHS DOGE team open sourced the largest Medicaid dataset in department history. This dataset contains aggregated, provider-level claims data for a specific billing code over time. For example, using this dataset, it would have been possible to easily detect the large-scale autism diagnosis fraud seen in Minnesota. Download the data yourself: opendata.hhs.gov