Divyanshu Kothari
185 posts

Divyanshu Kothari retweetledi

🚨 If you're hunting GraphQL bugs, this repo is a goldmine
👉 “awesome-graphql-security” is a curated list of tools, techniques & real-world resources for both attackers and defenders
From recon → exploitation → learning paths… it’s all here
💣 Perfect for bug bounty hunters
🔗 github.com/Escape-Technol…
👇 Start exploring before others do
English
Divyanshu Kothari retweetledi

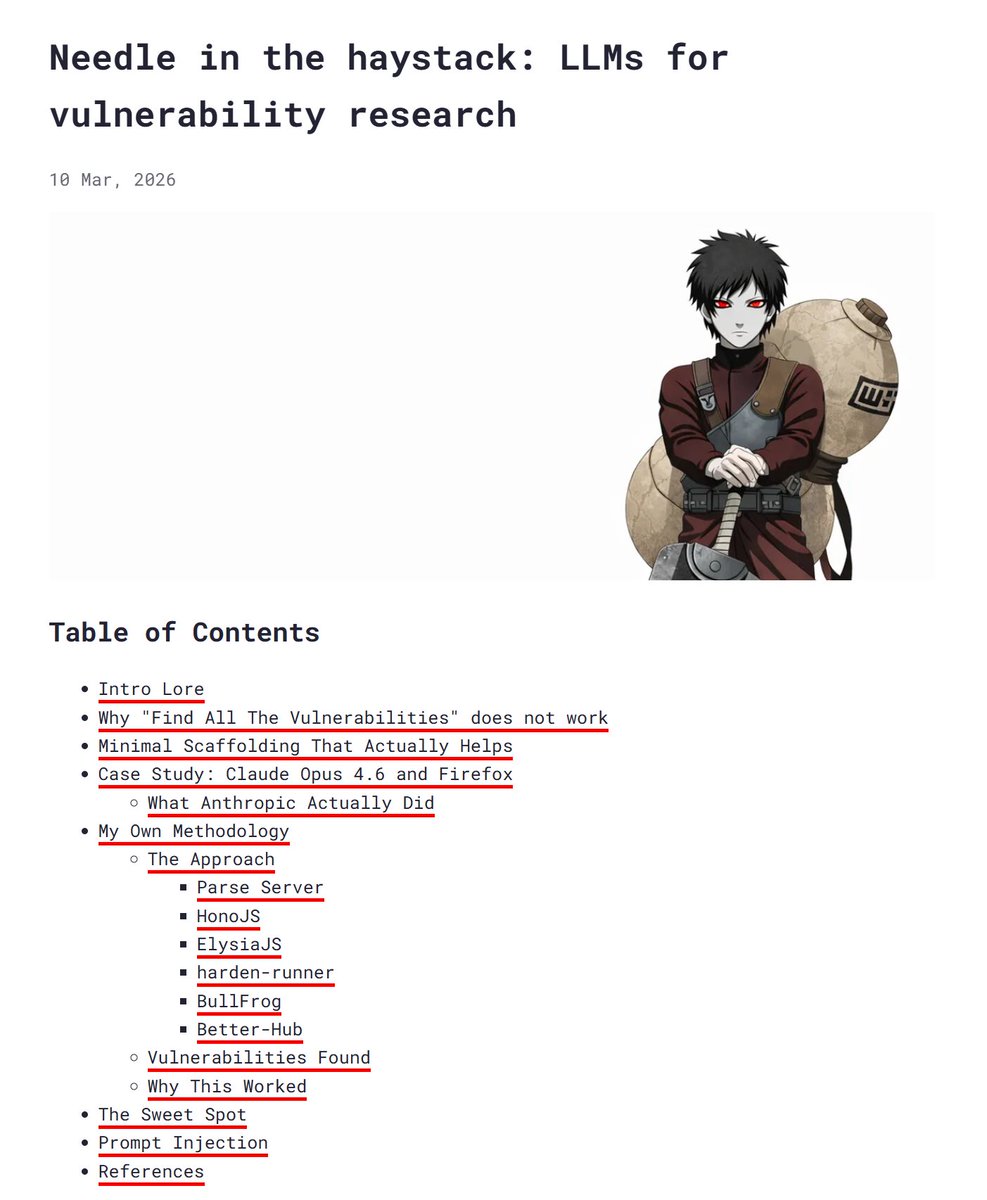
𝗥𝗲𝘀𝗲𝗮𝗿𝗰𝗵 𝗪𝗼𝗿𝘁𝗵 𝗥𝗲𝗮𝗱𝗶𝗻𝗴 - 𝗪𝗲𝗲𝗸 𝟭𝟮, 𝟮𝟬𝟮𝟲
AI doing research, AI killing CTF
🤖 𝗧𝗲𝘀𝘁𝗶𝗻𝗴 𝗔𝗜 𝗳𝗼𝗿 𝗩𝘂𝗹𝗻𝗲𝗿𝗮𝗯𝗶𝗹𝗶𝘁𝘆 𝗥𝗲𝘀𝗲𝗮𝗿𝗰𝗵: 𝟰 𝗔𝗽𝗽𝗿𝗼𝗮𝗰𝗵𝗲𝘀 & 𝗪𝗵𝗲𝗿𝗲 𝗜 𝗙𝗮𝗶𝗹𝗲𝗱
If you can only read one thing this week, make it this article: xclow3n.github.io/post/7.
🛠️ 𝗛𝘆𝗼𝗸𝗲𝘁𝘀𝘂 – 𝗦𝗼𝗹𝘃𝗶𝗻𝗴 𝘁𝗵𝗲 𝗩𝗲𝗻𝗱𝗼𝗿 𝗗𝗲𝗽𝗲𝗻𝗱𝗲𝗻𝗰𝘆 𝗣𝗿𝗼𝗯𝗹𝗲𝗺 𝗶𝗻 𝗥𝗘
Reversing Java and C# applications just became a lot easier thanks to the SearchLight Cyber team (ex: Assetnote): slcyber.io/research-cente….
🐧 𝗦𝗮𝘀𝗵𝗶𝗸𝗼
Sashiko is an agentic Linux kernel code review system that monitors public mailing lists to thoroughly evaluate proposed Linux kernel changes. sashiko.dev.
💀 𝗖𝗧𝗙 𝗶𝘀 𝗱𝗲𝗮𝗱*
A good rant on the impact of AI on CTF... k3ng.xyz/blog/ctf-is-de….
English
Divyanshu Kothari retweetledi

Most talentless sport itw. A genetic lottery
Hater Report@HaterReport
Bro CAN’T BELIVE his eyes I’M CRYING
English
Divyanshu Kothari retweetledi
Divyanshu Kothari retweetledi

Here's *everything* you wanted to know about @rez0__'s AI workflow for hacking
HackerNotes TLDR for episode 166: blog.criticalthinkingpodcast.io/p/hackernotes-…
►⠀Claude Code skills should encode knowledge the model lacks and enforce deterministic workflows, not replace its creative reasoning
►⠀Build a fallback architecture in skills: primary tool → SDK/library → raw API, so the agent adapts when one layer fails
►⠀Structure your notes as a funnel: notes → leads → primitives → findings → reports to keep multi-session hacking organized
►⠀Run two parallel agents (one guided, one free-roaming) and cross-compare results to continuously improve your methodology
English

@shydev69 I built something similar but running it locally for my own use
English

Introducing Reel Farmer
Paste a YouTube URL, get TikTok/Reel with animated captions in one command. Fully local.
> How it works:
1. yt-dlp downloads the video
2. LLM reads the transcript and picks the most clip-worthy moments
3. FFmpeg cuts each clip, silence removed automatically
4. Whisper.cpp runs locally for word-level timestamps
5. Remotion renders animated captions
6. Combines everything into 1080x1920 reels
Every stage checkpoints to SQLite. In case of a crash, it'll pick up exactly where it left off.
@MiniMax_AI M2.7 wrote the entire code.
English
Divyanshu Kothari retweetledi

It seems that my Burp AI plugin will never be in the BApp Store. The reasons are fair, but still 🥲
github.com/PortSwigger/ex…
English
Divyanshu Kothari retweetledi
Divyanshu Kothari retweetledi

Use this prompt for a thorough JS analysis:
You are an expert JavaScript reverse engineer and code analyst. I will provide you with
a JavaScript file. Perform a structured analysis with the following objectives:
## 1. High-Level Overview
- What is this code's purpose?
- Architecture pattern
- Key dependencies and frameworks used
- Execution flow: how does the code initialize and what is the main entry path?
## 2. Attack Surface & Endpoints
Extract and list ALL of the following in structured tables:
| Category | Examples to look for |
|-----------------------|---------------------------------------------------------|
| API routes/endpoints | paths, HTTP methods, route patterns |
| Parameters | query params, body fields, URL params, headers expected |
| Auth mechanisms | tokens, cookies, session logic, OAuth flows, API keys |
| WebSocket events | event names, channels, message schemas |
| External calls | fetch/axios URLs, third-party APIs, webhook targets |
## 3. Hidden & Interesting Artifacts
Look beneath the surface for:
- Hardcoded strings: URLs, IPs, hostnames, ports, internal service names
- Environment variables referenced (process.env.*)
- Database schemas, table/collection names, field names
- Role names, permission levels, feature flags
- Debug/admin/test routes or commented-out functionality
- Error messages that reveal internal structure
- Regex patterns (what are they validating/extracting?)
- File system paths (uploads, logs, configs, temp dirs)
## 4. Data Flow Map
Trace how user input moves through the code:
- Entry point (where does external data come in?)
- Transformations (parsing, validation, sanitization, or lack thereof)
- Storage (where does it end up: DB, file, cache, external service?)
- Output (what gets returned/rendered to the user?)
## Formatting Rules
- Use tables for structured data (endpoints, params, env vars)
- Use code snippets with line references for each finding
- Flag anything that seems intentionally obscured or unusual
- If the code is minified/obfuscated, note patterns and attempt to
identify the original framework or library
---
Here is the code:
English
Divyanshu Kothari retweetledi
Divyanshu Kothari retweetledi
Divyanshu Kothari retweetledi
Divyanshu Kothari retweetledi

I have been doing bug bounty since 2011 and ran a program for a multinational bank. Put everything I've learned into bugbounty.info. Target selection, recon pipelines, chain patterns, report templates, the business side. Free, no paywall, no course upsell.
English
Divyanshu Kothari retweetledi

Still no internet service recovery and no response from Tikona.
Today marks 12 days without internet, despite multiple complaints via email, app, and WhatsApp.
This is unacceptable service and complete negligence.
Requesting urgent intervention from @TRAI @DoT_India
English

@TikonaTIL
Internet not working for 9+ days despite complaints via email, app & WhatsApp.
On day 3, Tikona cited “network outage” & promised an update in 24 hrs—no update since.
Misleading & unacceptable.
Complaint: 1-10829824599 | User ID: 1127884030
Requesting @Trai to look
English

@Rosterrrrrrrrr @Real_Nishtha @AshwiniVaishnaw @DoT_India @bajpai_prakash @TikonaTIL Hey I am facing same issue i have 3 months left until renewal did you send disconnection request of your tikona connection?
English

@Real_Nishtha @AshwiniVaishnaw @DoT_India @bajpai_prakash @TikonaTIL I also face issue and more than 01 yr they harass like this and now no reply . What you do finally
English

@AshwiniVaishnaw @DoT_India @bajpai_prakash @TikonaTIL is running scams and extracting money by threatening people with lawsuits, when they request disconnection. I have not used their services since July 2023 and they made me forcefully pay money. Many such cases but no help.
English

@TikonaTIL I cannot access internet from past 3 days I have filed numerous complaints no response from you side just automate reply I can't login through otp in your selfcare.tikona.in website nor it is allowing me to reset my password give me solution
English
Divyanshu Kothari retweetledi

Walk into any Indian supplement store.
You: “I want whey protein.”
Them: “You also need:
Pre-workout - ₹2k
BCAA - ₹2k
Fat burner - ₹2k
Multivitamin - ₹1.5k”
The Indian supplement industry is a legal scam. Here’s what you ACTUALLY need:
1.Whey protein.
Not because it’s magic. Because most Indians eat 40g protein when their body needs 100g. Whey fills the gap. That’s it. Food in powder form.
2.Creatine.
Most researched supplement on the planet. Improves strength. Improves recovery. Costs a fraction of what that fat burner costs. But nobody pushes it because it’s boring and it works.
3.Vitamin D.
70-100% of Indians are deficient. You’re indoors 12 hours a day. Your body is running on empty. One blood test will confirm it.
4. Fish oil / Omega 3.
Most Indians don’t eat enough fatty fish. Good for your heart. Joints. Brain. Simple. Cheap. No flashy label needed.
That’s it. 4 things.
Now here’s what you DON’T need:
1. BCAA - if you’re eating enough protein, BCAAs are useless. Your whey already has them. You’re paying twice for the same thing.
2. Fat burner - no pill burns fat. None. If it did, nobody would be overweight. You’re paying ₹2,000 for a placebo with a six-pack on the label.
3. Testosterone booster - ashwagandha mixed with filler. Get your levels tested first. If they’re actually low, no supplement is fixing it. You need a doctor, not a tub.
4. Pre-workout - it’s caffeine in a fancy tub. Have a black coffee.
Get your blood work done first. Then decide what your body needs.
English